news
HACKS OF TODAY 29/02/2024

Today’s HOT includes 26 ransomware victims by the notorious BianLian, Mogilevich, Qilin, LockBit 3.0, RansomHouse, Trigona, Black Suit, 8Base, Medusa, ALPHV/BlackCat, Snatch, Abyss, Dunghill Leak, RansomHub, BlackBasta and Akira gangs.
The average Cyber Risk Factor is 4.5.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
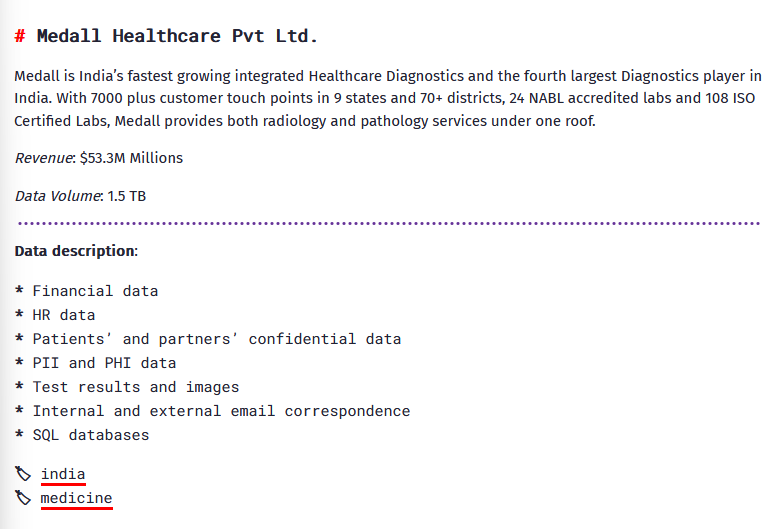
MEDALL HEALTHCARE
Victim website: | medall.in |
Victim country: | India |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.5 TB |
Exfiltrated data type: | Financial data, HR data, Patients’ and partners’ confidential data, PII and PHI data, Test results and images, Internal and external email correspondence, SQL databases |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
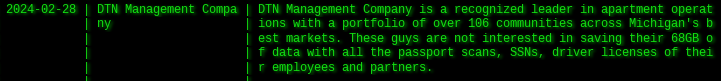
DTN MANAGEMENT
Victim website: | dtnmgt.com |
Victim country: | USA |
Attacker name: | Akira |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 68 GB |
Exfiltrated data type: | Passport scans, SSNs, driver licenses. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
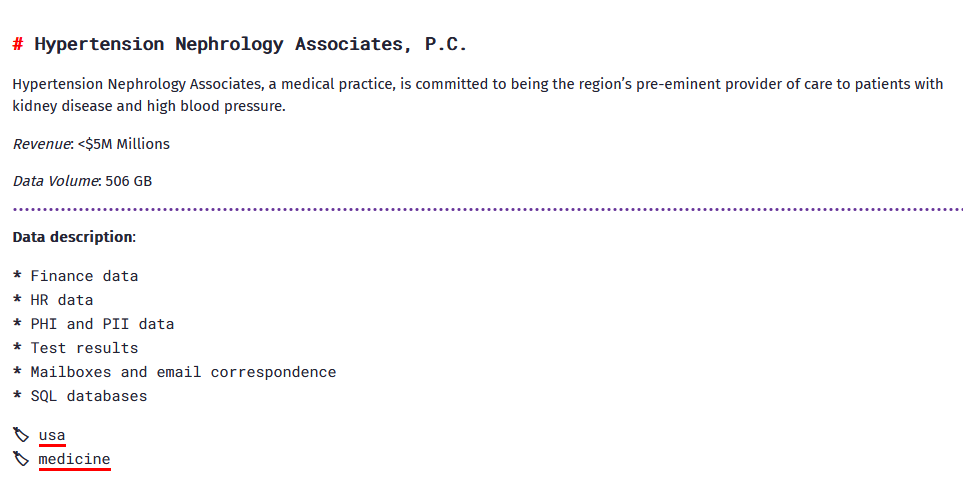
HYPERTENSION NEPHROLOGY ASSOCIATES
Victim website: | hypertensionnephrologyassociates.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 506 GB |
Exfiltrated data type: | Finance data, HR data, PHI and PII data, test results, mailboxes and email correspondence, SQL databases. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
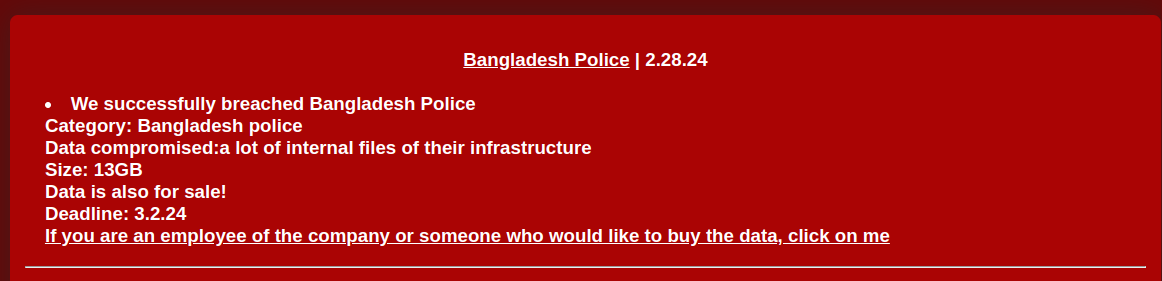
BANGLADESH POLICE BUREAU OF INVESTIGATION
Victim website: | pbi.gov.bd |
Victim country: | Bangladesh |
Attacker name: | Mogilevich |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 13 GB |
Exfiltrated data type: | Internal files |
Leaked data: | / |
Ransom deadline: | 03rd Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
ETAIROS HEALTH
Victim website: | etairoshealth.com |
Victim country: | USA |
Attacker name: | Qilin |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Financial data, confidential documents, personal documents, employees’ data, etc. |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
EASTERN SHIPBUILDING GROUP
Victim website: | easternshipbuilding.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Confidential data |
Leaked data: | / |
Ransom deadline: | 01st Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
HAL ALLERGY
Victim website: | hal-allergy.com |
Victim country: | Netherlands |
Attacker name: | RansomHouse |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 105 GB |
Exfiltrated data type: | N/A |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
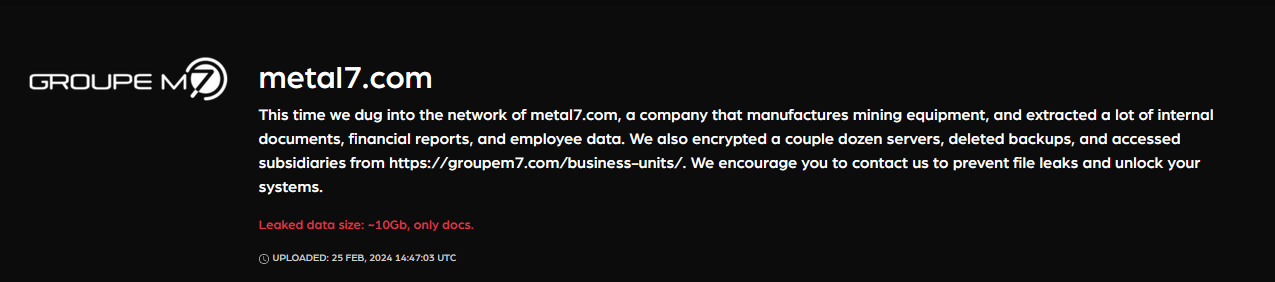
DINAMIC OIL
Victim website: | dinamicoil.com |
Victim country: | Italy |
Attacker name: | Trigona |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 5,000,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | Sample with Italian personal documents and other documents from the Indian branch Dinamic Oil India |
Ransom deadline: | 19th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
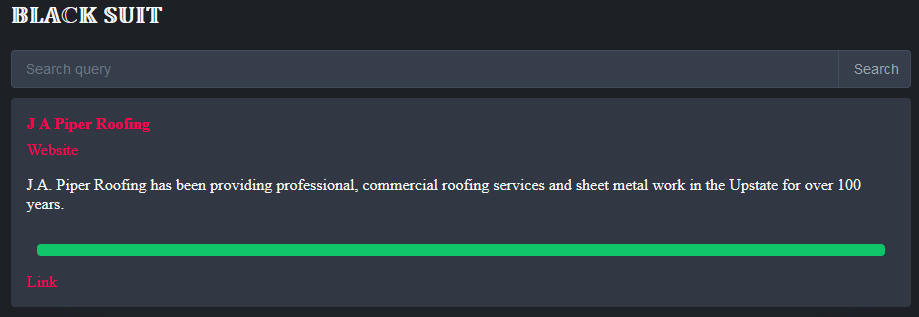
J.A. PIPER ROOFING
Victim website: | piperroofing.com |
Victim country: | USA |
Attacker name: | Black Suit |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 66.6 GB |
Exfiltrated data type: | N/A |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
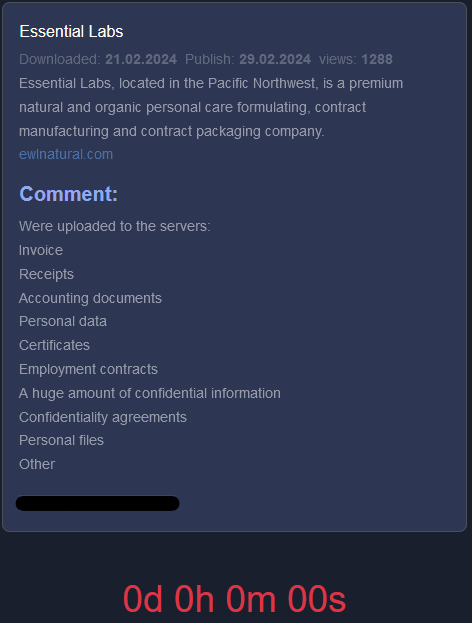
ESSENTIAL LABS
Victim website: | essentiallabs.com |
Victim country: | USA |
Attacker name: | 8Base |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 46.2 GB |
Exfiltrated data type: | N/A |
Leaked data: | Fully published |
Ransom deadline: | 29th Feb 24 |
Cyber Risk Factor: | 4 |
Image: |
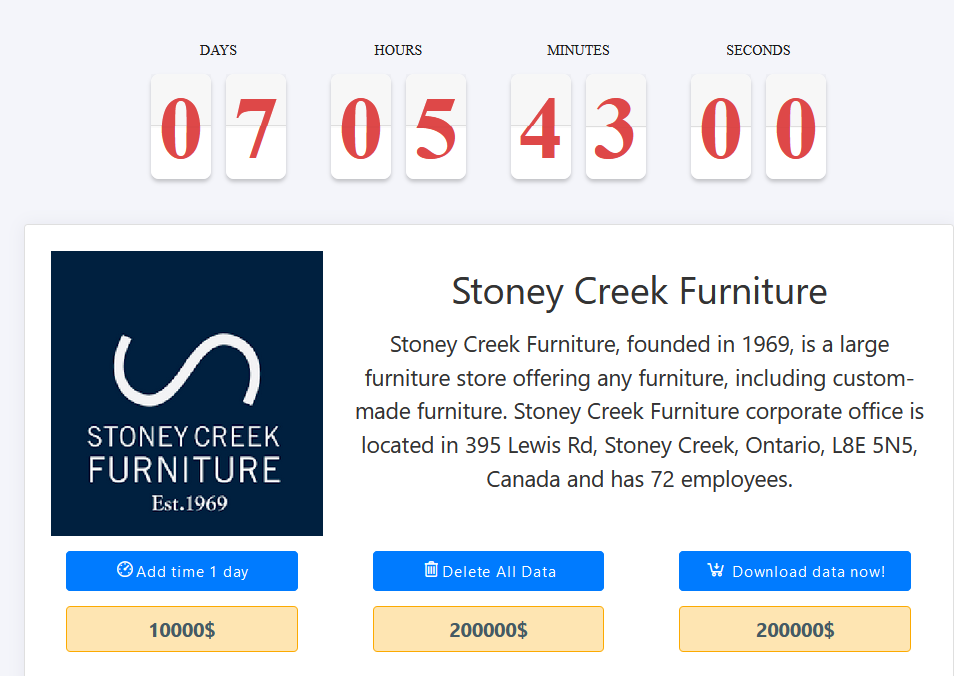
STONEY CREEK FURNITURE
Victim website: | stoneycreekfurniture.com |
Victim country: | Canada |
Attacker name: | Medusa |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 200,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents, financial, invoices, etc. |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
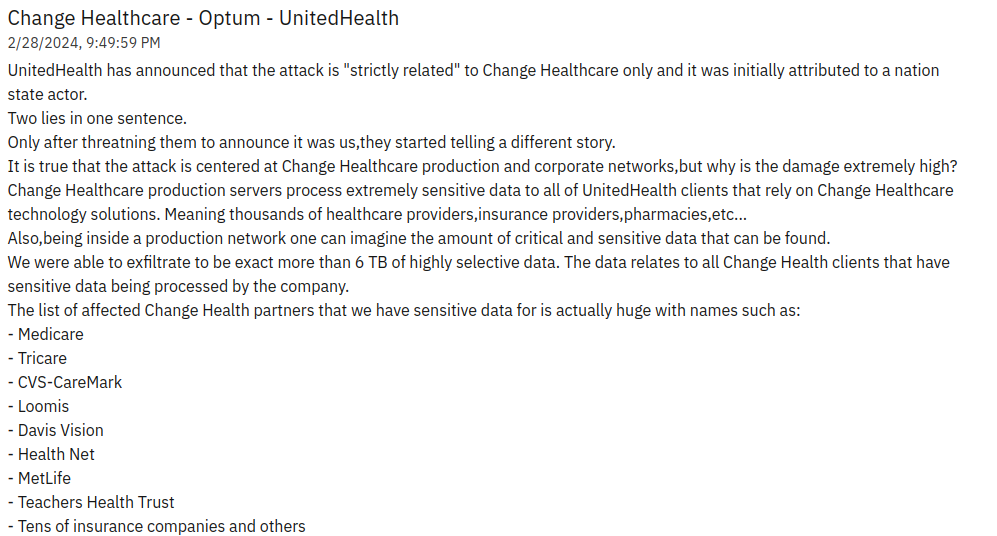
UNITEDHEALTH’S CHANGE HEALTHCARE
Victim website: | changehealthcare.com |
Victim country: | USA |
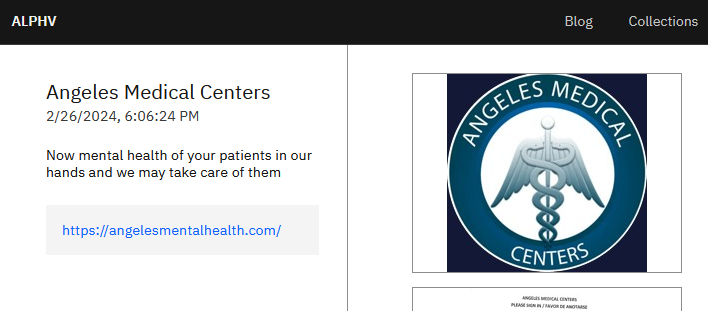
Attacker name: | ALPHV/BlackCat |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 6 TB |
Exfiltrated data type: | Sensitive company and partner data: Medicare, MetLife, CVS Caremark, Loomis, HealthNet, Teachers Health Trust |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
GAP SOLUTIONS
Victim website: | gapsolutions.com.au |
Victim country: | Australia |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 20th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
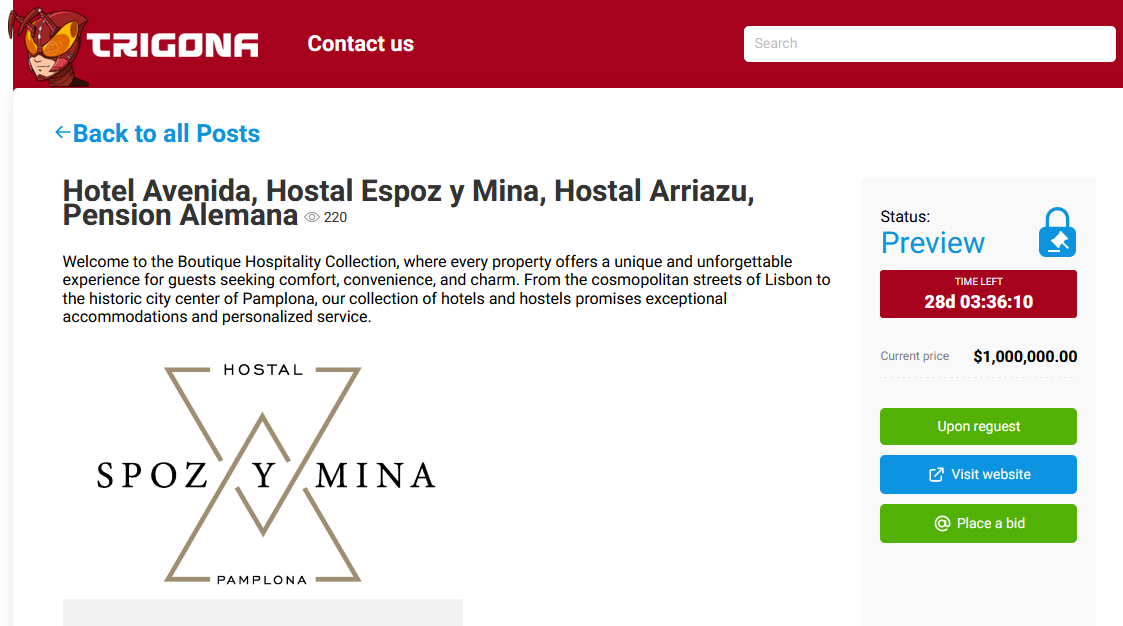
HOTEL AVENIDA, HOSTAL ESPOZ Y MINA,
HOSTAL ARRIAZU, PENSION ALEMANA
Victim website: | hotelavenidapalace.pt |
Victim country: | Spain |
Attacker name: | Trigona |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 1,000,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Scans of visitor documents and data. |
Leaked data: | Sample |
Ransom deadline: | 28th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
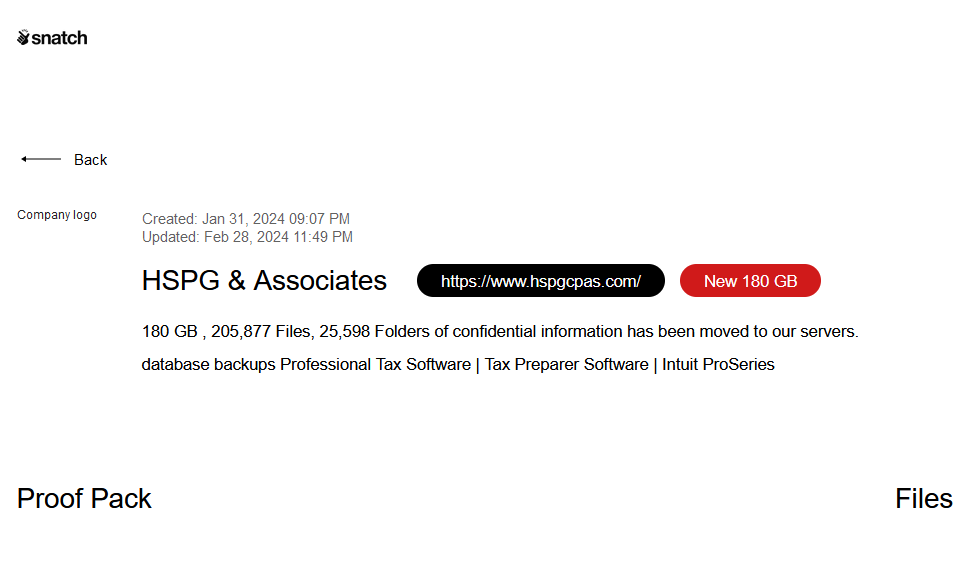
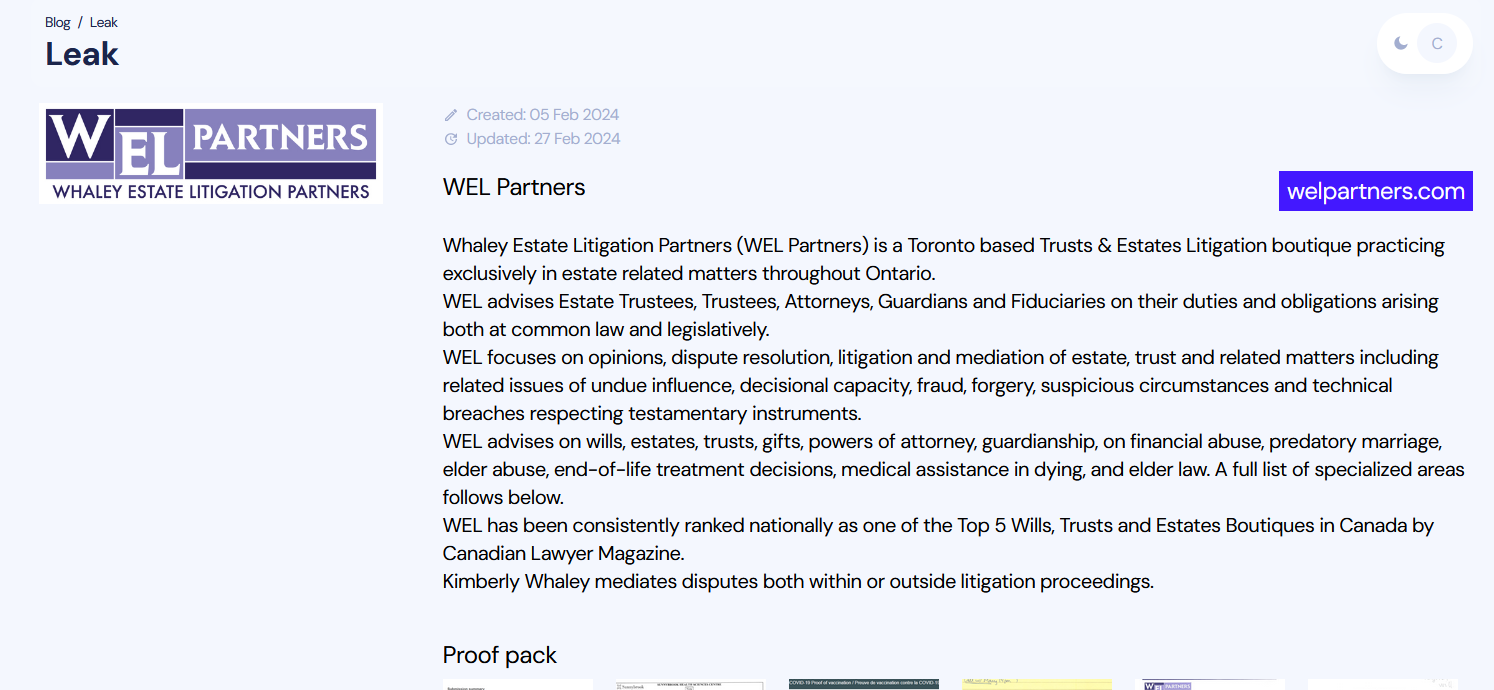
HSPG & ASSOCIATES
Victim website: | hspgcpas.com |
Victim country: | USA |
Attacker name: | Snatch |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 180 GB |
Exfiltrated data type: | Confidential information, database backups, etc. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
SUNHARBOR MANOR
Victim website: | sunharbormanor.com |
Victim country: | USA |
Attacker name: | Abyss |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 91 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 07th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
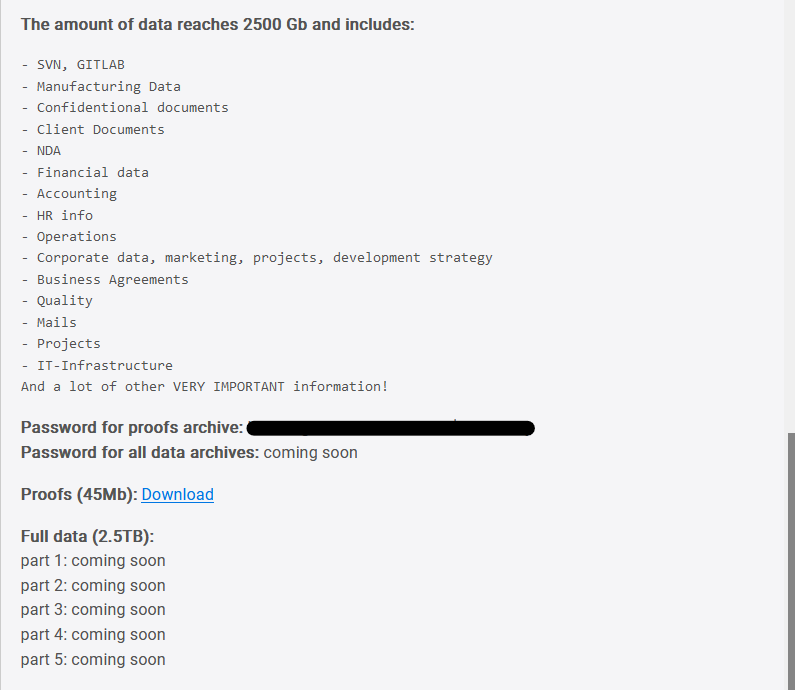
ARRAY NETWORKS
Victim website: | arraynetworks.com |
Victim country: | USA |
Attacker name: | Dunghill Leak |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 2.5 TB |
Exfiltrated data type: | SVN, GITLAB, Manufacturing Data, Confidential documents, Client Documents, NDA, Financial data, Accounting, HR info, Operations, Corporate data, marketing, projects, development strategy, Business Agreements, Quality, Mails, Projects, IT-Infrastructure, etc. |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
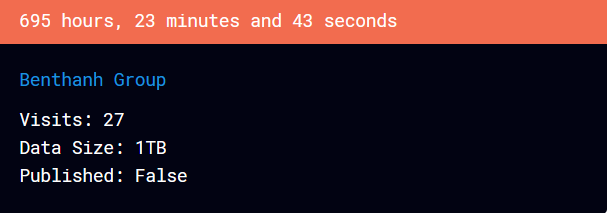
BENTHANH GROUP
Victim website: | benthanhgroup.com |
Victim country: | Vietnam |
Attacker name: | RansomHub |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1 TB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 29th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
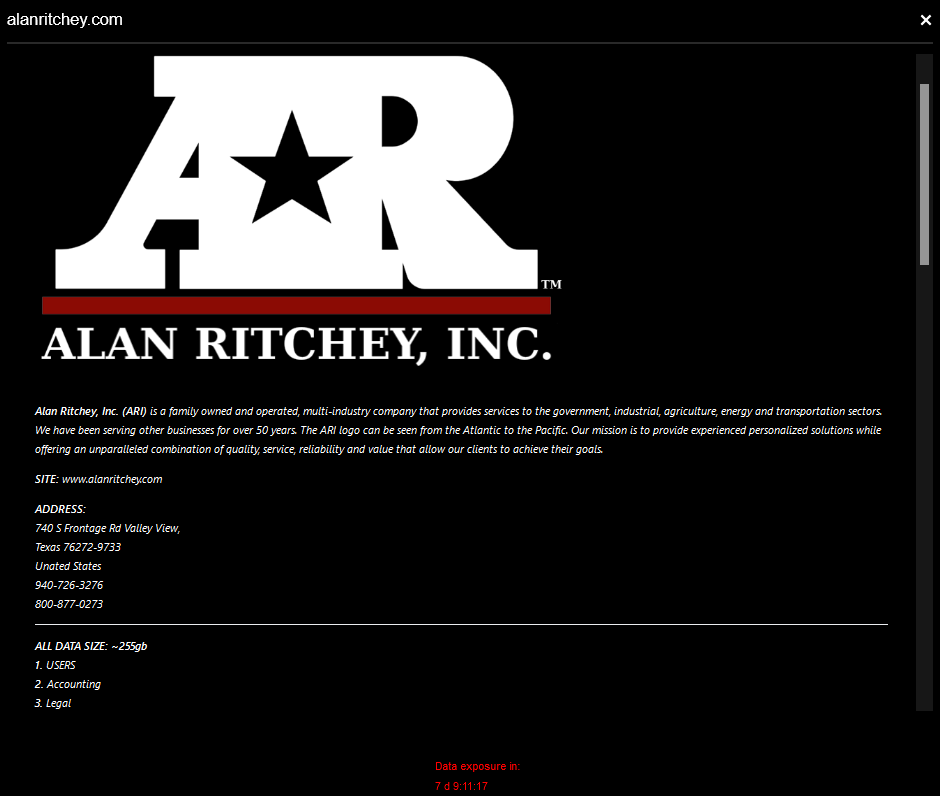
ALAN RITCHEY
Victim website: | alanritchey.com |
Victim country: | USA |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 255 GB |
Exfiltrated data type: | Users, accounting, legal, HR files. |
Leaked data: | Sample |
Ransom deadline: | 08th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
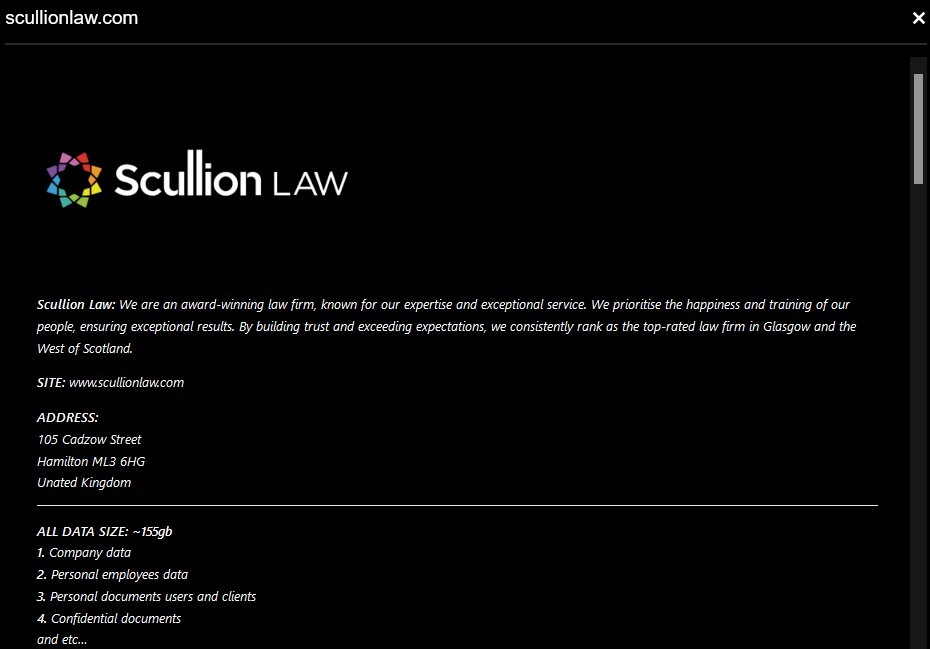
SCULLION LAW
Victim website: | scullionlaw.com |
Victim country: | United Kingdom |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 155 GB |
Exfiltrated data type: | Company data, personal employees data, personal documents of users and clients, confidential documents, etc. |
Leaked data: | Sample |
Ransom deadline: | 08th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
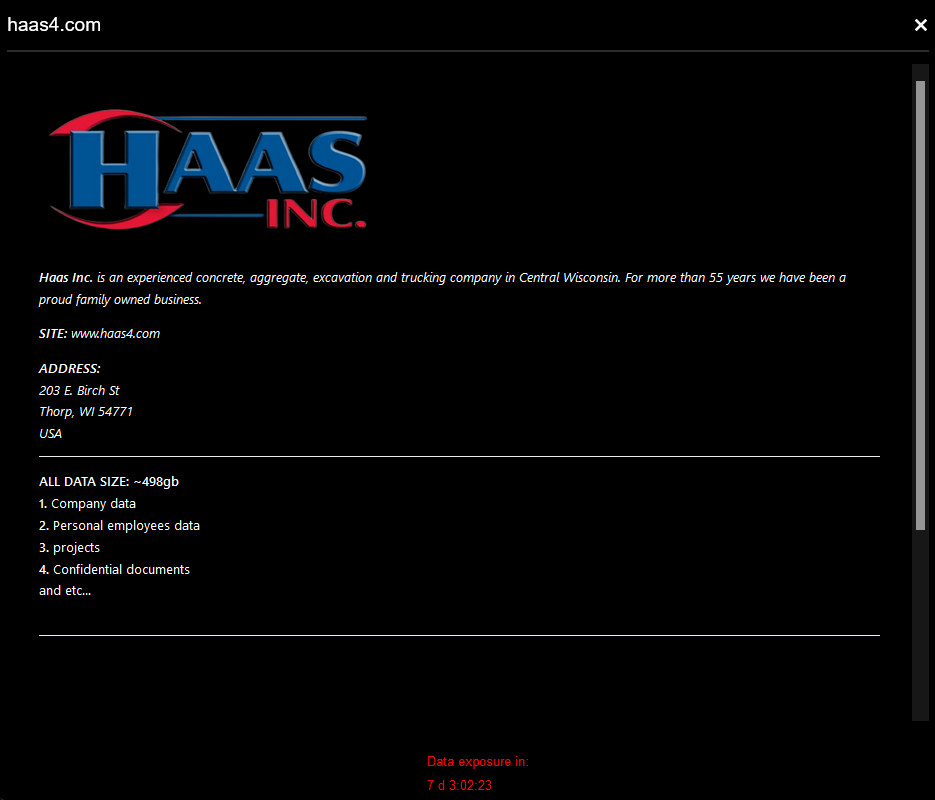
HAAS INC
Victim website: | haas4.com |
Victim country: | USA |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 498 GB |
Exfiltrated data type: | Company data, personal employees data, projects, confidential documents, etc. |
Leaked data: | Sample |
Ransom deadline: | 08th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
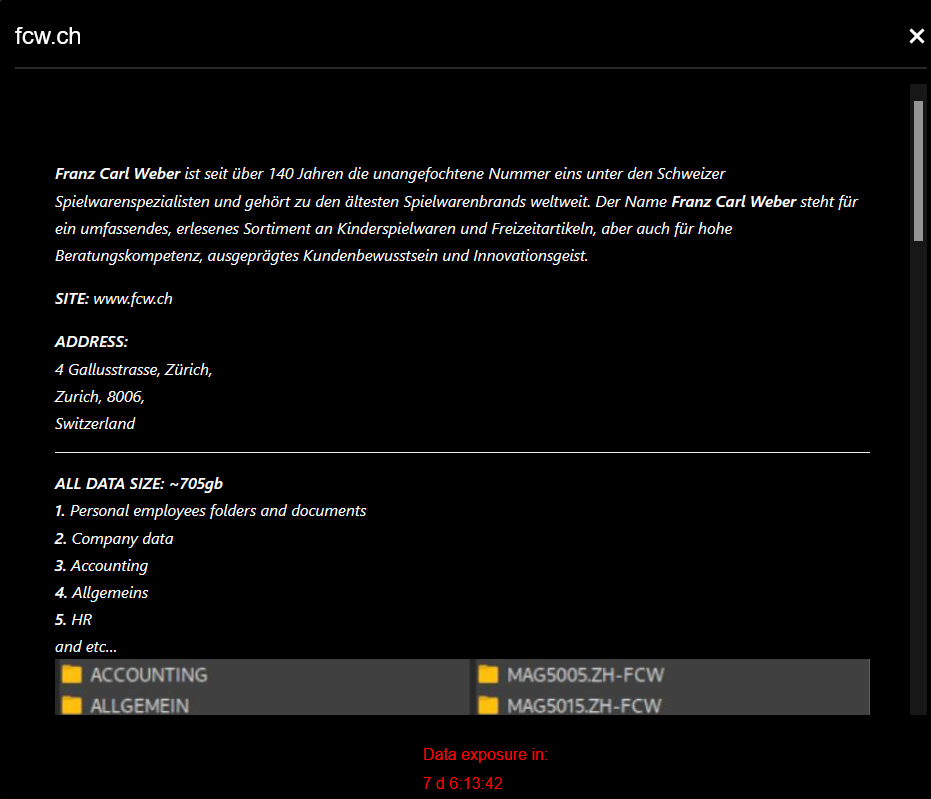
FRANZ CARL WEBER
Victim website: | fcw.ch |
Victim country: | Switzerland |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 705 GB |
Exfiltrated data type: | Personal employees folders and documents, company data, accounting, general, HR, etc. |
Leaked data: | Sample |
Ransom deadline: | 08th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
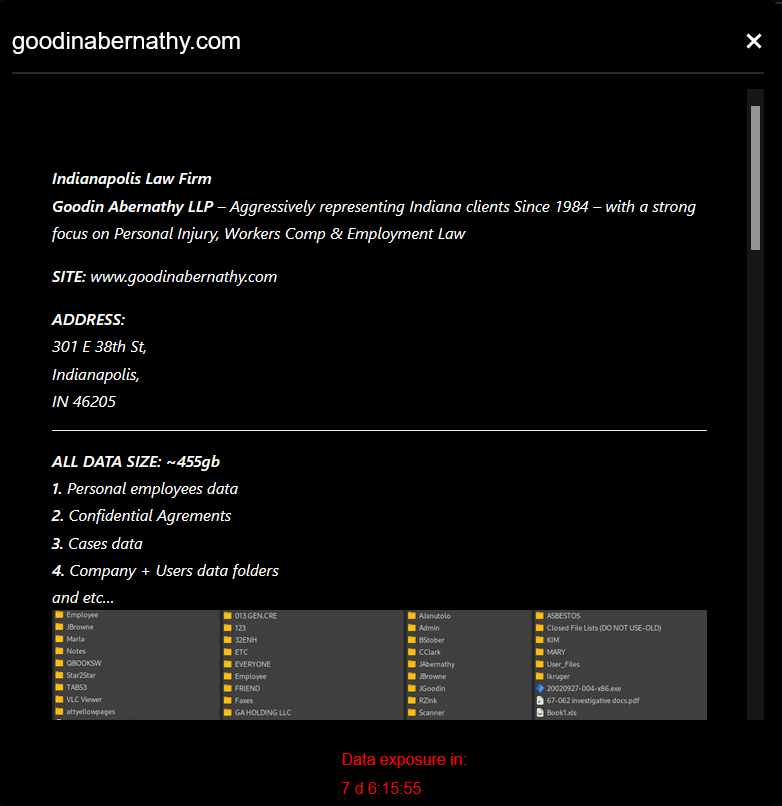
GOODIN ABERNATHY
Victim website: | goodinabernathy.com |
Victim country: | USA |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 455 GB |
Exfiltrated data type: | Personal employees data, confidential agreements, cases data, company and users data folders, etc. |
Leaked data: | Sample |
Ransom deadline: | 08th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
Stay safe!
Hackmanac Team!
Latest news
HACKS OF TODAY 26/04/2024
Today's HOT includes 19 victims by the notorious Rhysida, Everest, RansomHouse, DarkVault, RansomHub, Medusa, Hunters International, Cactus and dAn0n gangs. The average Cyber Risk Factor is 4.2. Read...
Read MoreHACKS OF TODAY 25/04/2024
Today's HOT includes 8 ransomware victims by the notorious RansomHub, Hunters International, Black Suit, Qiulong, DarkVault, RansomHouse, Qilin and MyData gangs. The average Cyber Risk Factor is 4.0....
Read MoreHACKS OF TODAY 24/04/2024
Today's HOT includes 10 ransomware victims by the notorious RansomHouse, Black Suit, Rhysida, BianLian, RansomHub, BlackBasta, Eraleig and Qiulong gangs. The average Cyber Risk Factor is 4.4. Read...
Read More