news
HACKS OF TODAY 19-20/03/2024

Today’s HOT includes 22 ransomware victims by the notorious Hunters International, LockBit 3.0, DragonForce, Medusa, Trigona, Snatch, 8Base, Rhysida, BlackBasta and BianLian gangs.
The average Cyber Risk Factor is 3.7.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
HSI GROUP
Victim website: | hsi.es |
Victim country: | Spain |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
P&B CAPITAL
Victim website: | pandbcapitalgroup.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
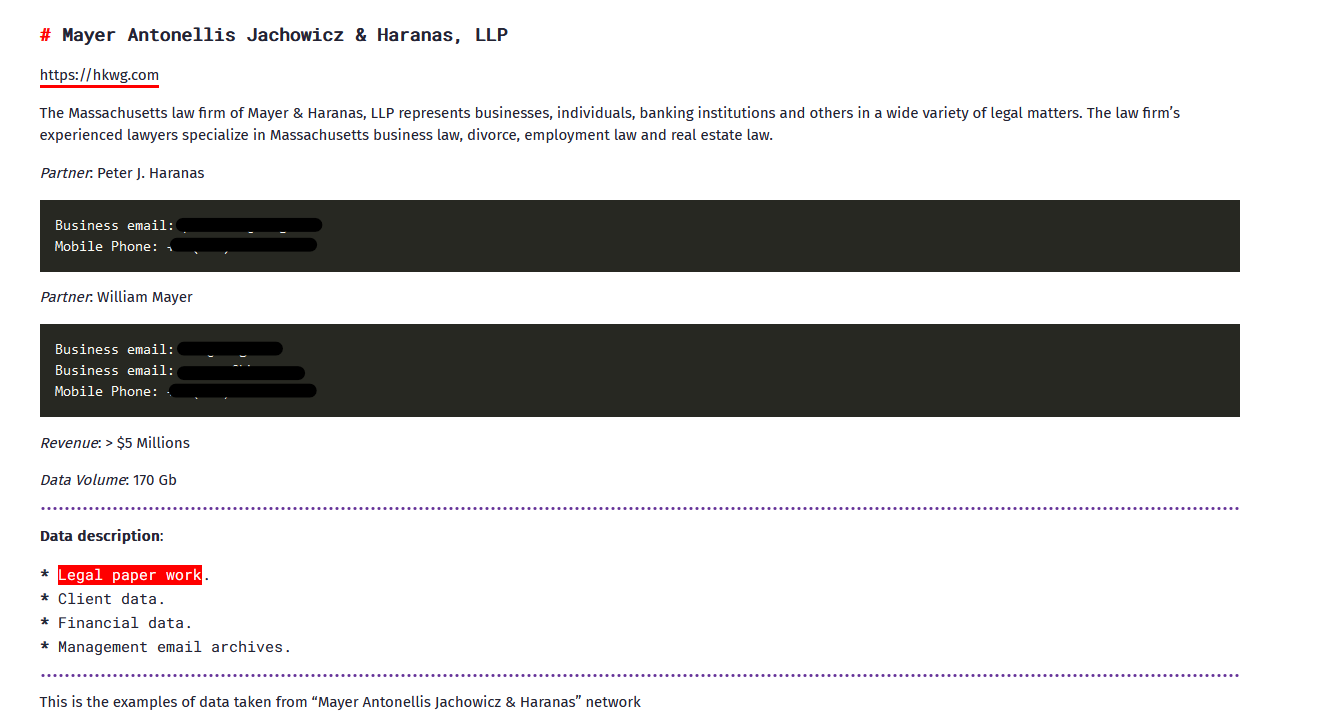
MAYER & HARANAS
Victim website: | hkwg.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 170 GB |
Exfiltrated data type: | Legal paperwork, client data, financial data, email archives. |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
DR DANIEL LEEMAN ENT
Victim website: | drleeman.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 480 GB |
Exfiltrated data type: | Finance data, HR data, PII and PHI records, patients’ images, cases, mailboxes, internal and external email correspondence with attachments, and SQL databases, etc. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
AGL
Victim website: | agladvisors.com |
Victim country: | China |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
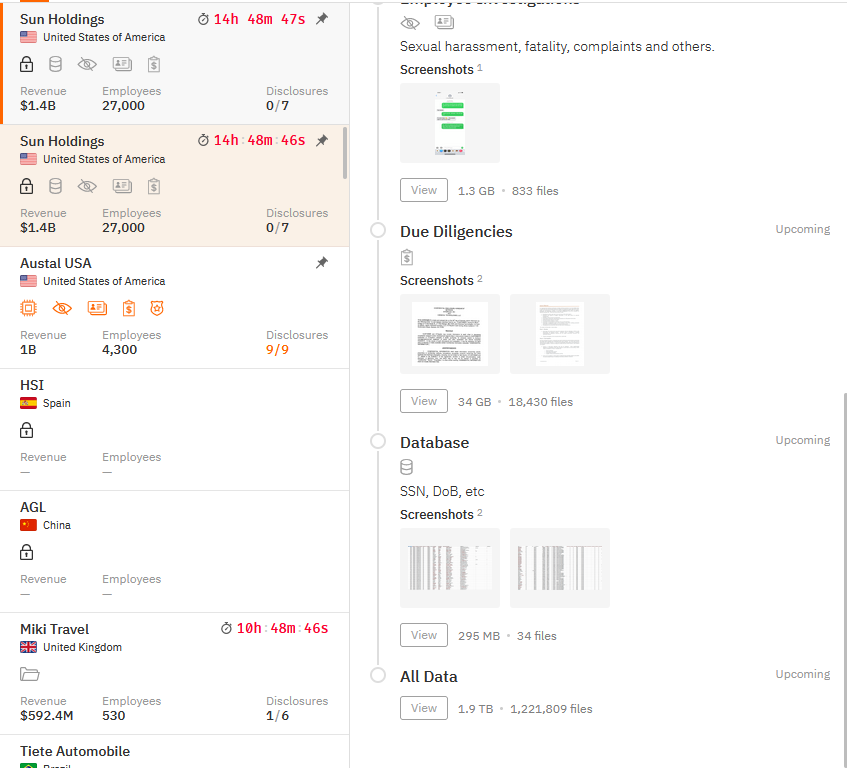
SUN HOLDINGS
Victim website: | sunholdings.net |
Victim country: | USA |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.9 TB |
Exfiltrated data type: | Names, dates of birth, Social Security numbers, addresses, phone numbers, emails, etc. |
Leaked data: | Sample |
Ransom deadline: | 20th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
SUN HOLDINGS (12th Mar 2024)
Victim website: | sunholdings.net |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
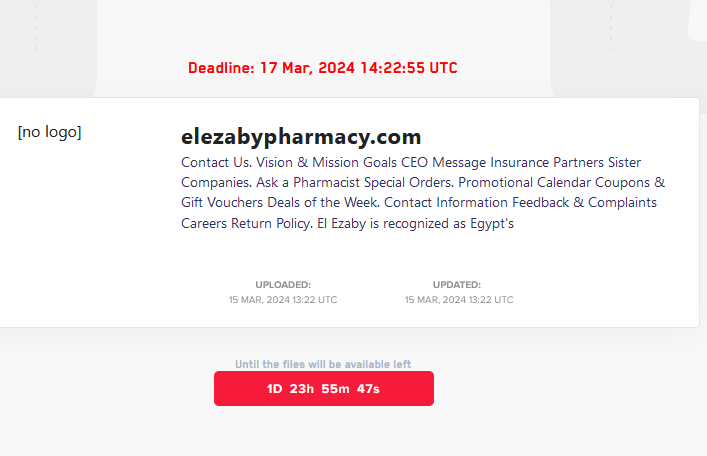
Ransom deadline: | 17th Mar 24 |
Cyber Risk Factor: | 3 |
Image: |
PANZIERI CATTANEO
Victim website: | panzericattaneonotai.it |
Victim country: | Italy |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
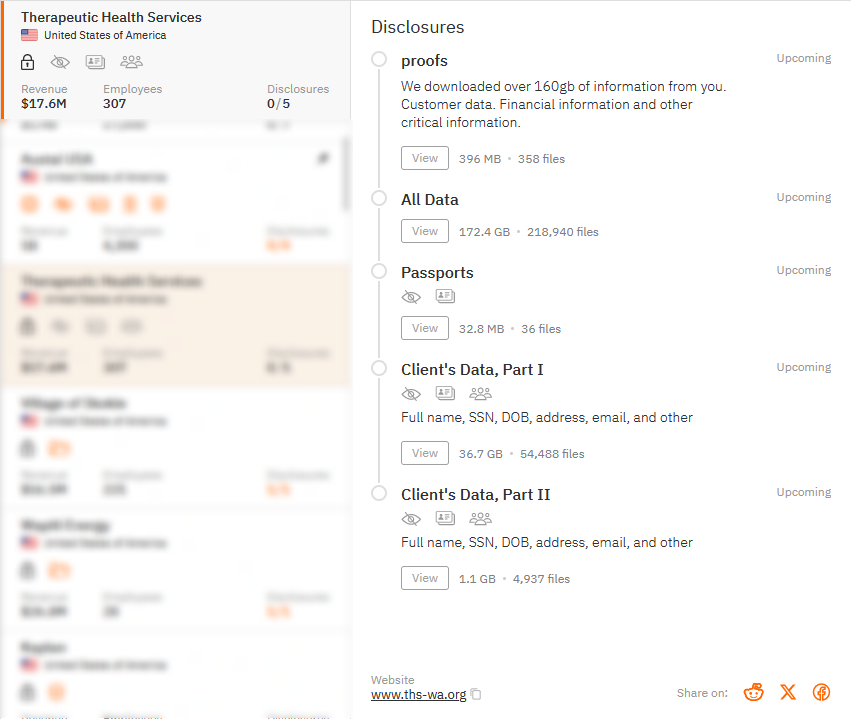
THERAPEUTIC HEALTH SERVICES
Victim website: | ths-wa.org |
Victim country: | USA |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 172.4 GB (218,940 files) |
Exfiltrated data type: | Customer data (full name, SSN, DOB, address, email, and other), passports, financial information, sensitive data and so on. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
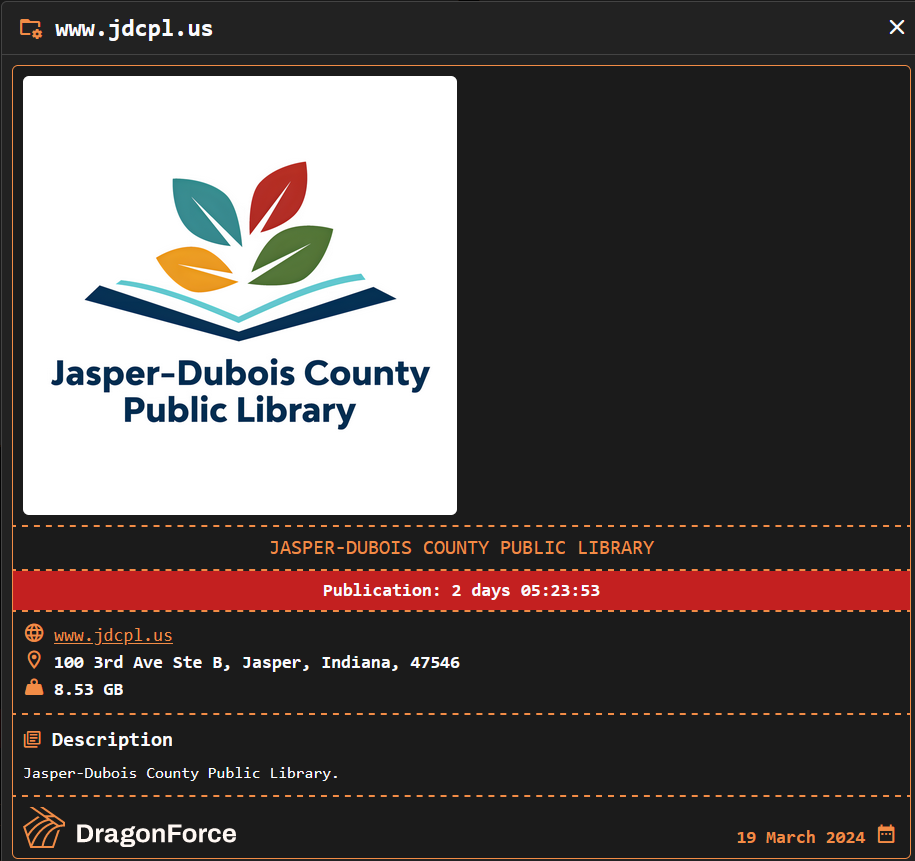
JASPER-DUBOIS COUNTY PUBLIC LIBRARY
Victim website: | jdcpl.us |
Victim country: | USA |
Attacker name: | DragonForce |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 8.53 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 22nd Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
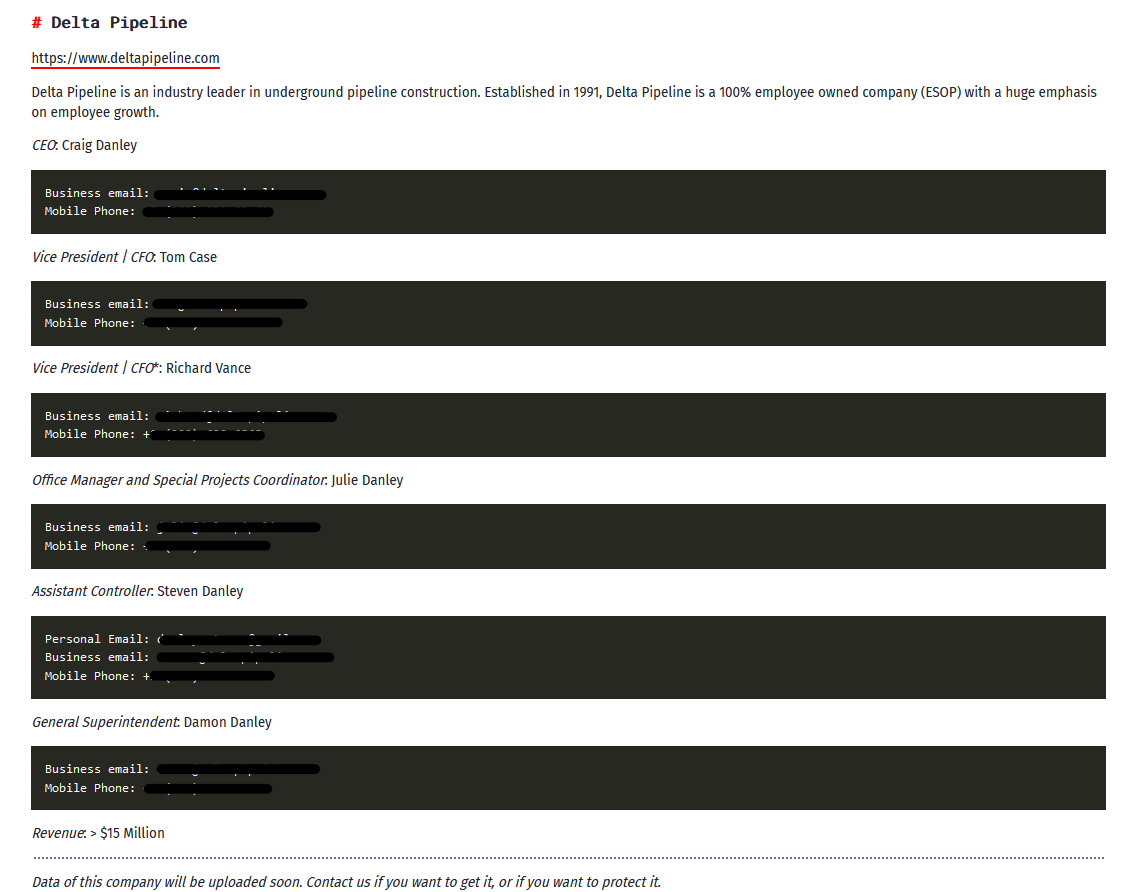
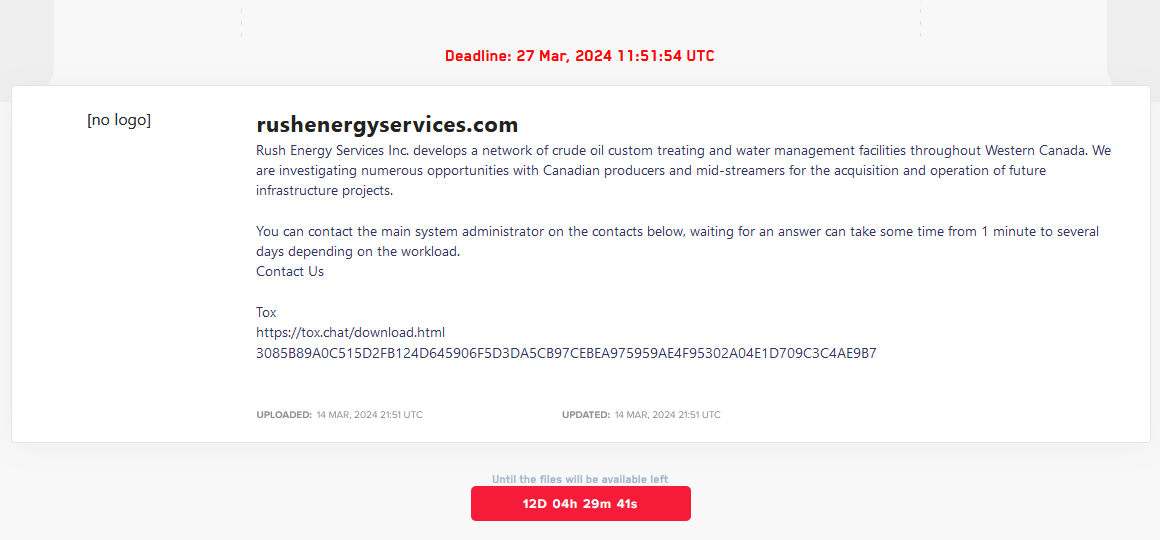
DELTA PIPELINE
Victim website: | deltapipeline.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
ACCIPITER CAPITAL MANAGEMENT
Victim website: | Not available |
Victim country: | USA |
Attacker name: | Medusa |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 300,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Certificates, PII documents, forms, confidential information, financial data, etc. |
Leaked data: | Sample |
Ransom deadline: | 27th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
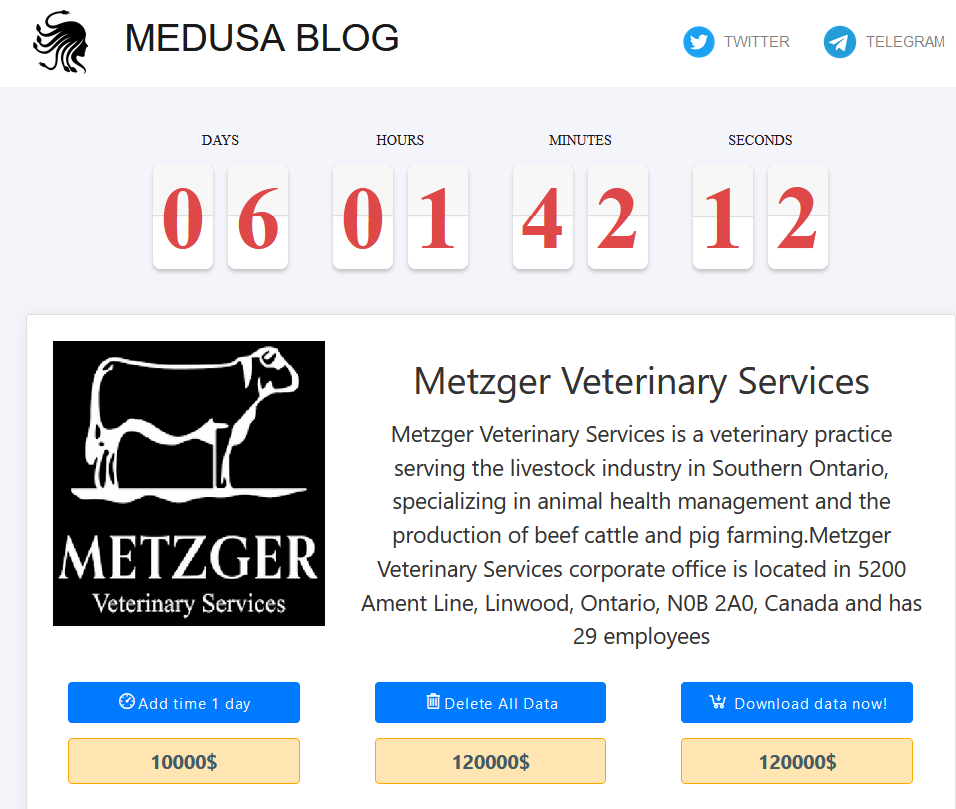
URBAN STRATEGIES
Victim website: | urbanstrategies.us |
Victim country: | USA |
Attacker name: | Medusa |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 100,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Reports, PII documents, confidential documents, clinical data, photos, email correspondence, etc. |
Leaked data: | Sample |
Ransom deadline: | 28th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
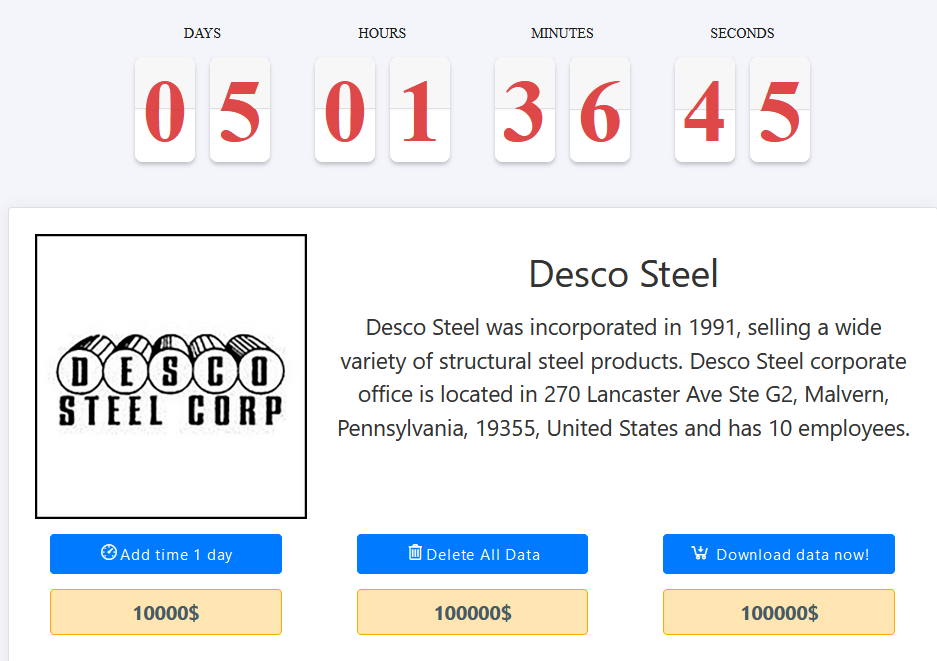
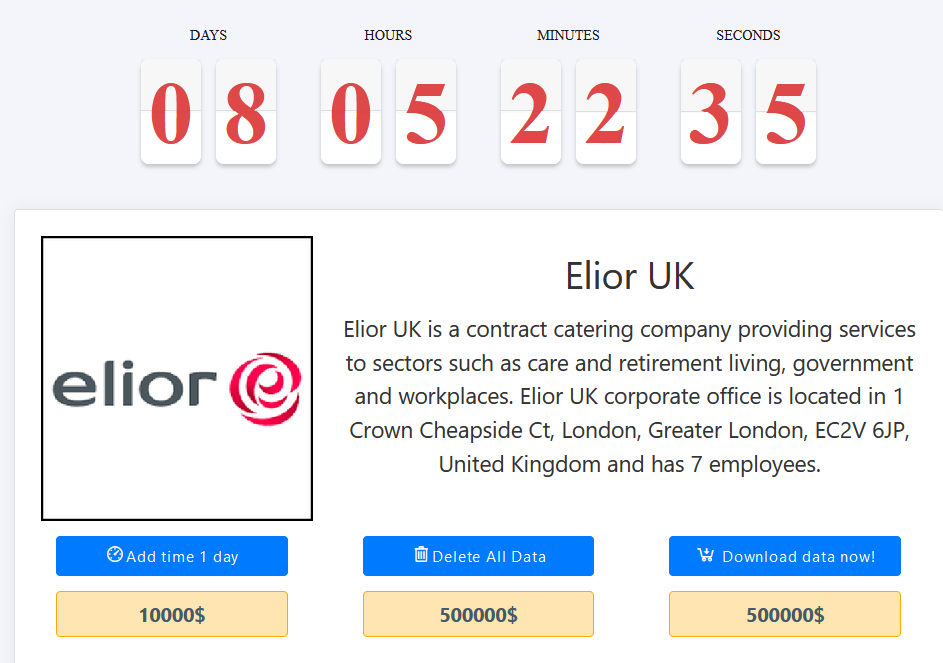
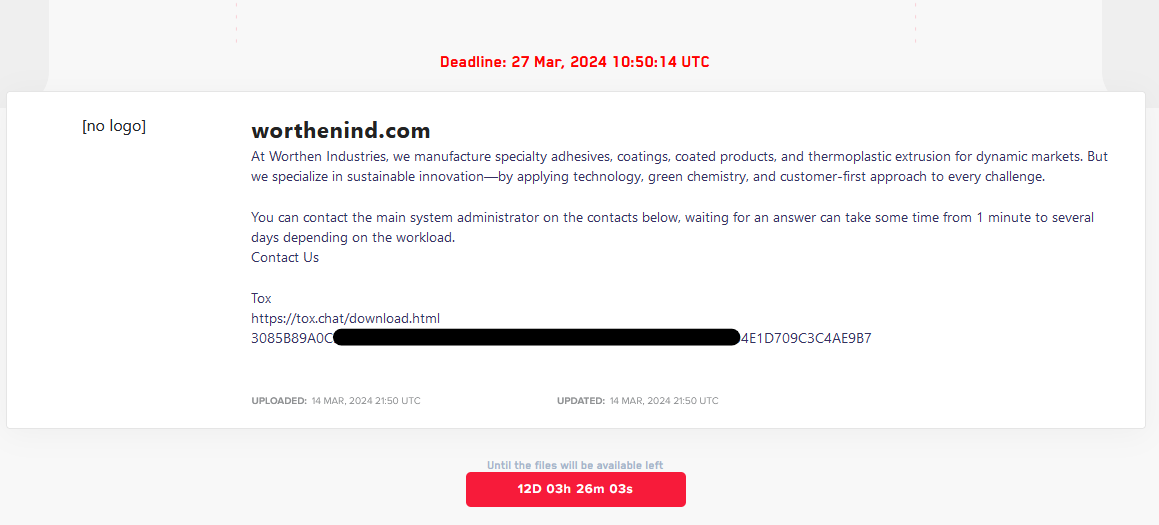
SOUTHSTAR ELECTRONICS
Victim website: | south-star.com.cn |
Victim country: | China |
Attacker name: | Trigona |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 150,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including employees’ data |
Leaked data: | Sample |
Ransom deadline: | 20th Apr 24 |
Cyber Risk Factor: | 4 |
Image: |
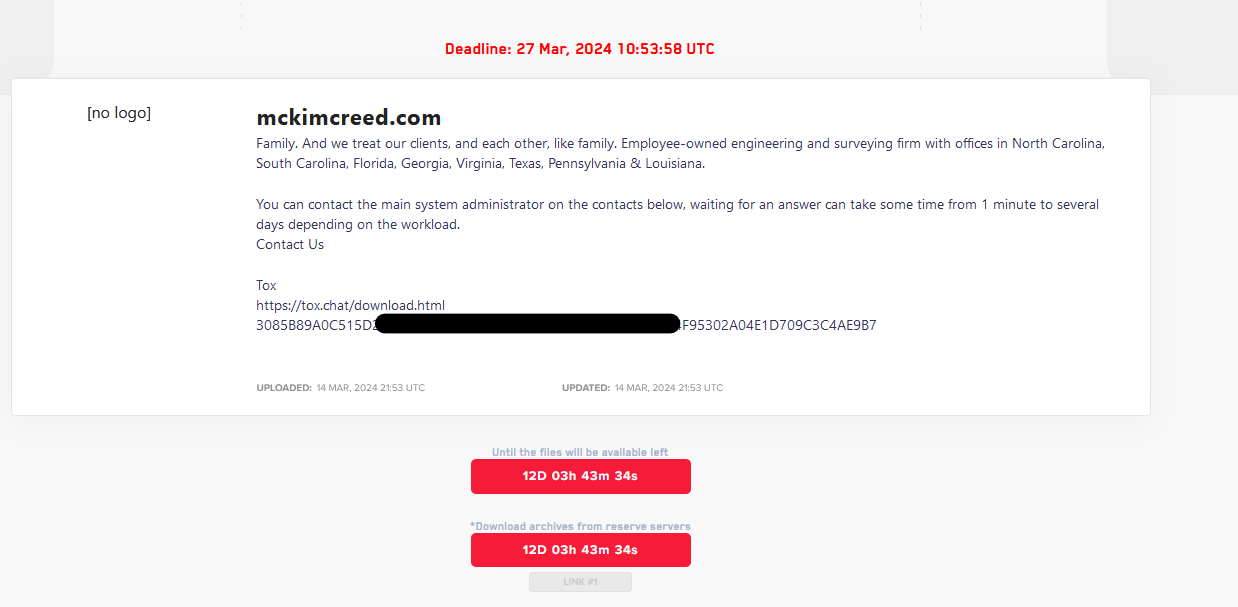
SPRINGFIELD SIGN
Victim website: | springfieldsign.com |
Victim country: | USA |
Attacker name: | 8Base |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Invoices, receipts, accounting documents, personal data, certificates, employment contracts, confidentiality agreements, personal files, etc. |
Leaked data: | / |
Ransom deadline: | 27th Mar 24 |
Cyber Risk Factor: | 3 |
Image: |
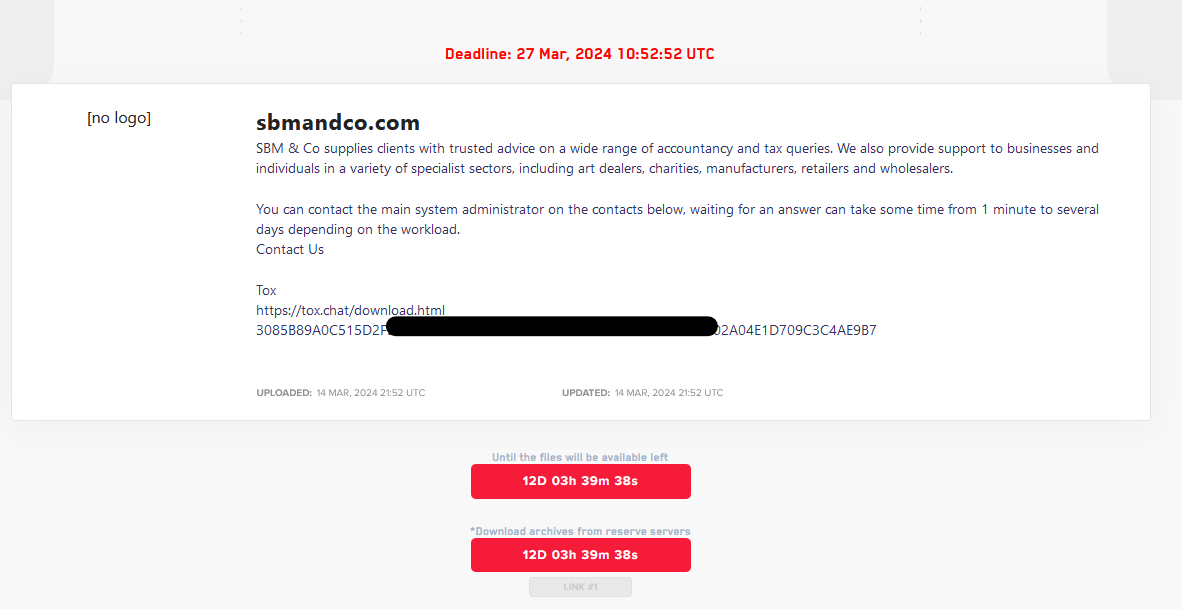
OSTENSSONS LIVS AB
Victim website: | ostenssons.se |
Victim country: | Sweden |
Attacker name: | 8Base |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Invoices, receipts, accounting documents, personal data, certificates, employment contracts, confidentiality agreements, personal files, etc. |
Leaked data: | / |
Ransom deadline: | 27th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
FILEXIS AG TREUHAND
Victim website: | filexis.ch |
Victim country: | Switzerland |
Attacker name: | 8Base |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Invoices, receipts, accounting documents, personal data, certificates, employment contracts, confidentiality agreements, personal files, etc. |
Leaked data: | / |
Ransom deadline: | 27th Mar 24 |
Cyber Risk Factor: | 3 |
Image: |
KOLBE STRIPING
Victim website: | kolbestriping.com |
Victim country: | USA |
Attacker name: | Rhysida |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | 3 BTC ($ 190,000) |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including employees’ data |
Leaked data: | Sample |
Ransom deadline: | 27th Mar 24 |
Cyber Risk Factor: | 4 |
Image: |
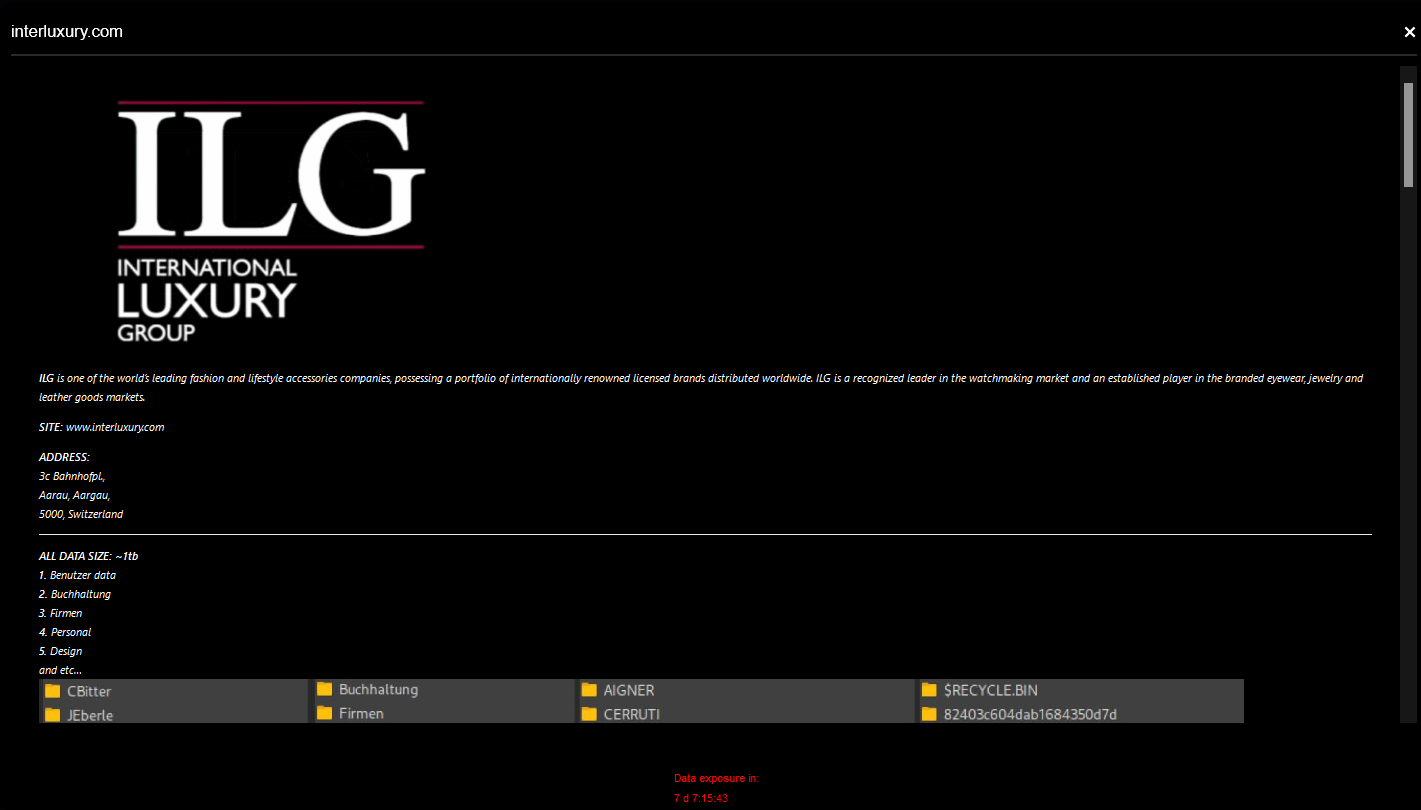
INTERNATIONAL LUXURY GROUP
Victim website: | interluxury.com |
Victim country: | Switzerland |
Attacker name: | BlackBasta |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1 TB |
Exfiltrated data type: | User data, accounting, companies, personal, design, etc. |
Leaked data: | Sample |
Ransom deadline: | 27th Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
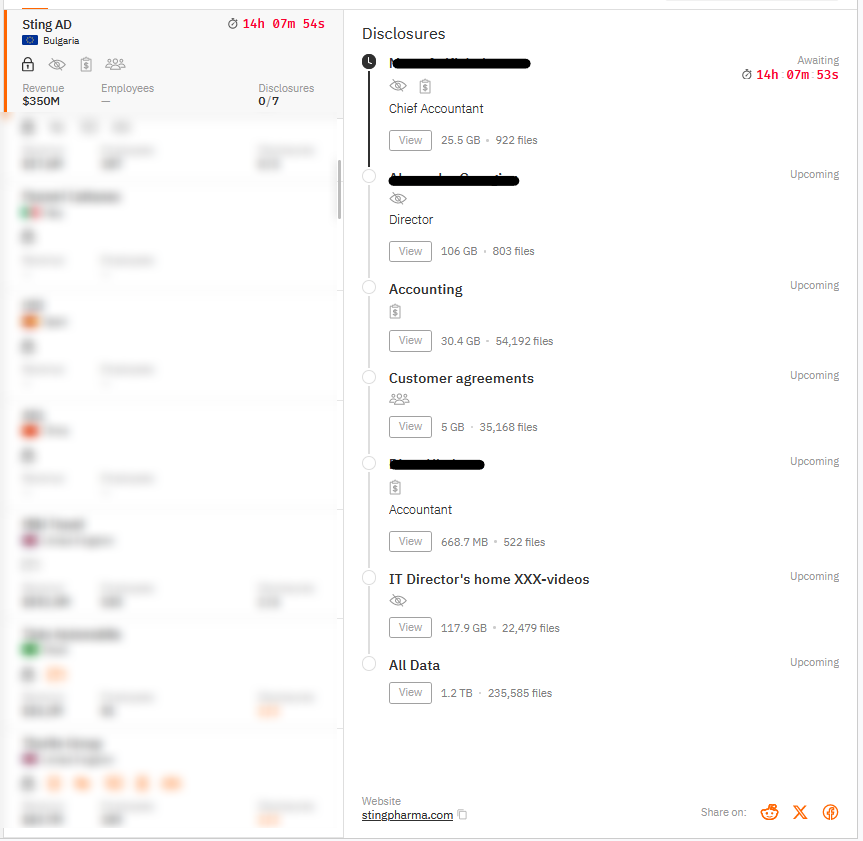
STING AD
Victim website: | stingpharma.com |
Victim country: | Bulgaria |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.2 TB |
Exfiltrated data type: | Accounting, customers’ data, accounting, etc. |
Leaked data: | / |
Ransom deadline: | 21st Mar 24 |
Cyber Risk Factor: | 5 |
Image: |
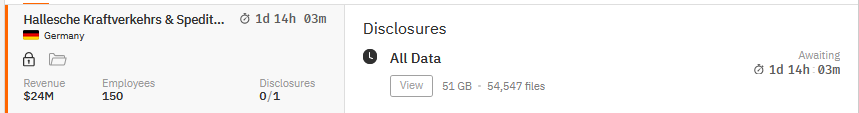
HALLESCHE KRAFTVERKEHRS & SPEDITIONS
Victim website: | Not available |
Victim country: | Germany |
Attacker name: | Hunters International |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 51 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
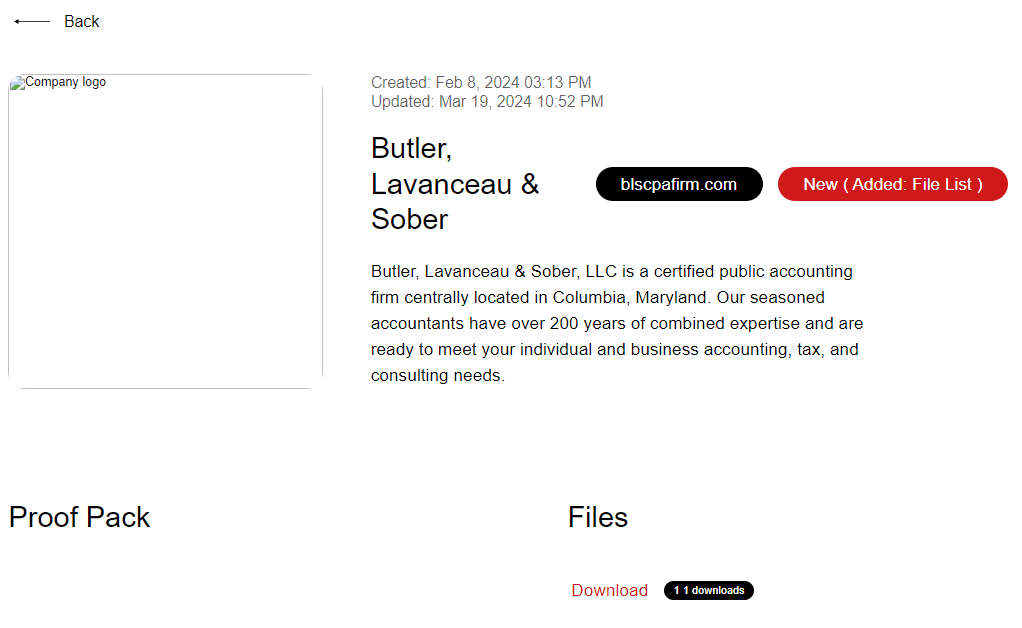
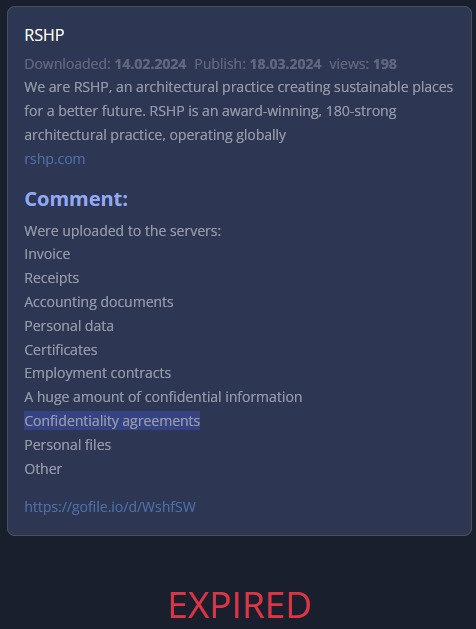
BUTLER, LAVANCEAU & SOBER (8th Feb 2024)
Victim website: | blscpafirm.com |
Victim country: | USA |
Attacker name: | Snatch |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
Stay safe!
Hackmanac Team!
Latest news
HACKS OF TODAY 25/04/2024
Today's HOT includes 8 ransomware victims by the notorious RansomHub, Hunters International, Black Suit, Qiulong, DarkVault, RansomHouse, Qilin and MyData gangs. The average Cyber Risk Factor is 4.0....
Read MoreHACKS OF TODAY 24/04/2024
Today's HOT includes 10 ransomware victims by the notorious RansomHouse, Black Suit, Rhysida, BianLian, RansomHub, BlackBasta, Eraleig and Qiulong gangs. The average Cyber Risk Factor is 4.4. Read...
Read MoreHACKS OF TODAY 23/04/2024
Today's HOT includes 12 ransomware victims by the notorious Medusa, Abyss, RansomHouse, Cactus, RansomHub, BianLian, Qilin and Qiulong gangs. The average Cyber Risk Factor is 4.5. Read below...
Read More