news
HACKS OF TODAY 02/05/2024

Today’s HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs.
The average Cyber Risk Factor is 4.3.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
CLINICA DE SALUD DEL VALLE DE SALINAS
Victim website: | csvs.org |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.7 TB |
Exfiltrated data type: | Finance data, HR data, patients’ and partners’ confidential data, PII and PHI data, test results and images, internal and external email correspondence, databases. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
AZTECA TAX SYSTEMS
Victim website: | aztecataxsystems.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 484 GB |
Exfiltrated data type: | Finance data, HR data, clients’ private data, contracts and agreements, internal and external email correspondence. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
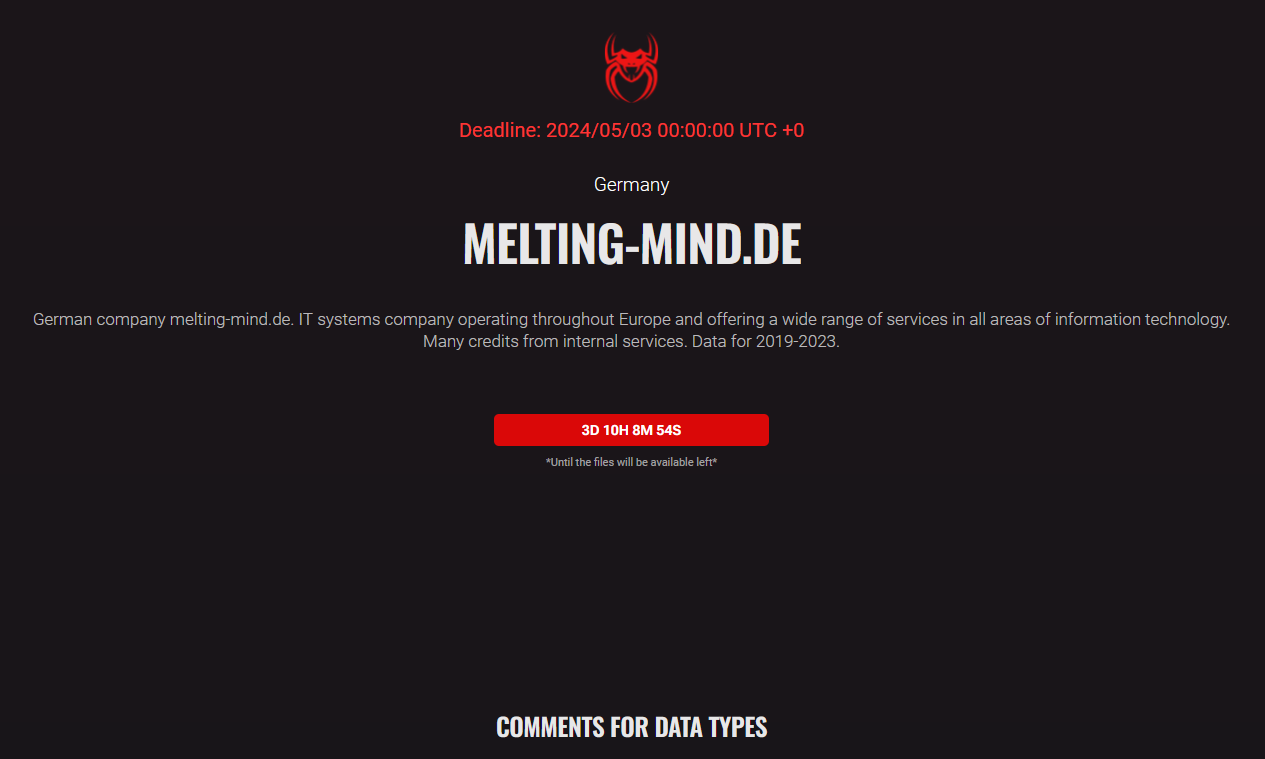
REEDEREI JUNGERHANS
Victim website: | juengerhans.de |
Victim country: | Germany |
Attacker name: | Ra World |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 424 GB |
Exfiltrated data type: | Legal documents, financial documents, customer information, employee documents, etc. |
Leaked data: | / |
Ransom deadline: | 15th May 24 |
Cyber Risk Factor: | 4 |
Image: |
GWF FRANKENWEIN
Victim website: | gwf-frankenwein.de |
Victim country: | Germany |
Attacker name: | Ra World |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 18 GB |
Exfiltrated data type: | Legal documents, financial documents, employee documents, etc. |
Leaked data: | / |
Ransom deadline: | 15th May 24 |
Cyber Risk Factor: | 3 |
Image: |
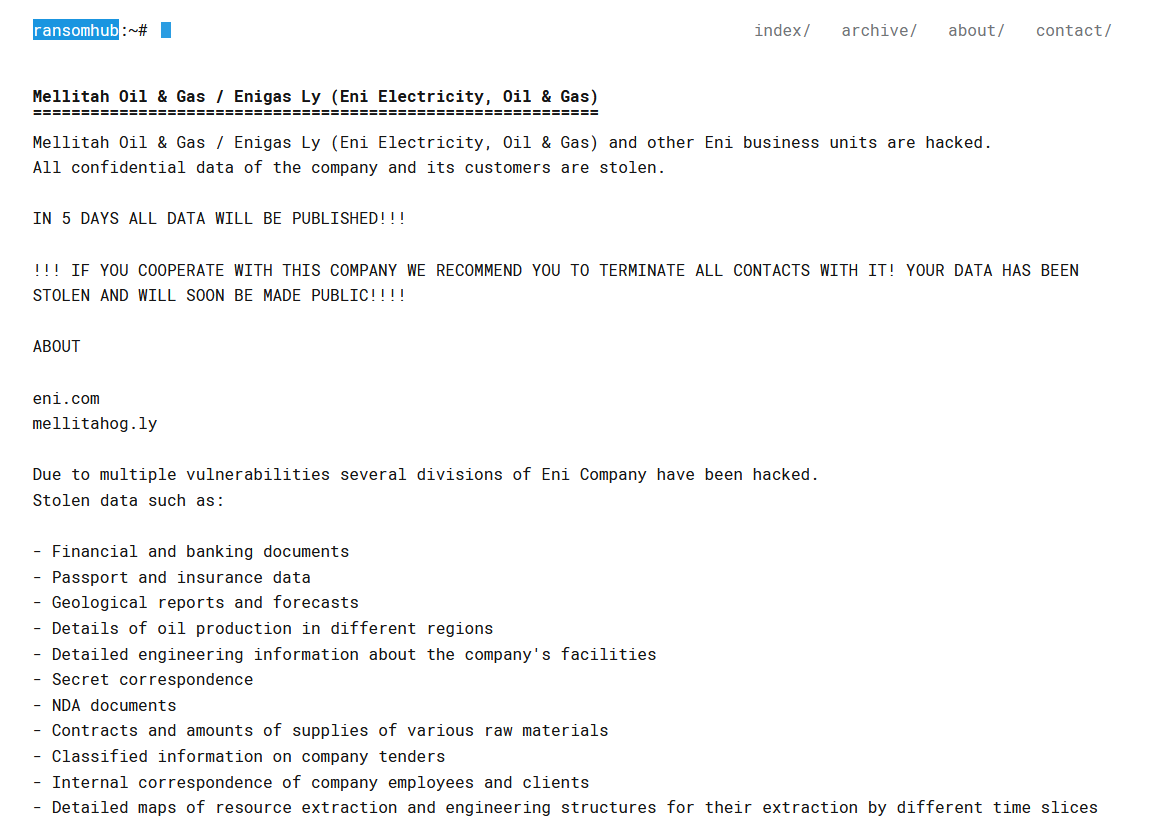
EXTRA CO
Victim website: | extraco.ae |
Victim country: | UAE |
Attacker name: | RansomHub |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 20 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 12th May 24 |
Cyber Risk Factor: | 4 |
Image: |
US-SAUDI ARABIAN BUSINESS COUNCIL
Victim website: | ussaudi.org |
Victim country: | USA |
Attacker name: | INC Ransom |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 200 GB |
Exfiltrated data type: | Confidential information, financial documents, mail correspondence, agreements and contracts that are not subject to disclosure, personal data of employees |
Leaked data: | Fully published |
Ransom deadline: | 29th Apr 24 |
Cyber Risk Factor: | 4 |
Image: |
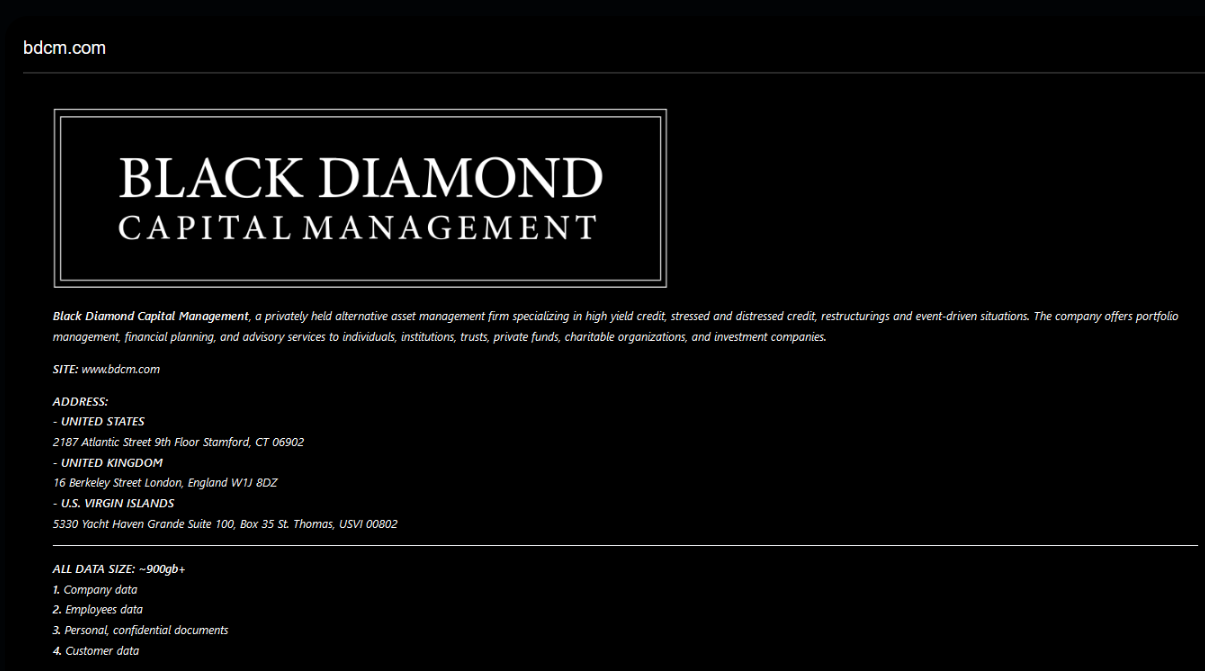
DBK PARTNERS
Victim website: | dbkp.cz |
Victim country: | Czech Republic |
Attacker name: | INC Ransom |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Contracts, financial data, customers’ data, etc. |
Leaked data: | Fully published |
Ransom deadline: | 30th Apr 24 |
Cyber Risk Factor: | 4 |
Image: |
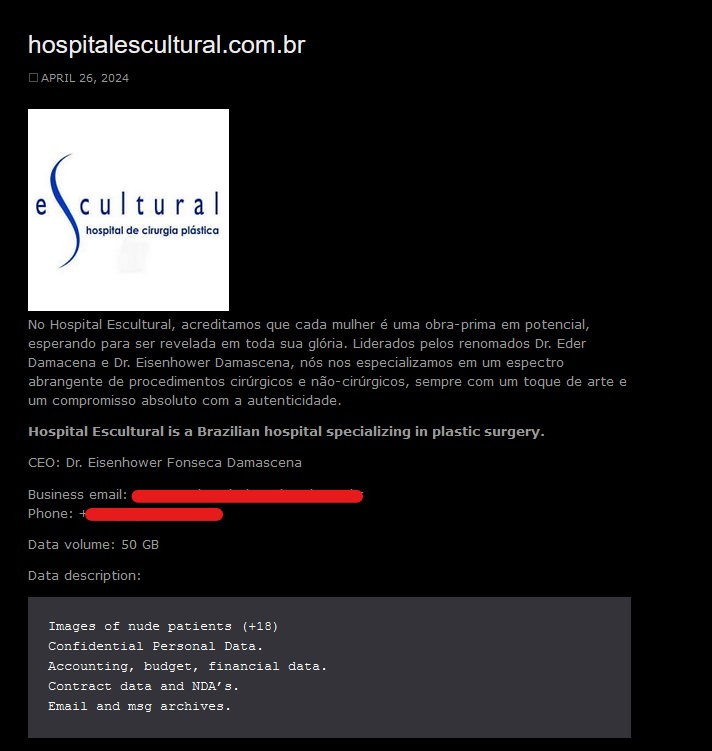
CONCEPTIONS REPRODUCTIVE ASSOCIATES
Victim website: | conceptionsrepro.com |
Victim country: | USA |
Attacker name: | INC Ransom |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Medical records, patient images, customer personal data, medical records, email correspondence, photos, and more. |
Leaked data: | Fully published |
Ransom deadline: | 29th Apr 24 |
Cyber Risk Factor: | 5 |
Image: |
SPRINGFIELD HOUSING AUTHORITY
Victim website: | shamass.org |
Victim country: | USA |
Attacker name: | Ransomware Blog |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 50,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Employees’ information, agreements, customers’ data, accounting data, reports, etc. |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
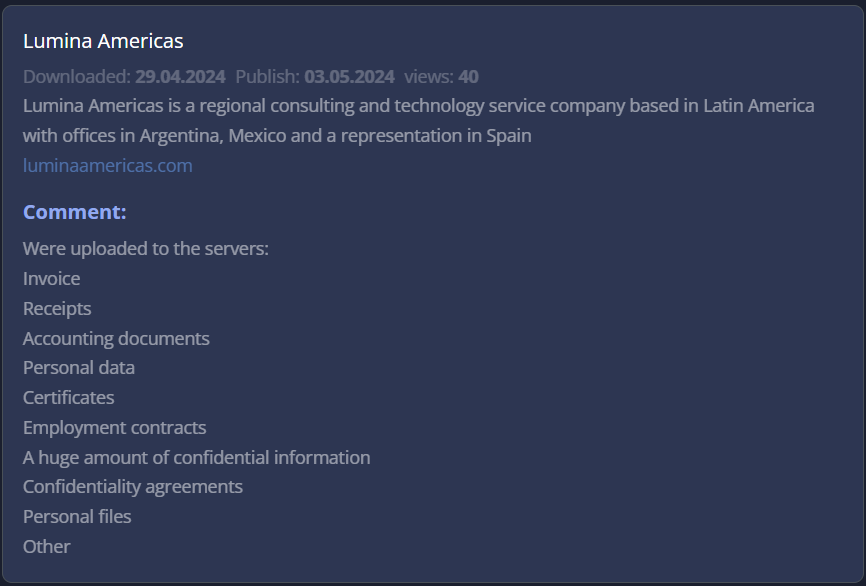
LOPEZ HNOS
Victim website: | lopezhnos.com.ar |
Victim country: | Argentina |
Attacker name: | Rhysida |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | 5 BTC (approx. $ 290,000) |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Financial data, PII documents and other miscellaneous data. |
Leaked data: | Sample |
Ransom deadline: | 08th May 24 |
Cyber Risk Factor: | 4 |
Image: |
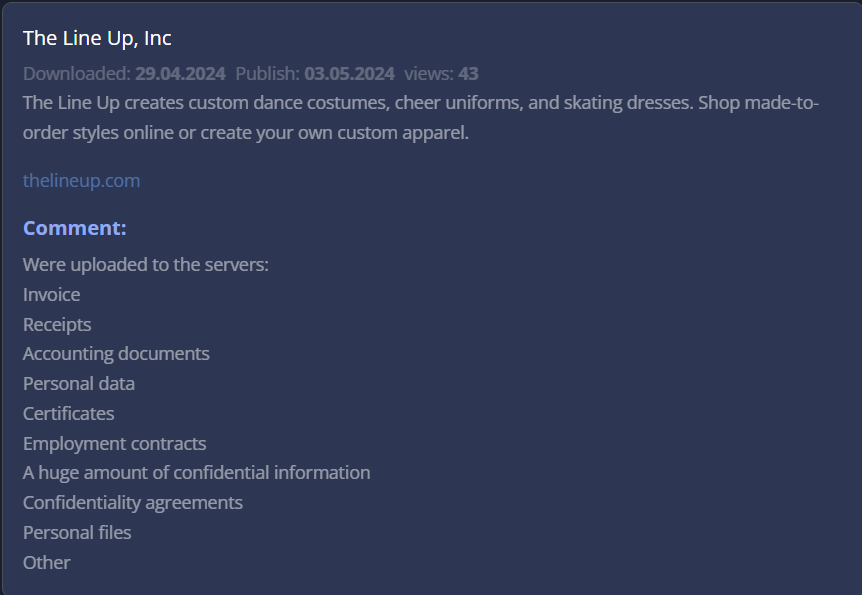
BULLDOG BAG
Victim website: | bulldogbag.com |
Victim country: | Colombia |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 91.7 GB |
Exfiltrated data type: | Employee information, Contracts, Financial Information and etc. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
CREATIVE BUSINESS INTERIORS
Victim website: | creativebusinessinteriors.com |
Victim country: | USA |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 34.5 GB |
Exfiltrated data type: | Confidential agreements, invoices, NDA agreements, employee applications with strictly confidential info, employee personal data (ID, SSN, DL, payroll, Form I9, Form W9), contracts, documents containing confidential information, confidential drawings, financial documents, project documentation, injury reports |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
COCHRANE INTERNATIONAL
Victim website: | cochraneglobal.com |
Victim country: | UAE |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 417.2 GB |
Exfiltrated data type: | Company financial documents, password-protected financial documents (passwords selected), personal data on employees (passports, SSNs, IDs, W9 forms, payrolls, medical information, employment contracts, drivers licenses), personal information on directors, shareholder documents, insurance documents, documents and drawings marked confidential, NDAs and Confidentiality Undertakings, project documentation (project specifications, confidential drawings, contracts, customer correspondence, financial documents), information and correspondence on classified projects (Project X, Project Omaha, military projects) |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
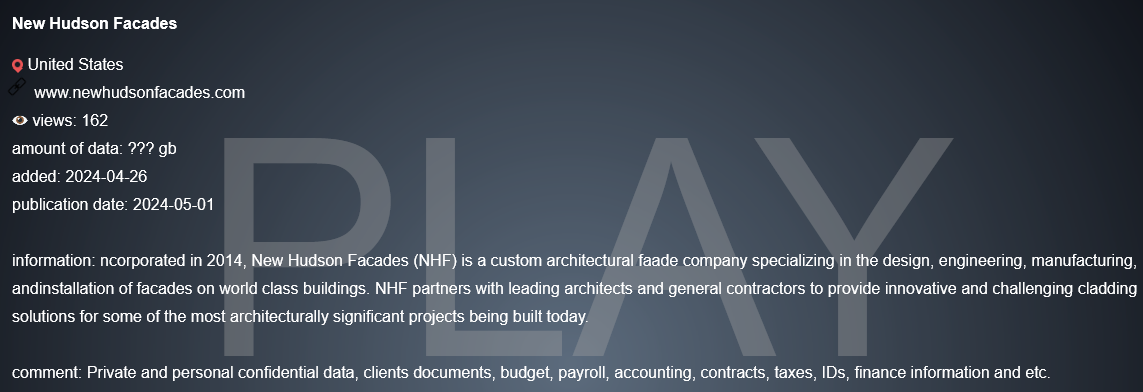
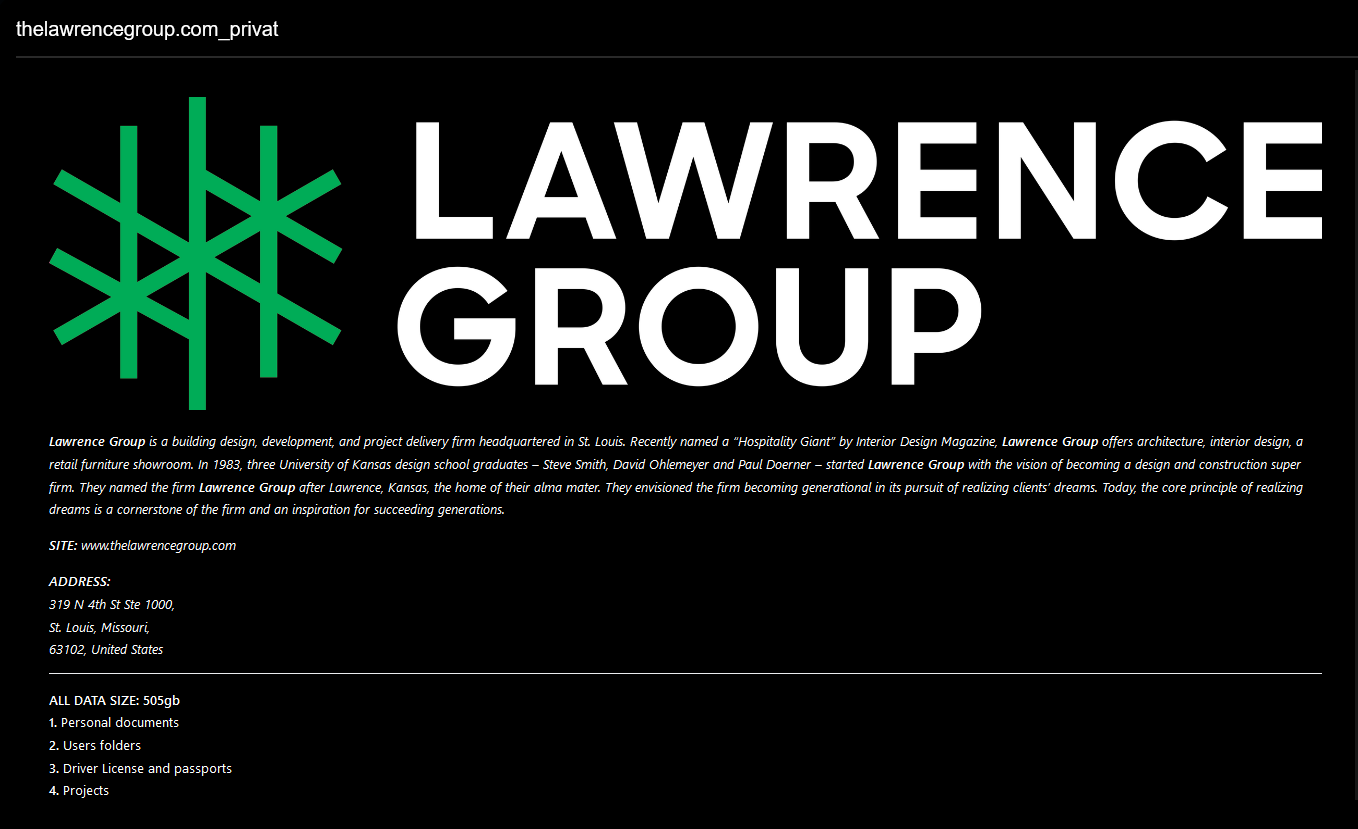
SKENDER CONSTRUCTION
Victim website: | skender.com |
Victim country: | USA |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 615.9GB |
Exfiltrated data type: | Confidential drawings and presentations, confidential agreements, pay stubs and commissions, financial documents, bank documents, invoices, investigation documents, NDA agreements, employee applications with strictly confidential info, personal information on employees (arrests, home addresses, tax documents, ID, SSN, and family info), medical documents (drug tests, medical results), documents containing privileged, confidential information, strictly private and confidential, information on clients and partners, projects, personal data of company’s executives, personally vulnerable photos. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
Y. HATA & CO.
Victim website: | yhata.com |
Victim country: | USA |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 55.9 GB |
Exfiltrated data type: | Confidential agreements, pay stubs and commissions, financial documents, bank documents, invoices, internal incidents, NDA and NCND agreements, employee applications with strictly confidential info, employee personal data (ID, SSN, EIN, tax documents, background checks), contracts, military contracts, personal health information (medical results), documents containing privileged, confidential information, customer database, credit card authorization forms with valid cards, confidential pricing list, personal data of company’s executives, photos and videos of rats in freezer and other proofs of violation of sanitary norms. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
KYUNGCHANG
Victim website: | kyungchang.com |
Victim country: | South Korea |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1.8 TB |
Exfiltrated data type: | Strictly Private and Confidential documents, financial documents, personal information of employees, drawings marked PROPRIETARY AND CONFIDENTIAL, secret designs, proprietary documents of company, joint written consent of board of directors, NDAs, Confidential Agreement, stock agreements. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
AWWG
Victim website: | awwg.com |
Victim country: | Spain |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 204.9 GB |
Exfiltrated data type: | Financial and legal document of the company since 1987, documents contain privileged, confidential information, strictly private and confidential, personally identified information about employees (dismissed and working) (scan: Passports, ID’s, addresses, emails, SSN, phone numbers, job offers), passports of board of directors with notary stamp, NDA Agreements, company accounting and financial data by region, payroll data and commissions, the company’s incidents. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
TRIATHLON GROUP
Victim website: | the-sunlight-group.com |
Victim country: | Germany |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 121.1 GB |
Exfiltrated data type: | N/A |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
TPA GROUP
Victim website: | tpa-group.com |
Victim country: | Slovakia |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 183.3 GB |
Exfiltrated data type: | Email communications with clients that contain confidential agreements, accounting and tax reports for each client, audit documents, company and clients financial documents, clients passports/ID’s and private information, documents contain privileged and confidential information, password-protected documents from a bank, payroll data. |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
SYNOLOGY
Victim website: | synology.com |
Victim country: | Germany |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 51 GB |
Exfiltrated data type: | Miscellaneous data |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
FRENCKEN GROUP
Victim website: | frenckengroup.com |
Victim country: | Singapore |
Attacker name: | Underground Team |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 439.4 GB |
Exfiltrated data type: | Miscellaneous data |
Leaked data: | Fully published |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
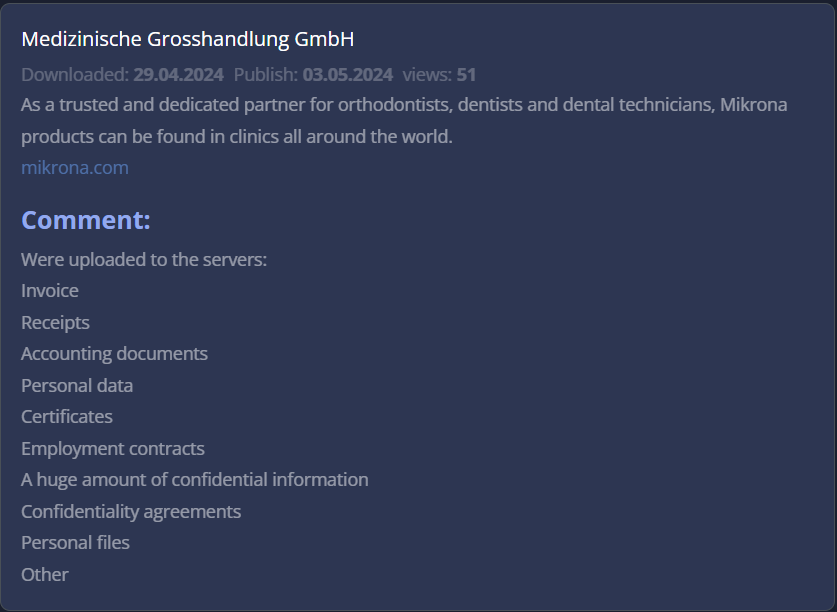
IMEDI L
Victim website: | imedil.ge |
Victim country: | Georgia |
Attacker name: | Akira |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 18 GB |
Exfiltrated data type: | Signed agreements, IDs with personal data, accounting information, payments\bank transactions details. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
Stay safe!
Hackmanac Team!
Latest news
HACKS OF TODAY 02/05/2024
Today's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
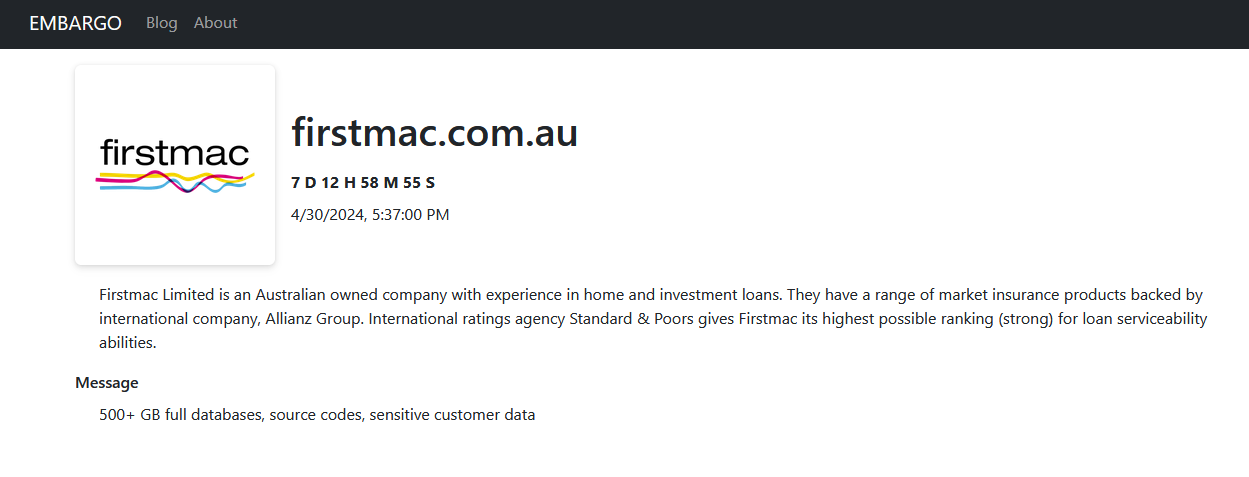
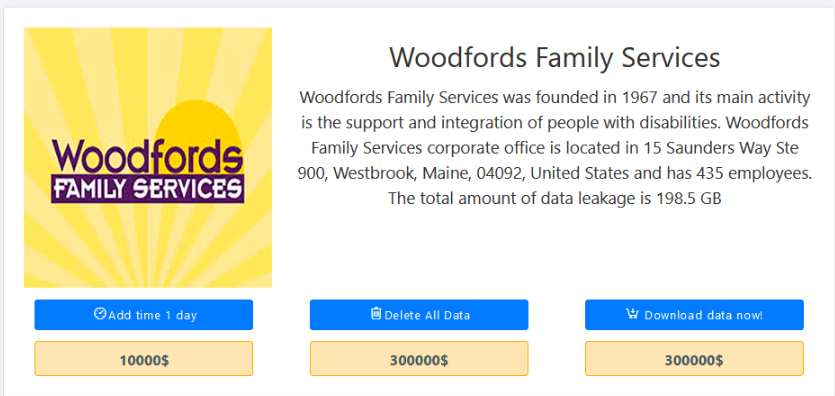
Read MoreHACKS OF TODAY 30/04/2024 – 01/05/2024
Today's HOT includes 29 victims by the notorious LockBit 3.0, BlackBasta, Embargo, Medusa, Akira, Play, Snatch, Everest, Qilin, Cl0p and RansomHub gangs. The average Cyber...
Read MoreHACKS OF TODAY 27-28-29/04/2024
Today's HOT includes 30 ransomware victims by the notorious Apos, Play, LockBit 3.0, RansomHub, INC Ransom, Black Suit, Eraleig, Qiulong, Hunters International, 8Base, BlackBasta and Space Bears...
Read More