news
HACKS OF TODAY 11-12-13/11/2023

Today’s HOT includes 48 ransomware victims by the notorious Hunters International, ALPHV/BlackCat, Rhysida, Medusa, NoEscape, BlackBasta, Abyss and LockBit 3.0 gangs.
The average Cyber Risk Factor is 3.8.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
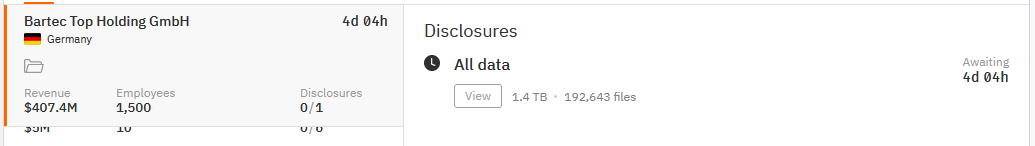
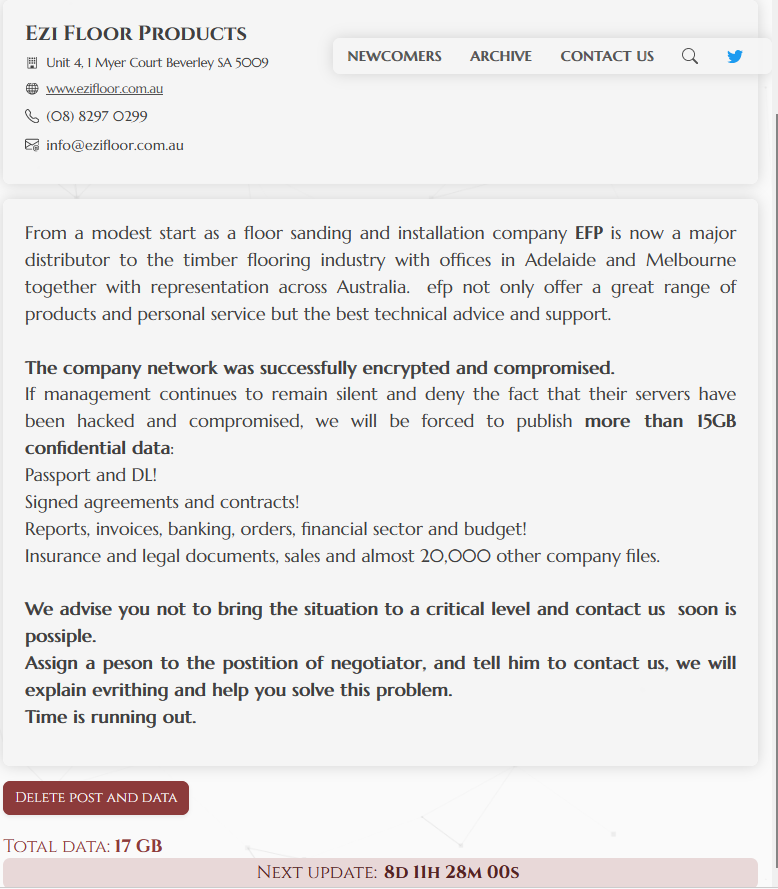
BARTEC
Victim website: | bartec.com |
Victim country: | Germany |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.4 TB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 17th Nov 23 |
Cyber Risk Factor: | 5 |
Image: |
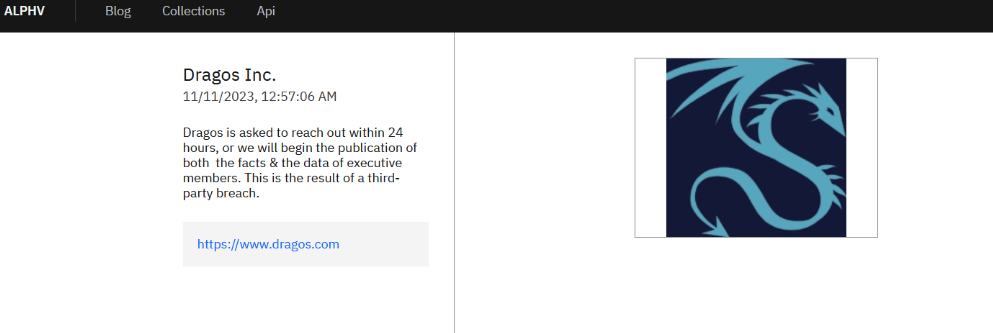
DRAGOS
Victim website: | dragos.com |
Victim country: | USA |
Attacker name: | ALPHV/BlackCat |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Facts and data of executive members |
Leaked data: | / |
Ransom deadline: | 12th Nov 23 |
Cyber Risk Factor: | 5 |
Image: |
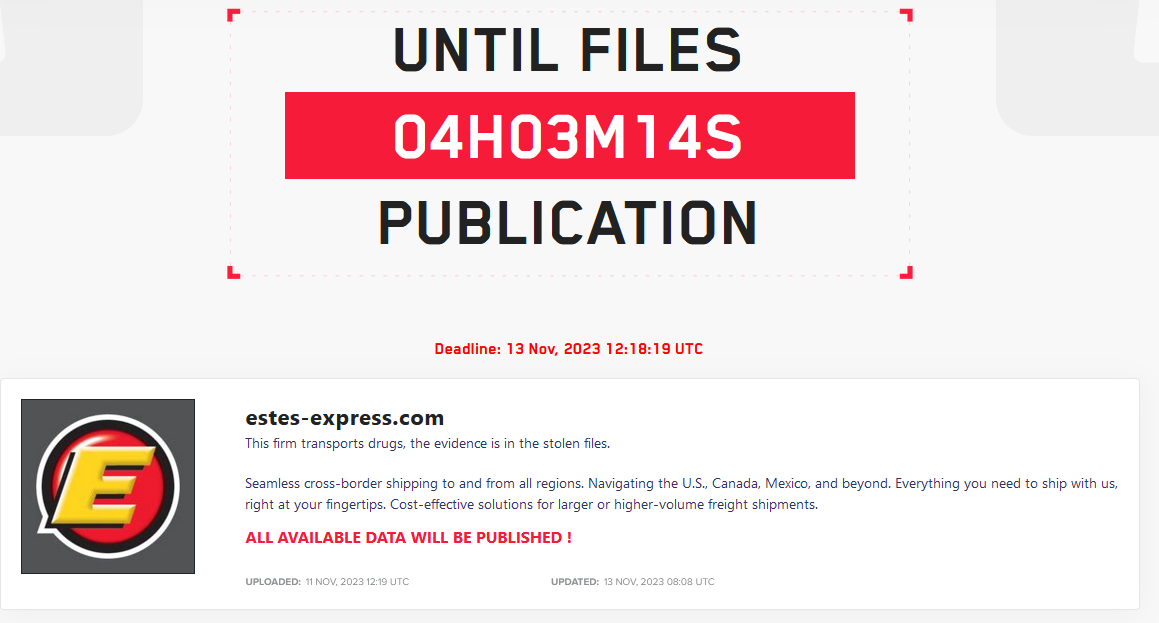
ESTES EXPRESS LINES
Victim website: | estes-express.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including evidence in the involvement of drugs transportation |
Leaked data: | / |
Ransom deadline: | 13th Nov 23 |
Cyber Risk Factor: | 5 |
Image: |
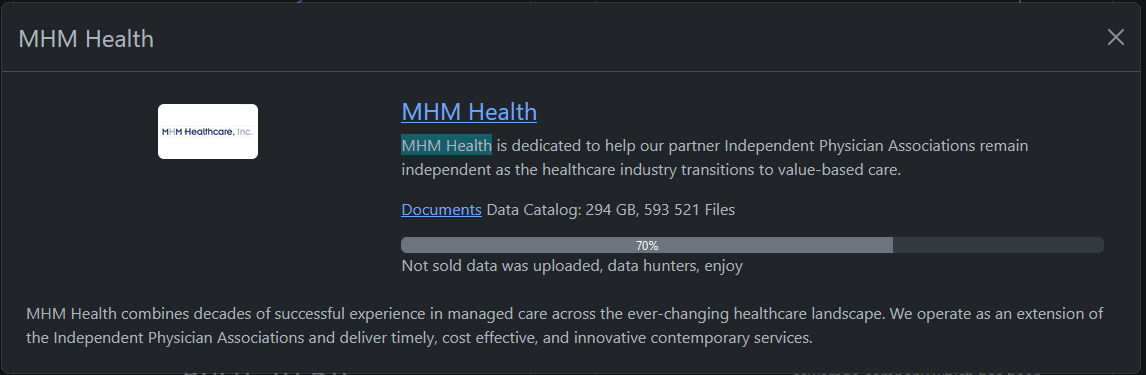
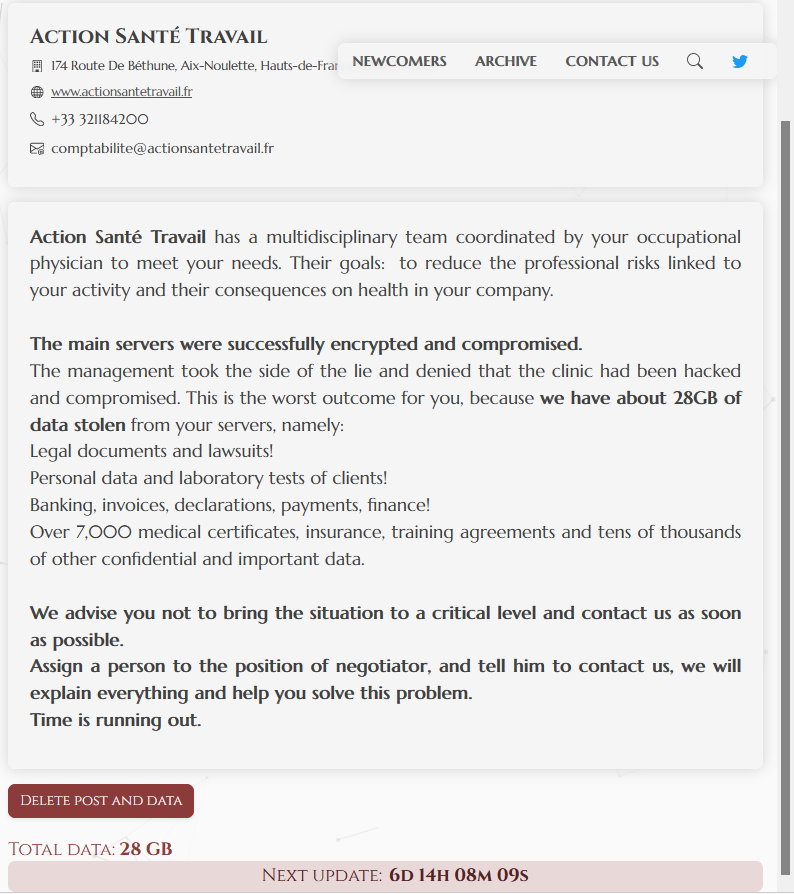
MHM HEALTH
Victim website: | mhmhealth.com |
Victim country: | USA |
Attacker name: | Rhysida |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 294 GB |
Exfiltrated data type: | N/A |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
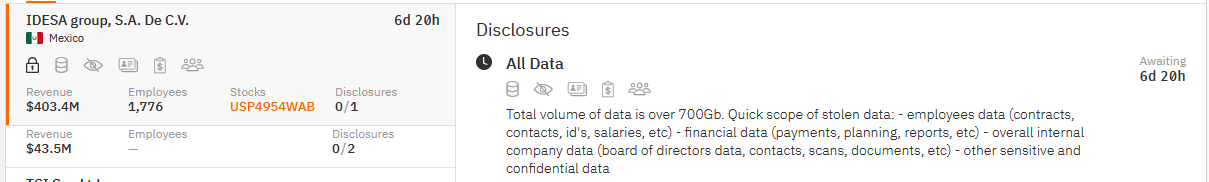
IDESA GROUP
Victim website: | grupoidesa.com |
Victim country: | Mexico |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 700 GB |
Exfiltrated data type: | Employees data including contracts, contacts, ID’s, salaries, etc., financial data such as payments, planning, reports, etc., overall internal company data including board of directors’ data, contacts, scans, documents, etc., and other sensitive and confidential data |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 20th Nov 23 |
Cyber Risk Factor: | 5 |
Image: |
TCI
Victim website: | tci-bio.com |
Victim country: | Taiwan |
Attacker name: | Hunters international |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 236.3 GB (104,001 files) |
Exfiltrated data type: | Customer complaint data, SQL backups including HR base, CRM base, and other bases, financial data such as payments, reports, audits, etc., business units data including orders, product recipes, lab tests, packages, etc., USA division data with network settings, audits, vendors, employee data, etc., and customers data covering orders, mixtures, product recipes, lab tests, packages, mails, etc. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
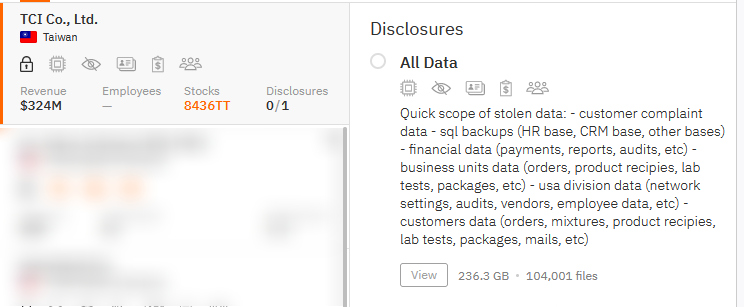
MONERIS SOLUTIONS
Victim website: | moneris.com |
Victim country: | Canada |
Attacker name: | Medusa |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 6,000,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including email correspondence and other sensitive data. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 22nd Nov 23 |
Cyber Risk Factor: | 5 |
Image: |
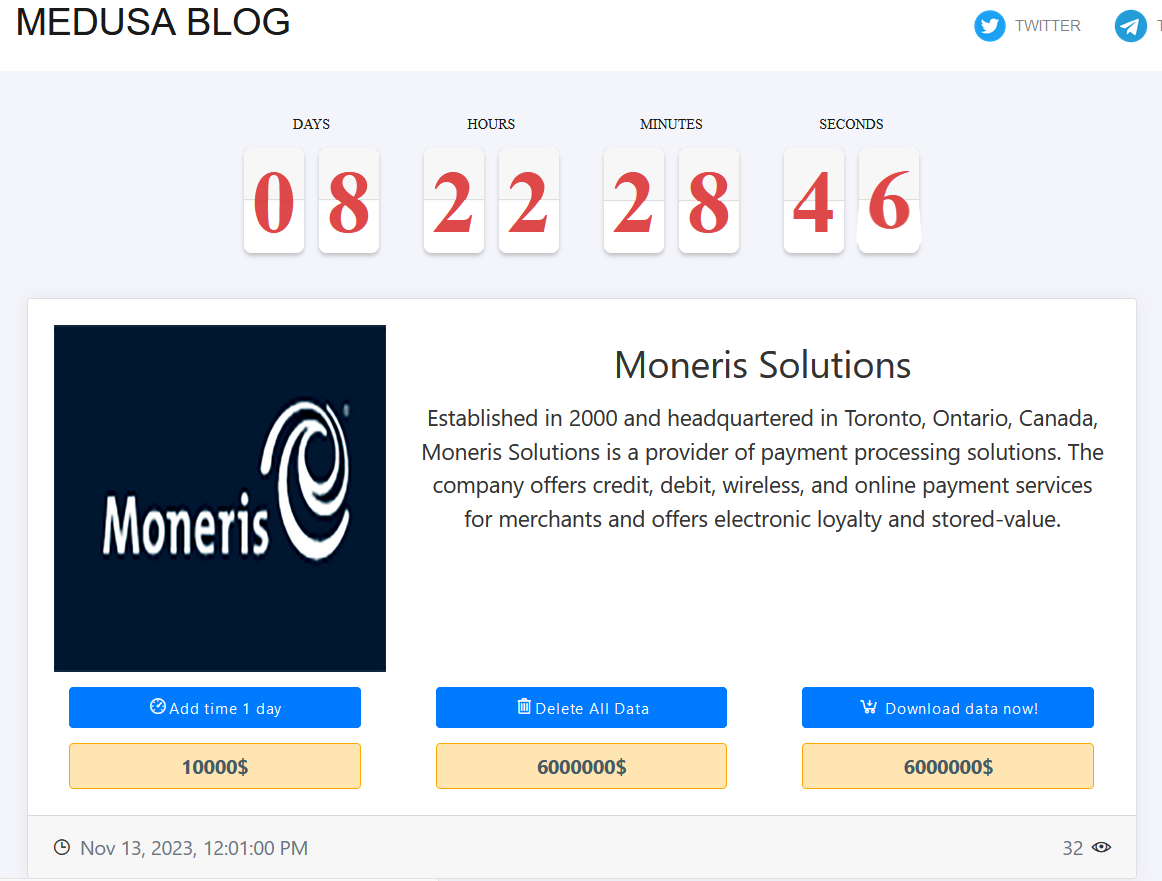
PUTZEL ELECTRICAL CONTRACTORS
Victim website: | putzelelectric.com |
Victim country: | USA |
Attacker name: | NoEscape |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 162 GB |
Exfiltrated data type: | Confidential agreements and contracts, finance, taxes, budget, accounting, 401K data, banking, full CC info, employee personal information, including SSN, DL, Electrical License, etc., databases, audit, reports, insurance, licenses, certificates, invoices, payments, v-card, scans and hundreds of thousands of other confidential and important data. |
Leaked data: | / |
Ransom deadline: | 23rd Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
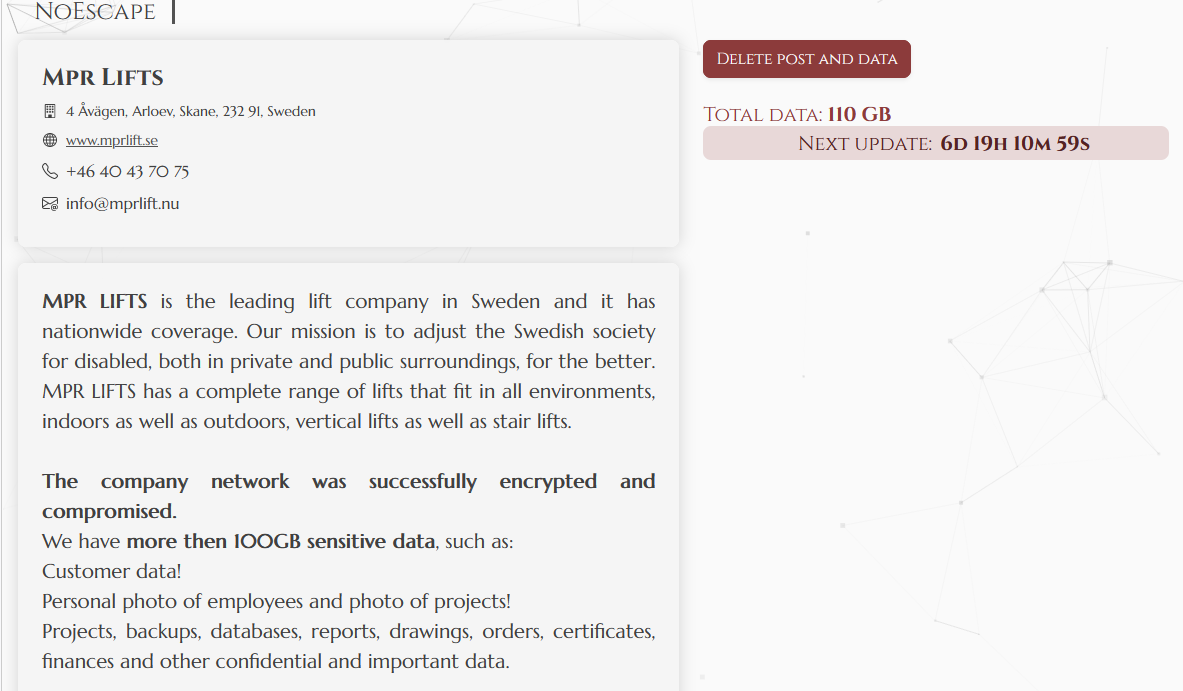
MPR LIFTS
Victim website: | mprlift.se |
Victim country: | Sweden |
Attacker name: | NoEscape |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 110 GB |
Exfiltrated data type: | Customer data, personal photo of employees and photo of projects, projects, backups, databases, reports, drawings, orders, certificates, finances and other confidential and important data. |
Leaked data: | / |
Ransom deadline: | 20th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
MORNING STAR PACKING COMPANY
Victim website: | morningstarco.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 16th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
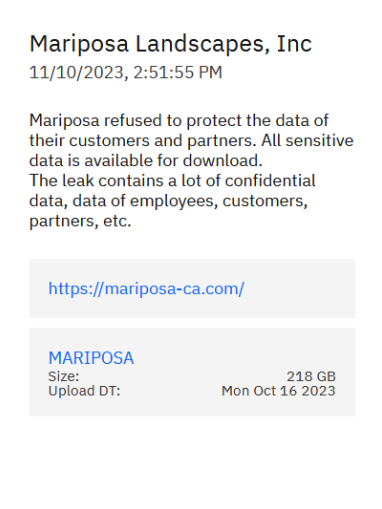
MARIPOSA LANDSCAPES
Victim website: | mariposa-ca.com |
Victim country: | USA |
Attacker name: | ALPHV/BlackCat |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 218 GB |
Exfiltrated data type: | Confidential data, data of employees, customers, partners, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
AYA KITCHENS
Victim website: | ayakitchens.com |
Victim country: | Canada |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Passports, driving licenses, invoices, and other sensitive data. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 19th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
BROWARD FACTORY SERVICE
Victim website: | browardfactory.com |
Victim country: | USA |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | SSNs, driving licenses, tax forms, etc. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 16th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
MONTCALM MONTAGENS INDUSTRIAIS
Victim website: | montcalm.com.br |
Victim country: | Brazil |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Passports, confidential documents, etc. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 19th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
BOS LOGISTICS
Victim website: | boslogistics.eu |
Victim country: | Netherlands |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Passports, driving licenses. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 17th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
FLOORTEX
Victim website: | floortex.com |
Victim country: | United Kingdom |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Passports, credits cards, bank data, insurances data, employees’ data, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | 12th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
MOTOR DEPOT
Victim website: | motordepot.co.uk |
Victim country: | United Kingdom |
Attacker name: | Abyss |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 636 GB |
Exfiltrated data type: | Personal information, photos with personal IDs. |
Leaked data: | / |
Ransom deadline: | 16th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
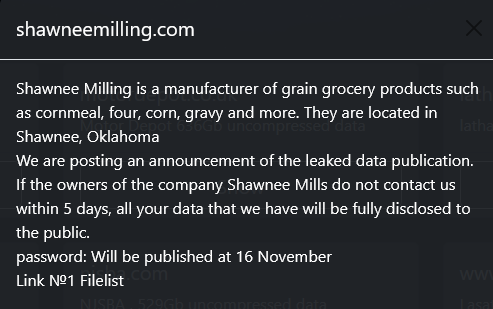
SHAWNEE MILLING
Victim website: | shawneemilling.com |
Victim country: | USA |
Attacker name: | Abyss |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 805 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 16th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
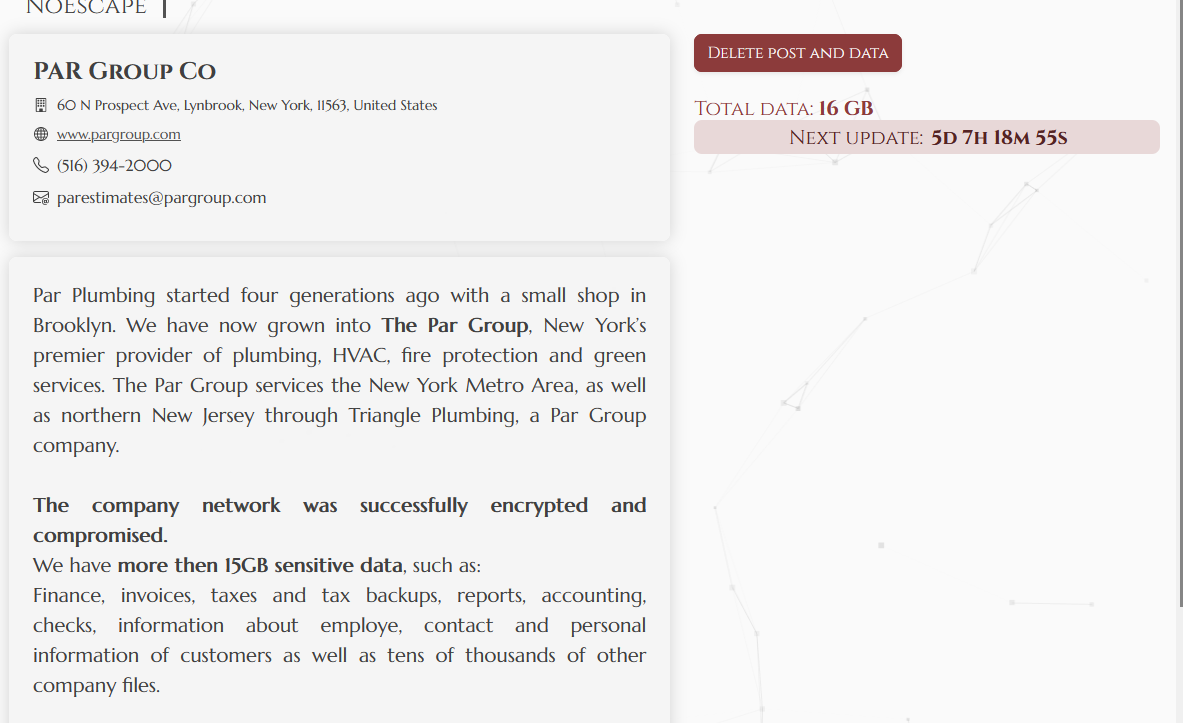
PAR GROUP
Victim website: | pargroup.com |
Victim country: | USA |
Attacker name: | NoEscape |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 16 GB |
Exfiltrated data type: | Finance, invoices, taxes and tax backups, reports, accounting, checks, information about employee, contact and personal information of customers as well as tens of thousands of other company files. |
Leaked data: | / |
Ransom deadline: | 18th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
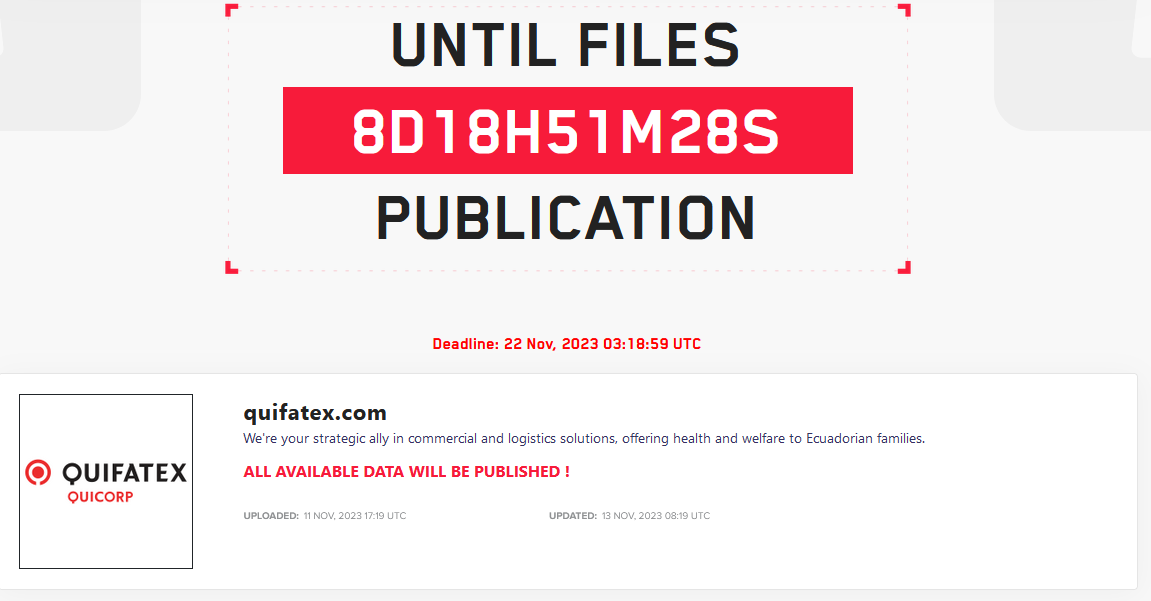
QUIFATEX
Victim website: | quifatex.com |
Victim country: | Ecuador |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 22nd Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
ATEN INTERNATIONAL
Victim website: | aten.com |
Victim country: | Taiwan |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 28th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
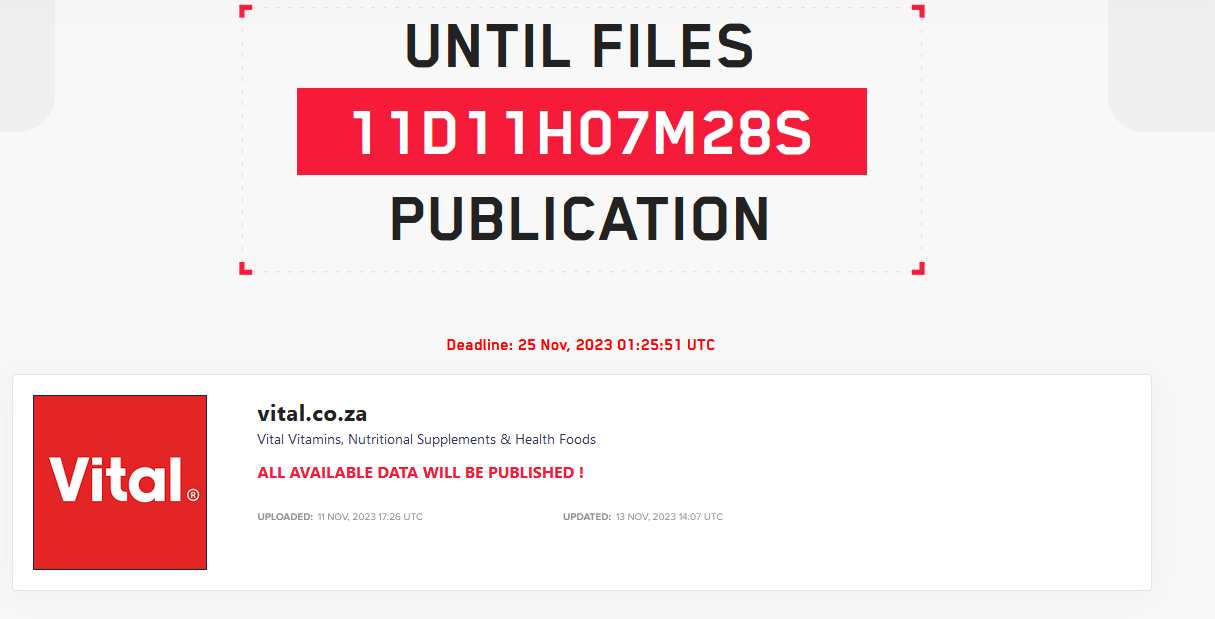
VITAL HEALTH FOODS
Victim website: | vital.co.za |
Victim country: | South Africa |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 25th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
|
CREATZ3D
Victim website: | creatz3d.sg |
Victim country: | Singapore |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 23rd Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
DÉPARTEMENT DU LOIRET
Victim website: | loiret.fr |
Victim country: | France |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 25th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
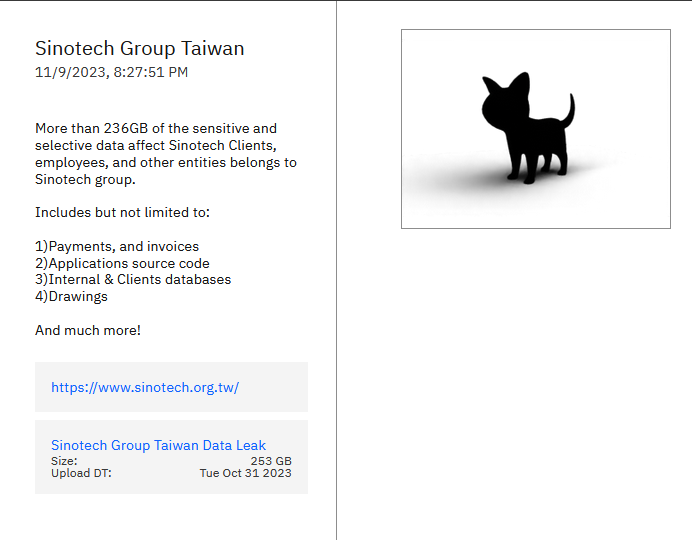
SYNNEX GROUP
Victim website: | synnex-grp.com |
Victim country: | Taiwan |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 29th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
GATTO INDUSTRIAL PLATERS
Victim website: | gattoplaters.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 22nd Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
HEINRICH SEEGERS OBJEKTTEXTILIEN
Victim website: | heinrichseegers.de |
Victim country: | Germany |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 25th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
ROTH WERKZEUGBAU
Victim website: | roth-werkzeugbau.de |
Victim country: | Germany |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 25th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
PRICESMART
Victim website: | pricesmart.com |
Victim country: | USA |
Attacker name: | ALPHV/BlackCat |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 500 GB |
Exfiltrated data type: | Sensitive data, clients and employees’ data |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
HÔTEL AMPÈRE
Victim website: | hotel-ampere-paris.com |
Victim country: | France |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 25th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
PLATI
Victim website: | plati.it |
Victim country: | Italy |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 21st Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
CARSON TEAM
Victim website: | carsonteam.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 60,000 files |
Exfiltrated data type: | Confidential information, personal data of all employees, financial reports, tax reports, technical documentation, documentation for official use. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 14th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
CITY OF CLARKSVILLE
Victim website: | cityofclarksville.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
ESSER GROUP
Victim website: | digitaldruck-esser.de |
Victim country: | Germany |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
HOTEL EMC2
Victim website: | hotelemc2.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
THE WALKER SCHOOL
Victim website: | thewalkerschool.org |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
MODAFABRICS
Victim website: | modafabrics.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
WOMBLE COMPANY
Victim website: | wombleco.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
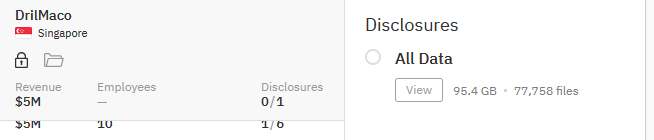
DRILMACO
Victim website: | drilmaco.com |
Victim country: | Singapore |
Attacker name: | Hunters international |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 95.4 GB (77,758 files) |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
OWENS GROUP
Victim website: | owensgroup.uk |
Victim country: | United Kingdom |
Attacker name: | Hunters international |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
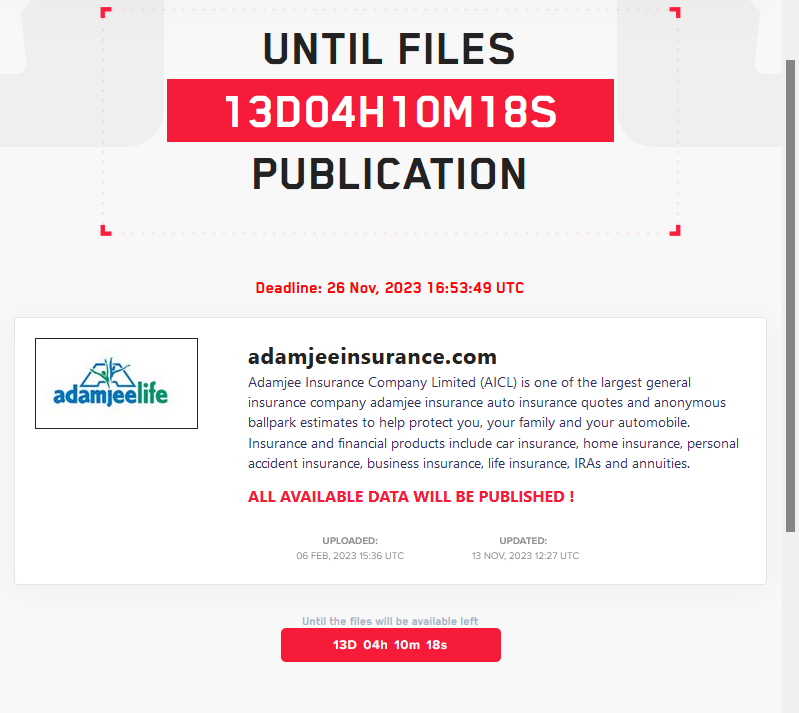
ADAMJEE INSURANCE COMPANY
Victim website: | adamjeeinsurance.com |
Victim country: | Pakistan |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
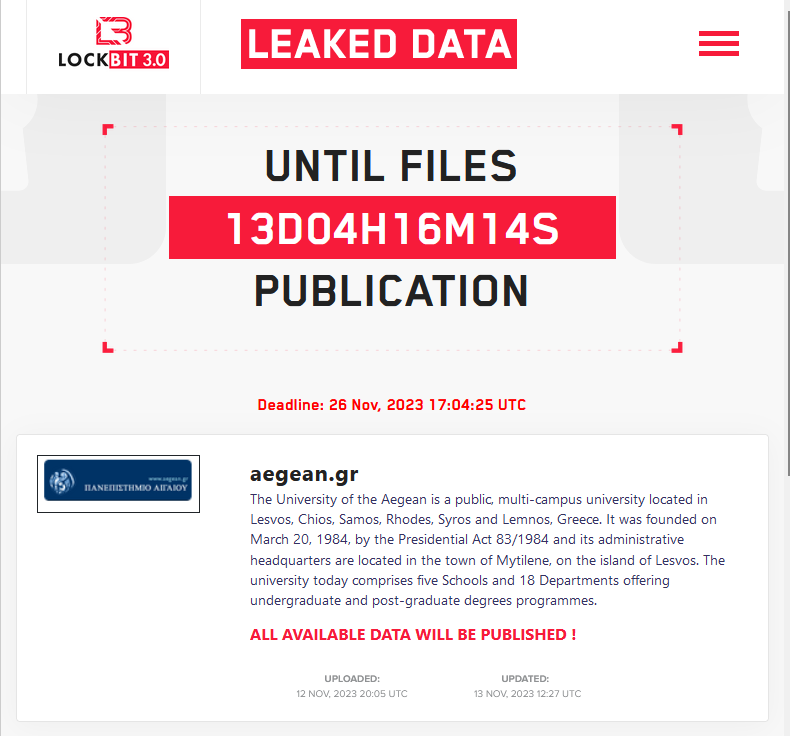
THE UNIVERSITY OF THE AEGEAN
Victim website: | aegean.gr |
Victim country: | Greece |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
SABENA ENGINEERING
Victim website: | sabena-engineering.com |
Victim country: | Belgium |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
MICROSERVE INFORMATIONS
Victim website: | msim.de |
Victim country: | Germany |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 194 GB |
Exfiltrated data type: | Miscellaneous documents including financial data |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 24th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
LEO’S JEANS HANDELS
Victim website: | leos-jeans.de |
Victim country: | Germany |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 194 GB |
Exfiltrated data type: | Miscellaneous documents including financial data |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 24th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
MUELLER SYSTEMS
Victim website: | muellersystems.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 26th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
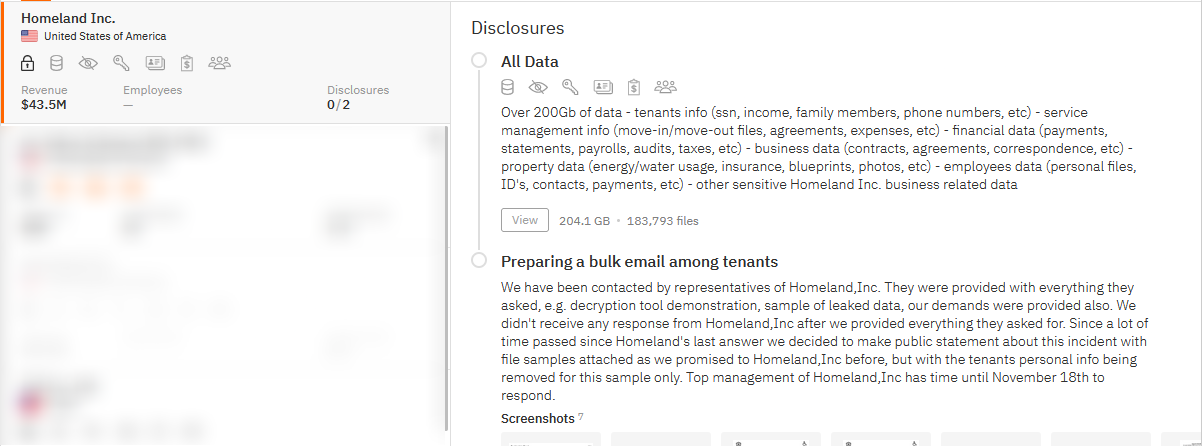
HOMELAND Inc
Victim website: | homelandinc.com |
Victim country: | USA |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 200 GB |
Exfiltrated data type: | Over 200Gb of data including tenants info such as SSN, income, family members, phone numbers, etc., service management info encompassing move-in/move-out files, agreements, expenses, etc., financial data featuring payments, statements, payrolls, audits, taxes, etc., business data with contracts, agreements, correspondence, etc., property data covering energy/water usage, insurance, blueprints, photos, etc., employees data with personal files, ID’s, contacts, payments, etc., and other sensitive Homeland Inc. business-related data. |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 18th Nov 23 |
Cyber Risk Factor: | 4 |
Image: |
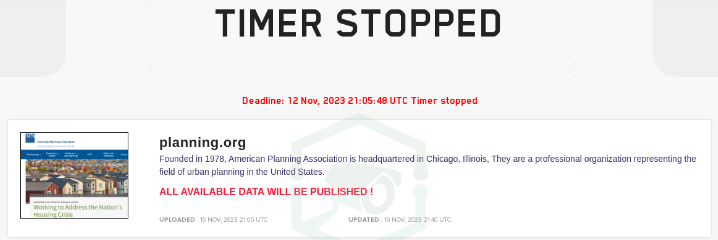
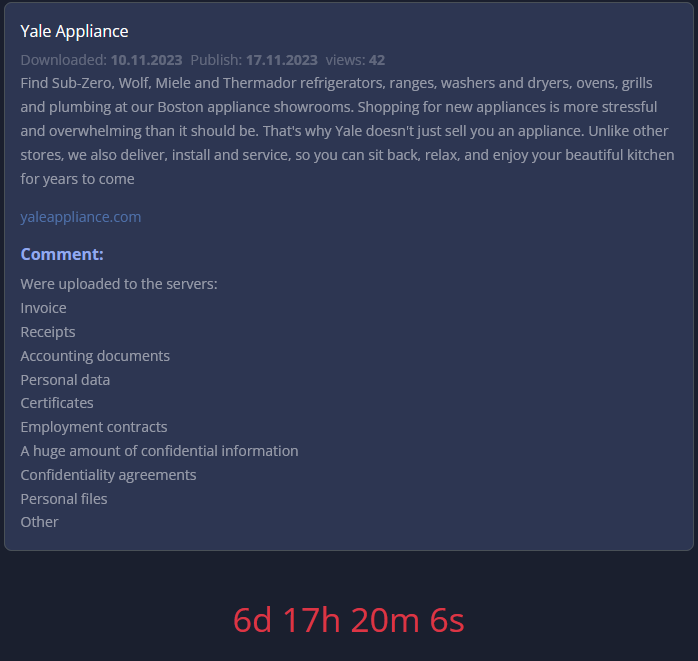
AMERICAN PLANNING ASSOCIATION
Victim website: | planning.org |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 12th Nov 23 |
Cyber Risk Factor: | 3 |
Image: |
Stay safe!
Hackmanac Team!
Latest news
HACKS OF TODAY 26/04/2024
Today's HOT includes 19 victims by the notorious Rhysida, Everest, RansomHouse, DarkVault, RansomHub, Medusa, Hunters International, Cactus and dAn0n gangs. The average Cyber Risk Factor is 4.2. Read...
Read MoreHACKS OF TODAY 25/04/2024
Today's HOT includes 8 ransomware victims by the notorious RansomHub, Hunters International, Black Suit, Qiulong, DarkVault, RansomHouse, Qilin and MyData gangs. The average Cyber Risk Factor is 4.0....
Read MoreHACKS OF TODAY 24/04/2024
Today's HOT includes 10 ransomware victims by the notorious RansomHouse, Black Suit, Rhysida, BianLian, RansomHub, BlackBasta, Eraleig and Qiulong gangs. The average Cyber Risk Factor is 4.4. Read...
Read More