Today's HOT includes 66 victims by the notorious Black Suit, Akira, BianLian, DarkVault, Play, RansomHub, INC Ransom, Qilin, Abyss and LockBit 3.0 gangs. The average...
Read MoreThe WereWolves ransomware group has been recently added to our database, and a first look at it’s data leak site reveals that 21 victims have been listed; 14 located in Russia along with another 7 across the USA, France, Netherlands, Germany, Serbia and Macedonia, apparently targeted between May 18th and November 2nd, 2023.
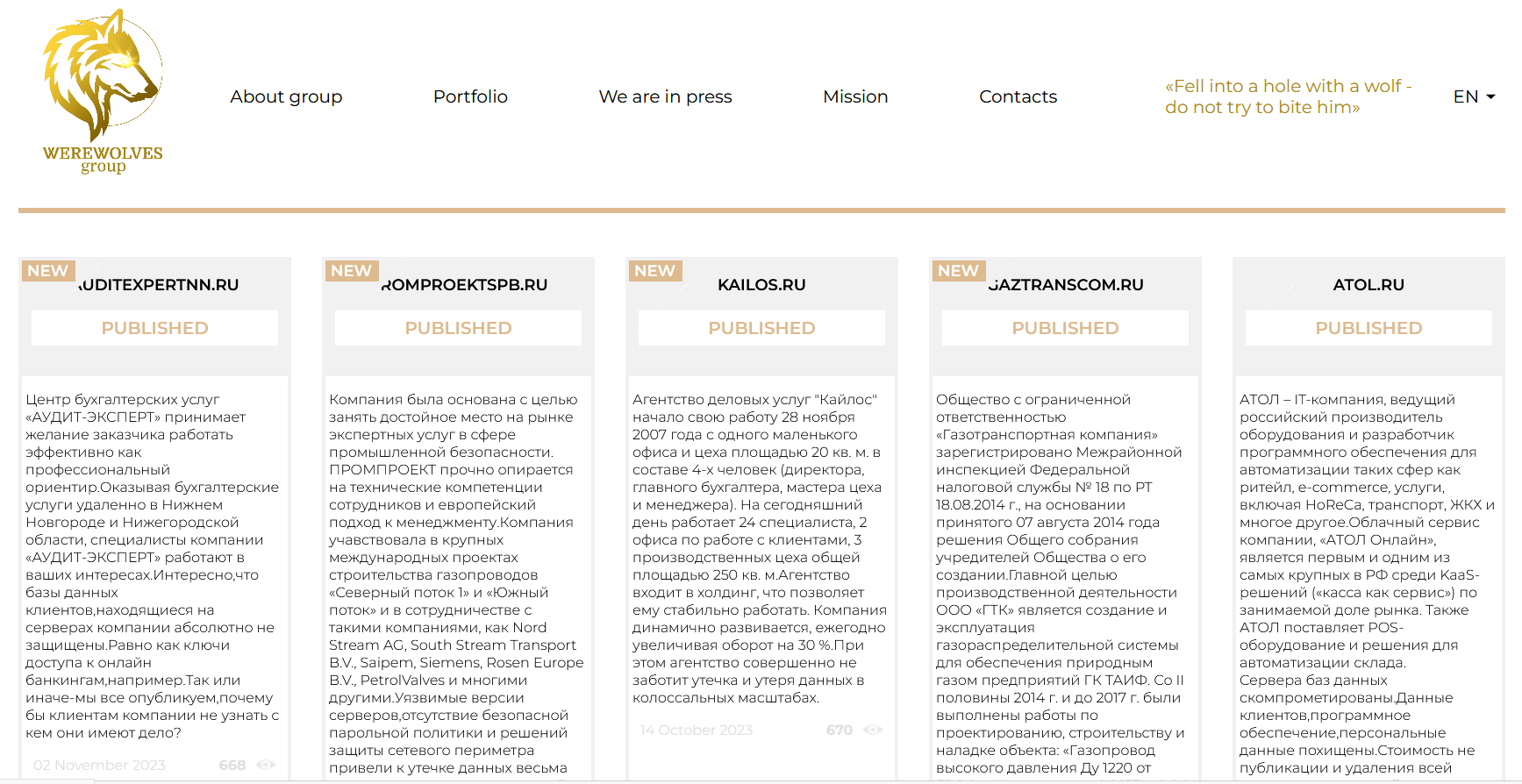
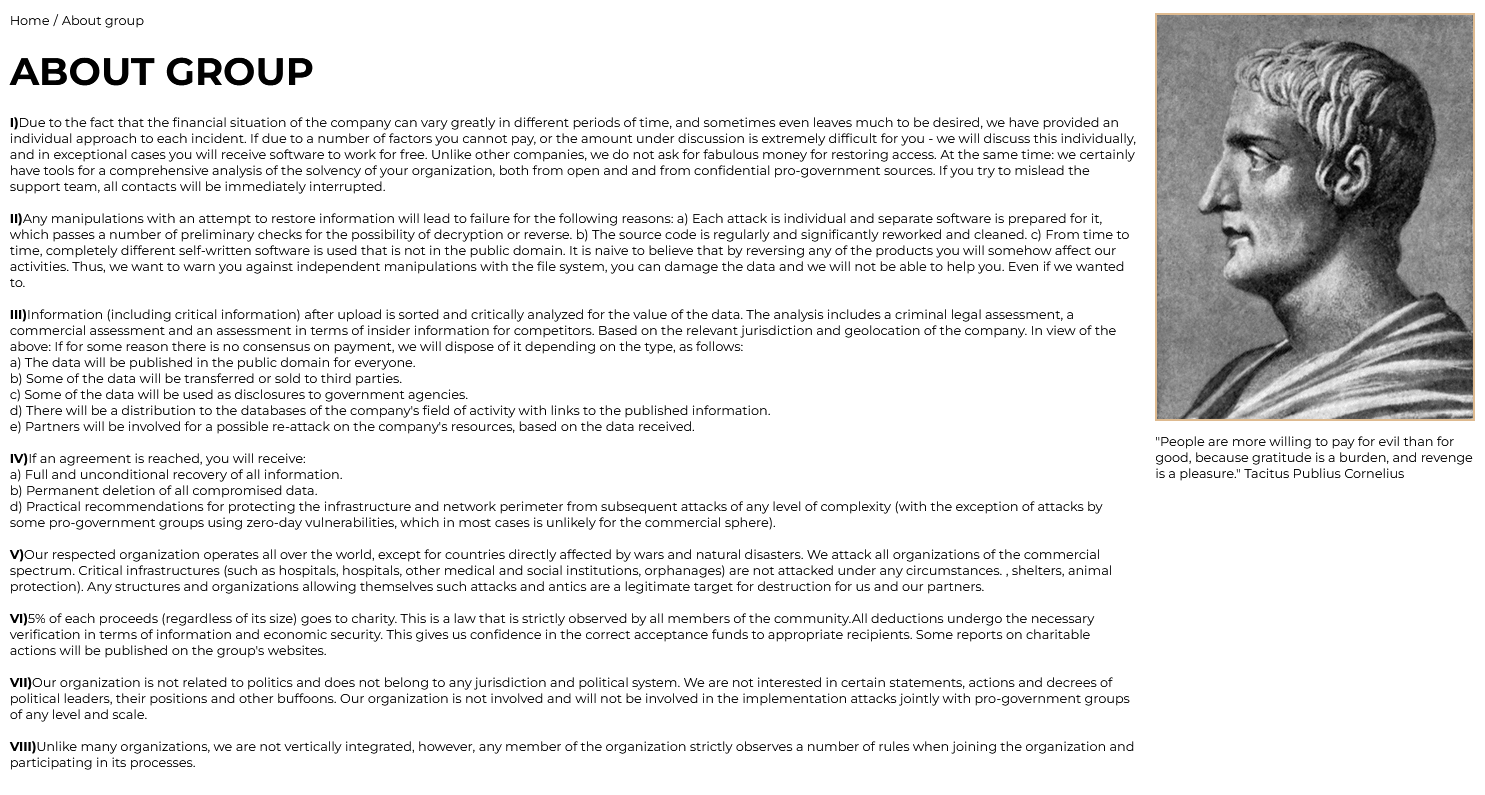
In the “About Us” section, the group portrays itself as an organization committed to cyber attacks and ransomware operations, offering tailored negotiations for data recovery while threatening of punitive measures if agreements are not met. Their “Mission” section states the following: “We see our mission in strengthening the cyber immunity of companies around the world, and this is definitely worth the money.”
Additionally, they feature a “Portfolio” section inviting security researchers, ethical, and unethical hackers worldwide to join their bug-finding bounty program. This program focuses on website vulnerabilities, doxing, software vulnerabilities, TOX vulnerabilities, unique ideas, and TOR vulnerabilities, with bounties ranging from $1,000 to $1 million.
Seeking public attention, the cybercrime group has published a 2022 article from Ghana Business News, claiming responsibility for an attack on the Electricity Company of Ghana (ECG). Following a ransomware attack, ECG was reportedly unable to buy power, resulting in several days of power outages.
Their blog also includes a recruitment call for new members with hacking skills. They promise flexible working hours, regular salary, and training, targeting both seasoned hackers and those with knowledge but less practical experience. A deposit of 1 Bitcoin is required as a security measure to deter unsuitable candidates like law enforcement or journalists. Applicants must demonstrate their hacking prowess and readiness to commit to cyber attacks immediately upon joining, with the organization emphasizing a structured recruitment process focused on skills, experience, and dedication to their illicit activities.
Although the last recorded activity was on November 2nd, by looking at the timeline of their attacks the group is likely to be still active, requiring a continuous monitoring.
An analysis of the attacks published by WereWolves provides us with an overview of the types of targets affected:

With 28.6%, the Professional/Scientific/Technical sector secures the leading position, closely followed by both the Financial/Insurance and Hospitality sectors, each holding a share of 14.3%. Subsequent to these are the WholesaleRetail, Telecommunications, and InformationCommunicationTechnology sectors, each accounting for 9.5%. Finally, the Manufacturing, EnergyUtilities, and OtherServices sectors each comprise 4.7%.
Interestingly, among the victims listed on the blog, 6 appear to be copy-pasted from attacks previously conducted by LockBit (Agency for Electronic Communications, Metalnet, Interfides, La Poste Mobile, Emprint, Big Centers). The posts for these 6 victims indeed showcase identical samples and the same amount of data exfiltrated.
Other impacted companies have captured our attention, this time for the extreme quantity of data that WereWolves claims to have exfiltrated. In the post detailing the attack on Maritime Bank, the cybercriminals assert that they have exfiltrated 120 Terabytes of data, and for CarMoney, 60 Terabytes. This volume of data is rarely seen even among the largest criminal organizations. As always, these statements are pending confirmation.
According to experts from the Digital Forensics Laboratory of F.A.C.C.T., the ransomware group WereWolves primarily targets victims’ poorly protected public services as their initial attack vector. They encrypt company data using a version of the LockBit3 (Black) ransomware program. This particular version is compiled from a builder that has surfaced in the public domain. In their operations, WereWolves also utilize the leaked tools of the notorious cybercriminal group Conti, known for having over 850 victims including corporations, and government agencies.
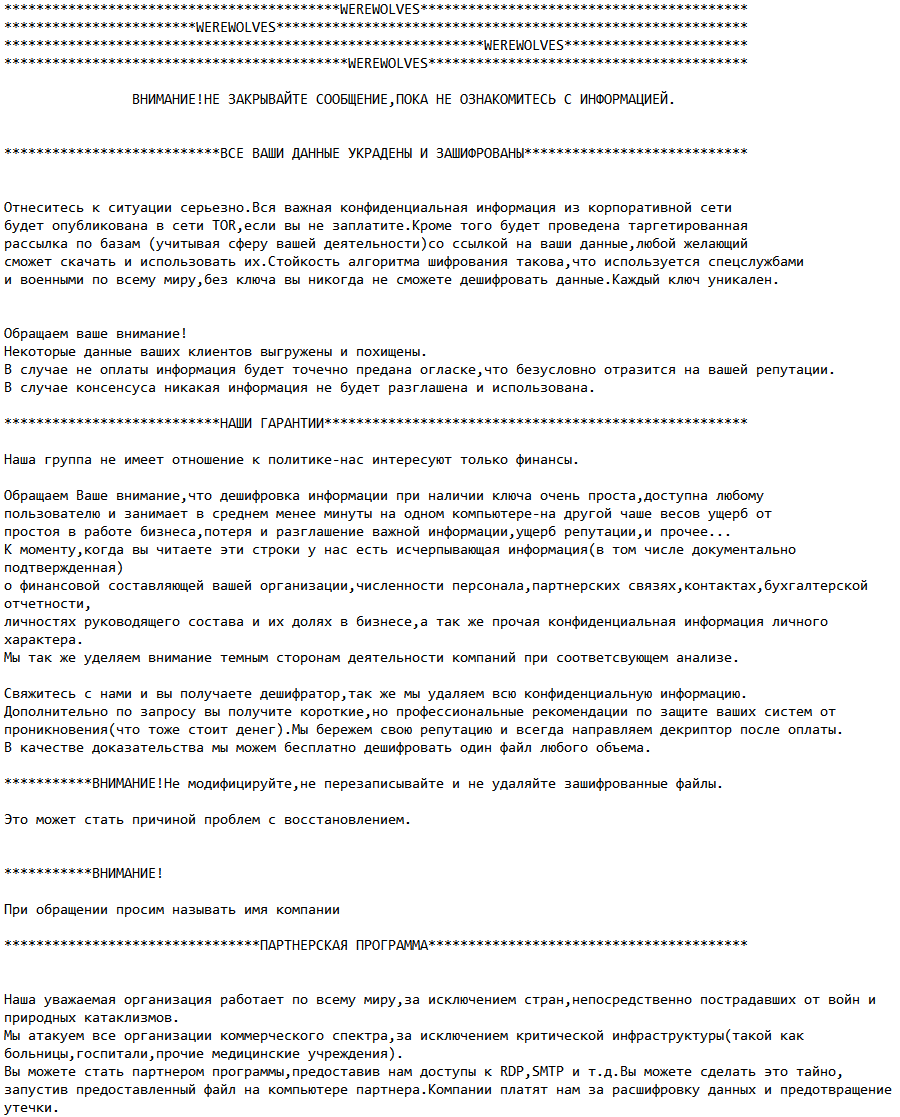
Furthermore, WereWolves is known for its adoption of the ‘double extortion‘ tactic. This approach involves not only demanding a ransom for the decryption of data but also posting sensitive data about non-compliant victim companies on their own Data Leak Site (DLS).
BIG Centers, Agency for Electronic Communications, Metalnet, Interfides, Easy Loan, QB2B, Emprint, La Poste Mobile, acac Fitness & Wellness, AMAKS Hotels & Resorts, Aurora Store, AMAKS Congress Hotel Khabarovsk, Maritime Bank, CROC Incorporated, CarMoney, RoomHotel, ATOL, Gas Transportation Company, Kailos, Promproekt, Audit-Expert.
Confirmation or denial of WereWolves’ attacks would be a decisive factor in assessing the actual threat posed by this ransomware group, which until now has remained in the shadows. Moreover, given the 6 attacks coinciding with those of LockBit, an affiliation between the two criminal gangs cannot be ruled out. Continuous monitoring will reveal the true nature of WereWolves.
Victim website: | bigcenters.rs |
Victim country: | Serbia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Financial documents |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | aek.mk |
Victim country: | Macedonia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 118 GB |
Exfiltrated data type: | Financial documents, PII, credit cards, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | metalnet.nl |
Victim country: | Netherlands |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 49 GB |
Exfiltrated data type: | Technical designs, invoices and financial documents, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | interfides.de |
Victim country: | Germany |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Projects, financial data, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | lzaim38.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 45,000 |
Exfiltrated data amount: | Miscellaneous documents including passports and photos, etc. |
Exfiltrated data type: | N/A |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | qb2b.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 16,300 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including scans and passports, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | emprint.com |
Victim country: | USA |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: |
Victim website: | lapostemobile.fr |
Victim country: | France |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 3 |
Image: |
Victim website: | acac.com |
Victim country: | USA |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: |
Victim website: | krasnoyarsk.amaks |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 4,000 |
Exfiltrated data amount: | 1.0 TB |
Exfiltrated data type: | Miscellaneous documents including videos and photos, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | avrora24.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 130,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: |
Victim website: | habarovsk.amaks |
Victim country: | N/A |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 3,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including videos and photos, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | maritimebank.com |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 1,000,000 |
Exfiltrated data amount: | 120 TB |
Exfiltrated data type: | Clients’ data |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 5 |
Image: |
Victim website: | croc.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 170,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | carmoney.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 60 TB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 5 |
Image: |
Victim website: | roomhotel-sochi.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: |
Victim website: | atol.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 450,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Database, clients’ data, personal data, software data, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 5 |
Image: |
Victim website: | gaztranscom.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 60,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Clients’ data |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | kailos.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 6,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
Victim website: | promproektspb.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Clients’ data |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: |
|
Victim website: | auditexpertnn.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Clients’ data |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
Stay Cyber Safe!
Today's HOT includes 66 victims by the notorious Black Suit, Akira, BianLian, DarkVault, Play, RansomHub, INC Ransom, Qilin, Abyss and LockBit 3.0 gangs. The average...
Read MoreToday's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
Read MoreToday's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
Read More
-----BEGIN PGP PUBLIC KEY BLOCK----- xsFNBFyONI0BEAC3wJRo5qhtr1KsqVdMz7b5JqHmt7H0ZZr14oJ9TV/hD9LMfrKpnQ94dFGnpfGa BKC1wSoJN4Yfs5lg5YmN4hmHmm6PkjgQdenVgL4YDfLDodwn5DgXKuywRBqIFbbnTDvFAb03DX2A FPnc+4g2QHsfiFycz+ISg/Z+8i21gY3j5oZlrdMKVWrNczrNc/lDJqJ36RSYDn1QzAW1ZGY/pUXk imPRvLew5Idr3462sZVVhuUFMD3Uf/W1SaS3bSEQM89pSYKZfo8AFpAs659Mn7gqKru6ndxilRdF wJGQuepqR8kz+vVPLyxJj68ii2ZBIY50RQvSBgJRnNF/Htp30cuk3v8jfSGZit9XYTTGQThVbfGR ZcKWze/iF+es110+mNXA/8s7jKs95PI+z1Foc9o74Ujs8dvjEGHTaESIEzX3JtEZUCZUiPt/P8pU Jw0ewbj1XCacYxYVsR7ODlf6GEsjt868WcjiqsuuZo2rzO4og9hFU5DlBzuePklfhw8dO5CiMN2H vtSkAn4DkgHqC+JiciHc9h5Cvvfjp52oQPj1eYmU3LkOvGFmPXVIts3VfxsQT3gk+DmrQ4J//fAl tNRSbMBnGu5F/qnLLkJmKRKPKNNcpjptFznKxLZbxW5QbAeDok3ho8YQACfADKcrmaIRkoPr8/mn PxZgMSMB87W7sQARAQABzSRTb2ZpYSBTY296emFyaSA8c29maWFAaGFja21hbmFjLmNvbT7CwZQE EwEIAD4WIQTNwEbcXbH0vegGlHCd6fr0nsTifwUCXI40jQIbIwUJEswDAAULCQgHAgYVCgkICwIE FgIDAQIeAQIXgAAKCRCd6fr0nsTifwKuD/4+3MaN+9eFiltI06fFBjr1Csh0OLFw89jFnpuYl9Sm ImVqmBwrnm+APxxLK4M+FMuNm4fW08X249t09Nsf0ba6UJ0HR/7/fRTipjzRLqHSr0+ZjVUGHhon fuuFZgNzPA5RmQZZCyiwyqZJs7pLn1QI/CtlDP6MsQhadywbkO/5LlDoBoYh/2DYNA/mtEfJbvc/ cOvfk47thj5OzcXJEWFxz7h2P5C2ELwxdhNPC+uqcOQkTScnuIBJooheJPhdmqOtOwrbUUIfaryM IESrol3Jg3/MUOe7FLXhwCSQGY1iefzl4py2jTeK936GMBHifLSUCA88lpE7ALkbf3+qJ9ABra9G e9e0dirIlPvFgBkEBBXsoIReQLrhHKFBtvKdrrE9Rb7kAwon+sW+3Uf6Ie3M8nTisGy2AmlI/tQ5 V0MHU2UJUNcc59hk7ADIlXN64eeqELgsMtlR4wEHd6nwcEpoPCTWfrVSwzsPtXUGNAGbgGxISv/F ltcFJ6Qw6Zy4f+YBEyCx/7GA3kjLllkcHv4kwHpP+WQCzbjh2JdkGEp5AY7puil1AtOFcbirbHbR 83KVeqx4Vvlyh2jhIDQYB/9qpTDC1xDKpndn40gnNd5hvjK0I0Xvbhb0PLhCpJQ5tsvPiQHjhOMF Wye3ZigaX1gTZxE29MLtwBbOYdGCYG0MrM7BTQRcjjSNARAAupAKTZXLRktriUVqhkZpU8zUVwrW ik6siStg7BppSJuKVW+Ic8QIagW0I48d2jZIIXrQRvqVBixn8eeBTE8Cujum1mZyhTw2sri3gE9i 81gisF17T/uewzRyYwx8obMfSEBnwJa44td7VjtbfLMRtfneK9R40+kELhhvXZa3DBbcG86zHVPU f1YkLX4RNSyjz4vOCX3WlcIAOr6MJA8DT+F5mUCVEhnkeUbflXtxRSeTUTfOw/3MYLs+mc6hWwLq gqTMcIQhDrYEY5wUgb5Mj86NR/uvsThL6MtWCJWVbfxHxM575woyTdD9E6HGO6loHYdky/7I+XFZ twgxsGn6HJYT+Gwn9BI5/DiwT1Qb/AyADktN1jGmZGTlniS+hly7rm0EHb2CTTM5zT1fh/sCOtQb nYIUf2in2cIfcFvzeFrUbDk2HfJMp5FmY6tBEV5xyNCww/mBkW2nuZy9CvAheJEOGoO8lyonPU2u ARq345LdbS6l+VdivPmZoLNpIMRw9MSTYmzm08h7C+/6hxzpjw1/nWZ+W2k9VpLutEs7KMtsbZR4 WhVFVS1uhqxrnjoeBHznh360Ou8SR+PFO0HIrYz4W7ayfcBhqcsGrM9u1E892gjUVTbPv8UoXQ8S Zm9ra2jqbfZGbyOpMIlyMzHTak7r0IZvCedEUDCimitbw98AEQEAAcLBfAQYAQgAJhYhBM3ARtxd sfS96AaUcJ3p+vSexOJ/BQJcjjSNAhsMBQkSzAMAAAoJEJ3p+vSexOJ/C+wP/iGvKG1NldCT2gR7 oWhmvgBnsD7qjC57RX0Go7WD1lmrWP4xWpvM6Tj0V4ZsXnyB8zUR38p49PPymjwy51FAss5PYh8S bVC1/sKC5Sae3kiAoMGH29MBAwL1IkJ8PNw6uOJHhUIJgKT5RWk2f7q3+Tha19slXwD/FC1IcBJK baxyVkG3cG5AnNvvKZyFAUNZ9FiBycaNHO4o6bCcCzSsaRLL2azudJLrF8UYPfTNBQ6Cr4QLqaRb t+ZqL2nqmcadO1AtxLtq5lQjxbhJ3jSYIcQJRq0ztbIBcPrdR2B/dfVED9cU5leSmNXxrh09gJ7N tmUpVo5fBcbf6fP7h2HIFBpH+G/8UUlcbm9pQ5Jcb8FEom0JrfaIAuv1gEIJAk1mkqLNzWUs8KuL nCBBVT2+2hfEZjtjUYbCLVB4LRCsLs9CY1wS3yKca90S8m0tfKcSj3K3k8qlKodkE2raX2GW2dm9 b200ENbb41B1uZlPts4Yh/AMfLqoNv8wyw0GlUQ2DqgDqviLANYbg4/GHwTLwO2b9UMHuTVU3woS 1LRKt0iPPsd+ir+9YRAVt5LB5XTS5C5cdIW9JSXQ+0cnbr3LPZCBulOew/M72liBINKWKGoUyueF 73ckNO9S7pzTOCpjn3+gAuzN/itwgwrMLoqUqqBuxzd7cKNJHTFdTIfTm53f =KIMs -----END PGP PUBLIC KEY BLOCK-----