news
HACKS OF TODAY 25-26/12/2023

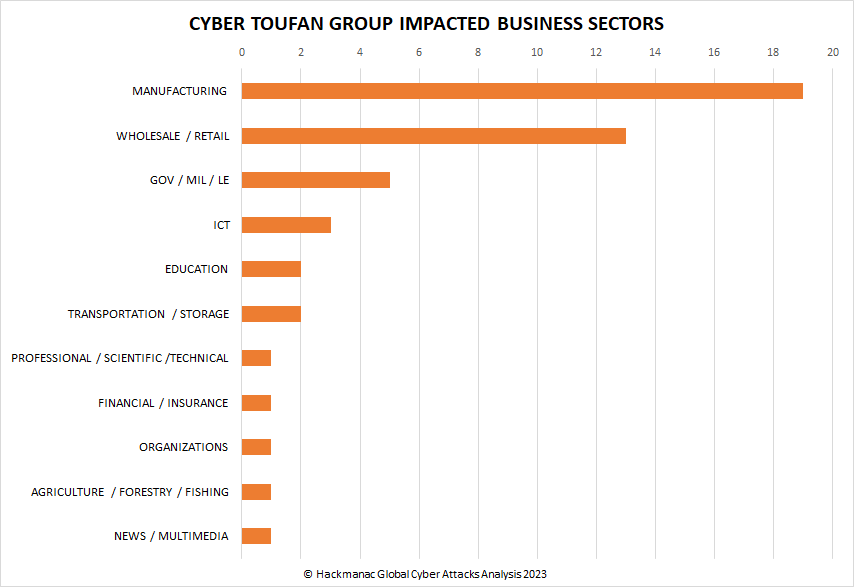
Today’s HOT includes 15 victims by the notorious LockBit 3.0, Cyber Toufan, Stormous, Black Suit, Rhysida and Akira gangs.
The average Cyber Risk Factor is 3.9.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
HENDELS
Victim website: | hendelsinc.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 9th Jan 24 |
Cyber Risk Factor: | 3 |
Image: |
TECNIFIBRE
Victim website: | tecnifibre.com |
Victim country: | France |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous including financial data, invoices, etc. |
Leaked data: | Sample |
Ransom deadline: | 3rd Jan 24 |
Cyber Risk Factor: | 4 |
Image: |
ZAMFIRESCU RACOTI VASILE & PARTNERS
Victim website: | zrvp.ro |
Victim country: | Romania |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous including financial data, confidential documents, etc. |
Leaked data: | Sample |
Ransom deadline: | 9th Jan 24 |
Cyber Risk Factor: | 4 |
Image: |
PICKENS COUNTY
Victim website: | co.pickens.sc.us |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 3rd Jan 24 |
Cyber Risk Factor: | 4 |
Image: |
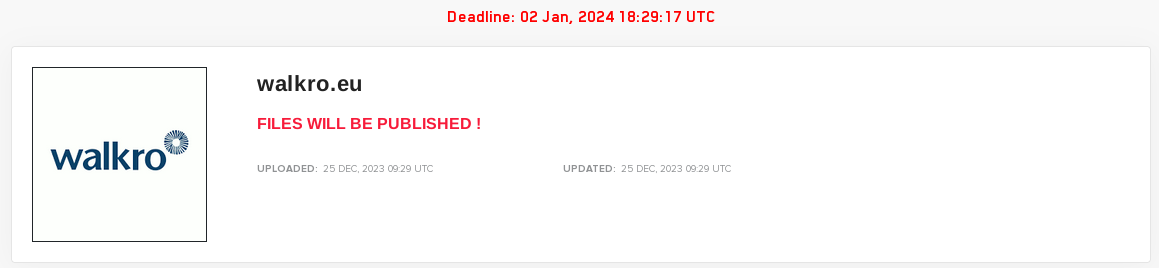
WALKRO
Victim website: | walkro.eu |
Victim country: | Netherlands |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 2nd Jan 24 |
Cyber Risk Factor: | 3 |
Image: |
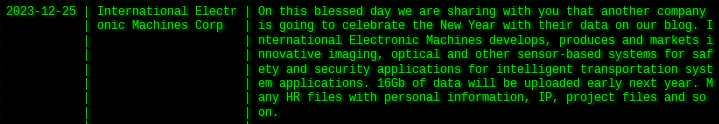
INTERNATIONAL ELECTRONIC MACHINES CORP
Victim website: | iem.net |
Victim country: | USA |
Attacker name: | Akira |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 16 GB |
Exfiltrated data type: | HR files with personal information, intellectual property, and project files |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
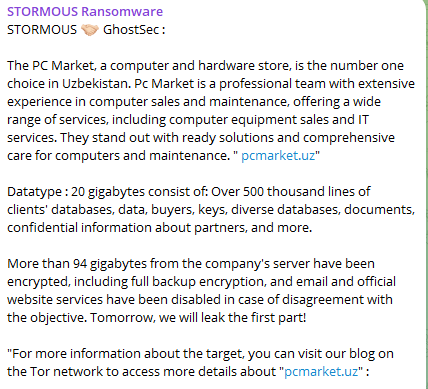
PC MARKET
Victim website: | pcmarket.uz |
Victim country: | Uzbekistan |
Attacker name: | Stormous |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 94 GB |
Exfiltrated data type: | Clients’ database, buyers, keys, confidential information, etc. |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
BLAINE COUNTY SCHOOL DISTRICT
Victim website: | blaineschools.org |
Victim country: | USA |
Attacker name: | Black Suit |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
TSHWANE UNIVERSITY OF TECHNOLOGY
Victim website: | tut.ac.za |
Victim country: | South Africa |
Attacker name: | Rhysida |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | 20 BTC ($ 855,0000) |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 2nd Jan 24 |
Cyber Risk Factor: | 5 |
Image: |
ABDALI HOSPITAL
Victim website: | abdalihospital.com |
Victim country: | Jordan |
Attacker name: | Rhysida |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | 10 BTC ($ 428,000) |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Financial documents, invoices, personal data, etc. |
Leaked data: | Sample |
Ransom deadline: | 2nd Jan 24 |
Cyber Risk Factor: | 5 |
Image: |
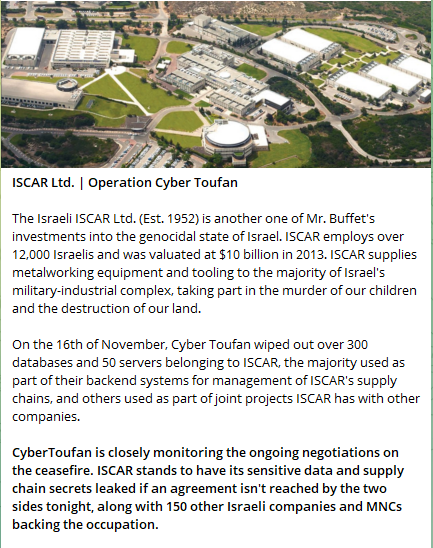
PALRAM INDUSTRIES
Victim website: | palram.com |
Victim country: | Israel |
Attacker name: | Cyber Toufan |
Attacker class: | Hacktivism |
Attack technique: | Data breach |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Database |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
ISRAELI SECURITIES AUTHORITY (16th November)
Victim website: | isa.gov.il |
Victim country: | Israel |
Attacker name: | Cyber Toudan |
Attacker class: | Hacktivism |
Attack technique: | Data breach |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Systems wiped |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
Image: |
ICL GROUP
Victim website: | icl-ip.com |
Victim country: | Israel |
Attacker name: | Cyber Toufan |
Attacker class: | Hacktivism |
Attack technique: | Data breach |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Customers’ database, suppliers, etc. |
Leaked data: | Sample |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
A.R.I.
Victim website: | ari.co.il |
Victim country: | Israel |
Attacker name: | Cyber Toufan |
Attacker class: | Hacktivism |
Attack technique: | Data breach |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Database of the company, including customers, products, and other details |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
Image: |
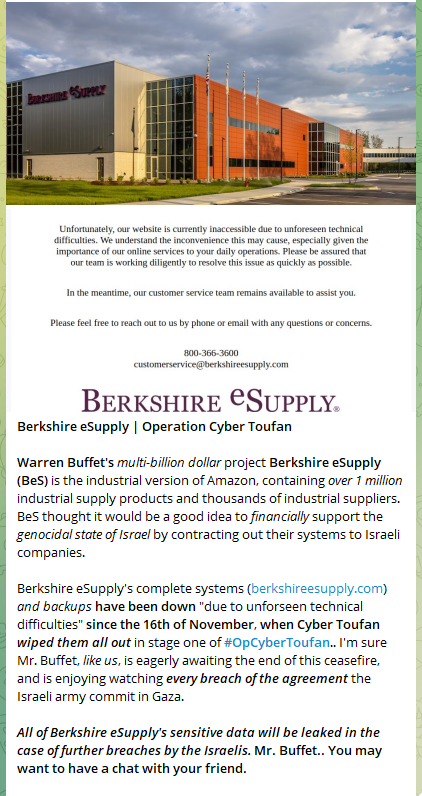
CAROLINA LEMKE BERLIN
Victim website: | carolinalemke.com |
Victim country: | Israel |
Attacker name: | Cyber Toufan |
Attacker class: | Hacktivism |
Attack technique: | Data breach |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Database |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: |
Stay safe!
Hackmanac Team!
Latest news
HACKS OF TODAY 08/05/2024
Today's HOT includes 20 ransomware victims by the notorious Metaencryptor, Qilin, LockBit 3.0, Hunters International, INC Ransom, RansomHub, Medusa, Black Suit, APT73 and dAn0n gangs....
Read MoreHACKS OF TODAY 07/05/2024
Today's HOT includes 66 victims by the notorious Black Suit, Akira, BianLian, DarkVault, Play, RansomHub, INC Ransom, Qilin, Abyss and LockBit 3.0 gangs. The average...
Read MoreHACKS OF TODAY 03-04-05-06/05/2024
Today's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
Read More