news
HACKS OF TODAY 03-04-05/01/2024

Today’s HOT includes 14 victims by the notorious LockBit 3.0, BlackBasta, Play, Black Suit, Hunters International, Monti and ALPHV/BlackCat gangs.
The average Cyber Risk Factor is 4.1.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
PARK HOLIDAYS
Victim website: | parkholidays.com |
Victim country: | United Kingdom |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 515 GB |
Exfiltrated data type: | Finance, insurances, 1099 info, users’ personal documents including DL, SSN, passports, etc. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
TEACHING COMPANY (dba THE GREAT COURSES)
Victim website: | thegreatcourses.com |
Victim country: | USA |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.3 TB |
Exfiltrated data type: | Accounting, HR, 401(k), users’ personal folders including passports, DL, SSN, confidentiality agreements, etc. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
SAED INTERNATIONAL
Victim website: | saed.sa |
Victim country: | Saudi Arabia |
Attacker name: | ALPHV/BlackCat |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
GROUPE IDEA
Victim website: | groupe-idea.com |
Victim country: | France |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 22nd Jan 24 |
Cyber Risk Factor: | 4 |
Image: |
MADISON CAPITAL
Victim website: | madisoncapital.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients’ documents, budget, IDs, payroll, Insurance, taxes, finance information, etc. |
Leaked data: | / |
Ransom deadline: | 5th Jan 23 |
Cyber Risk Factor: | 4 |
Image: |
WPM REAL ESTATE MANAGEMENT
Victim website: | wpmllc.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients’ documents, budget, IDs, payroll, Insurance, taxes, finance information, etc. |
Leaked data: | / |
Ransom deadline: | 5th Jan 23 |
Cyber Risk Factor: | 3 |
Image: |
THE TIME GROUP
Victim website: | thetimegroup.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients’ documents, budget, IDs, payroll, Insurance, taxes, finance information, etc. |
Leaked data: | / |
Ransom deadline: | 5th Jan 23 |
Cyber Risk Factor: | 3 |
Image: |
KERSHAW COUNTY SCHOOL DISTRICT
Victim website: | kcsdschools.net |
Victim country: | USA |
Attacker name: | Black Suit |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 17.5 GB |
Exfiltrated data type: | N/A |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
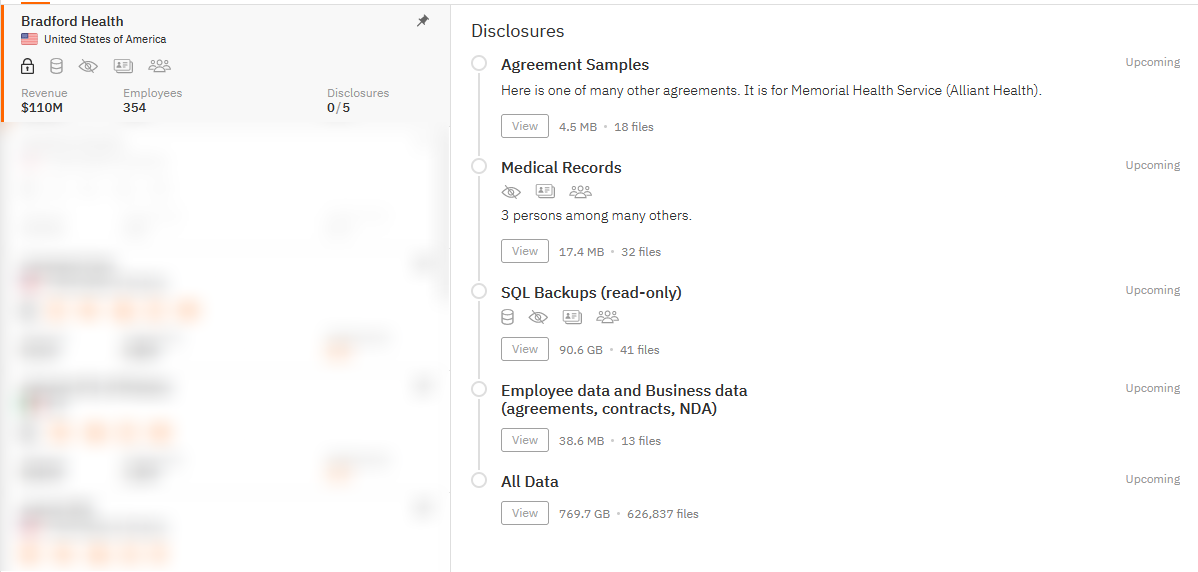
BRADFORD HEALTH CARE
Victim website: | bradfordhealth.net |
Victim country: | USA |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 769.7 GB (626,837 files) |
Exfiltrated data type: | Agreements, medical records, SQL Backups, employee data and business data, etc. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
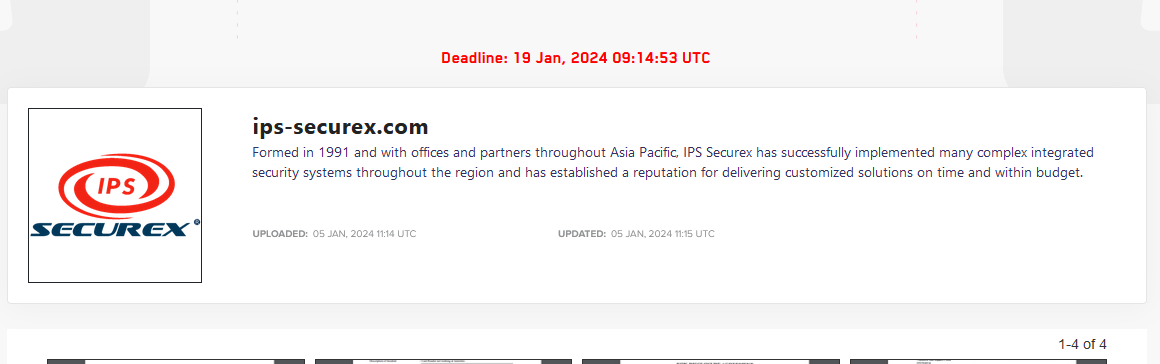
IPS SECUREX
Victim website: | ips-securex.com |
Victim country: | Singapore |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Reports, non-disclosure, and confidential documents, etc. |
Leaked data: | Sample |
Ransom deadline: | 19th Jan 23 |
Cyber Risk Factor: | 4 |
Image: |
DIABLO VALLEY ONCOLOGY AND HEMATOLOGY MEDICAL GROUP
Victim website: | dvohmg.com |
Victim country: | USA |
Attacker name: | Monti |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 30 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 28th Jan 24 |
Cyber Risk Factor: | 4 |
Image: |
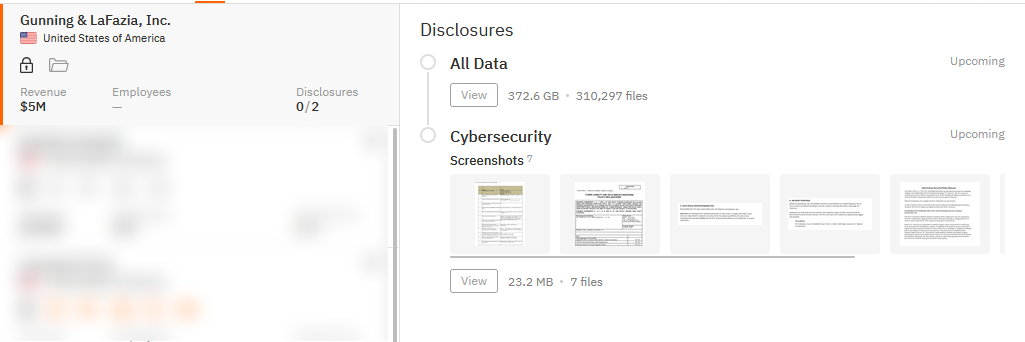
GUNNING & LAFAZIA
Victim website: | gunninglafazia.com |
Victim country: | USA |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 372.6 (310,297 files) |
Exfiltrated data type: | N/A |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
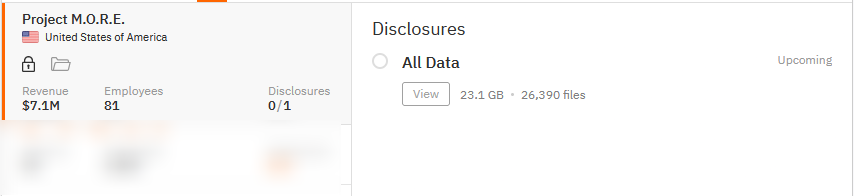
PROJECT M.O.R.E.
Victim website: | projectmore.org |
Victim country: | USA |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 23.1 GB (26,390 files) |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
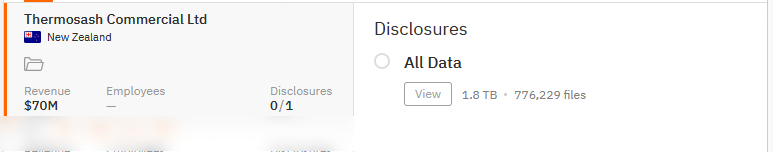
THERMOSASH COMMERCIAL LIMITED
Victim website: | thermosash.co.nz |
Victim country: | New Zealand |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.8 TB (776,229 files) |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
Stay safe!
Hackmanac Team!
Latest news
HACKS OF TODAY 08/05/2024
Today's HOT includes 20 ransomware victims by the notorious Metaencryptor, Qilin, LockBit 3.0, Hunters International, INC Ransom, RansomHub, Medusa, Black Suit, APT73 and dAn0n gangs....
Read MoreHACKS OF TODAY 07/05/2024
Today's HOT includes 66 victims by the notorious Black Suit, Akira, BianLian, DarkVault, Play, RansomHub, INC Ransom, Qilin, Abyss and LockBit 3.0 gangs. The average...
Read MoreHACKS OF TODAY 03-04-05-06/05/2024
Today's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
Read More