news
SIEGEDSEC: FOURTH OPERATION AGAINST ISRAEL

SiegedSec is a hacktivist group that emerged during Russia’s invasion of Ukraine and recently claimed to have breached NATO and subsequently leaked unclassified documents online.
The group is reportedly conducting their fourth attack on Israel, intensifying their cyber offensive efforts.
The latest operation
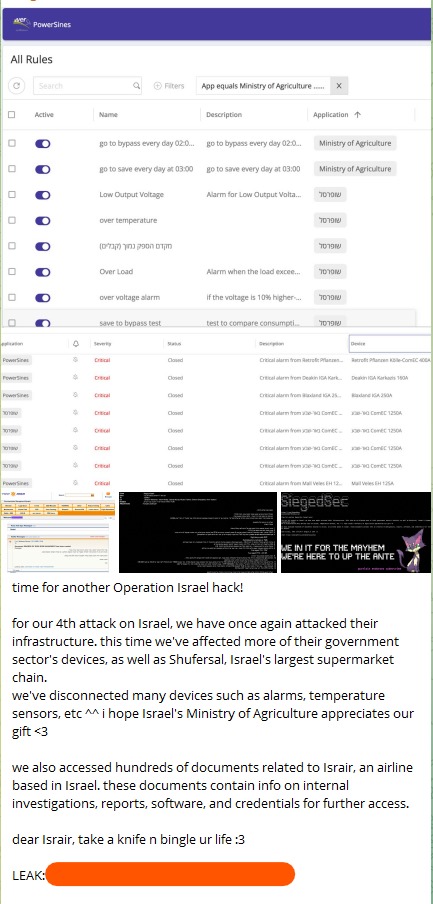
In their latest operation, they claim to have compromised a broader range of systems within Israel’s government sector and targeted Shufersal, Israel’s largest supermarket chain.
This operation has expanded further, with SiegedSec also asserting that they have gained access to numerous documents associated with Israir, an Israeli airline based in Tel Aviv.
The exfiltrated documents, reportedly containing critical information such as internal investigations, reports, software, and credentials, have been published in Telegram SiegedSec channell for a total of 1.26 GB.
The previous cyber offenses
This attack on Israel is part of a series of significant cyber offenses.
Initially, SiegedSec exfiltrated the customer database of Bezeq, an Israeli telecommunications company. Data included around 50,000 customers’ full names, email addresses, and phone numbers.
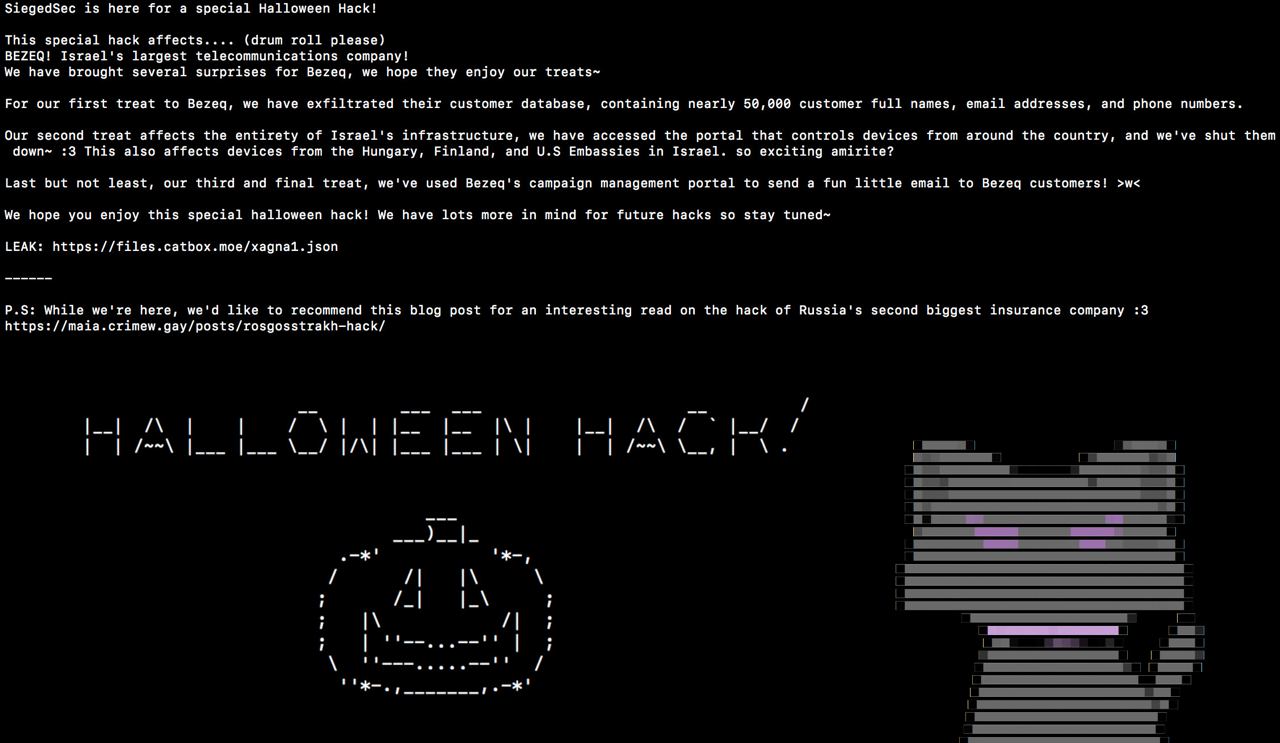
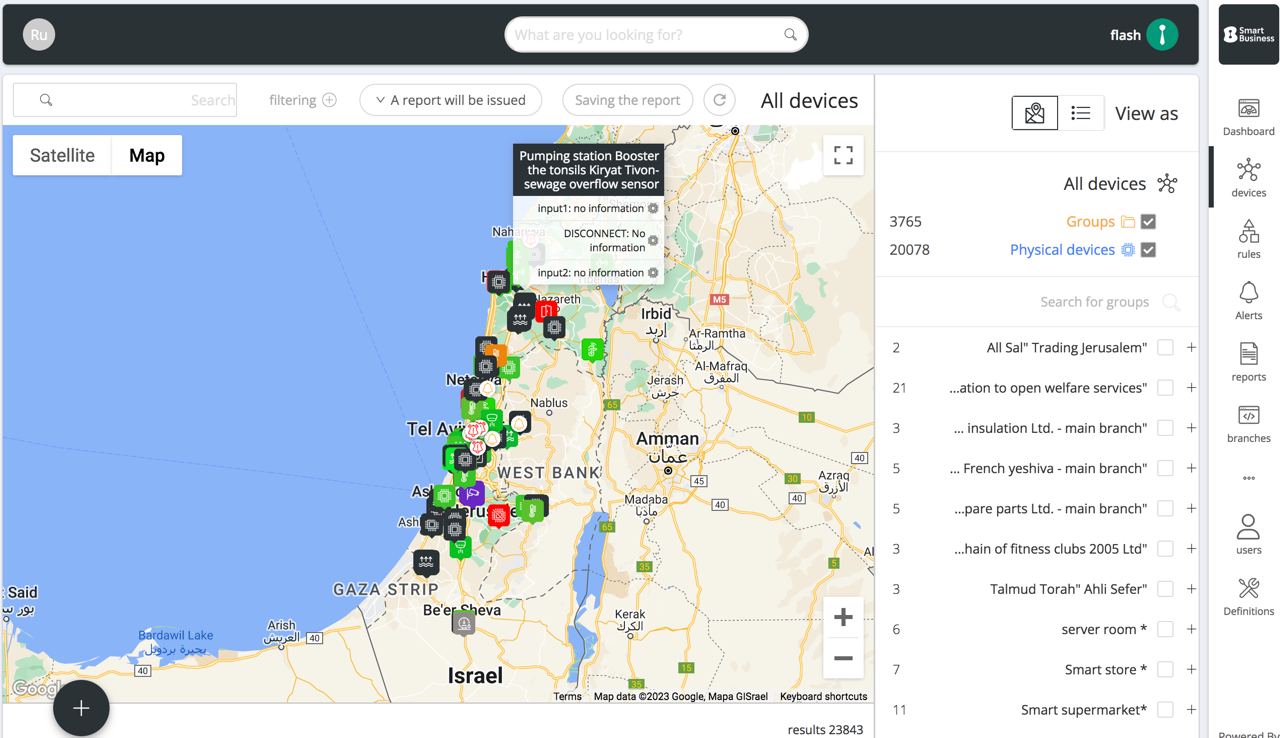
Their second operation had a broader scope, targeting Israel’s entire infrastructure.
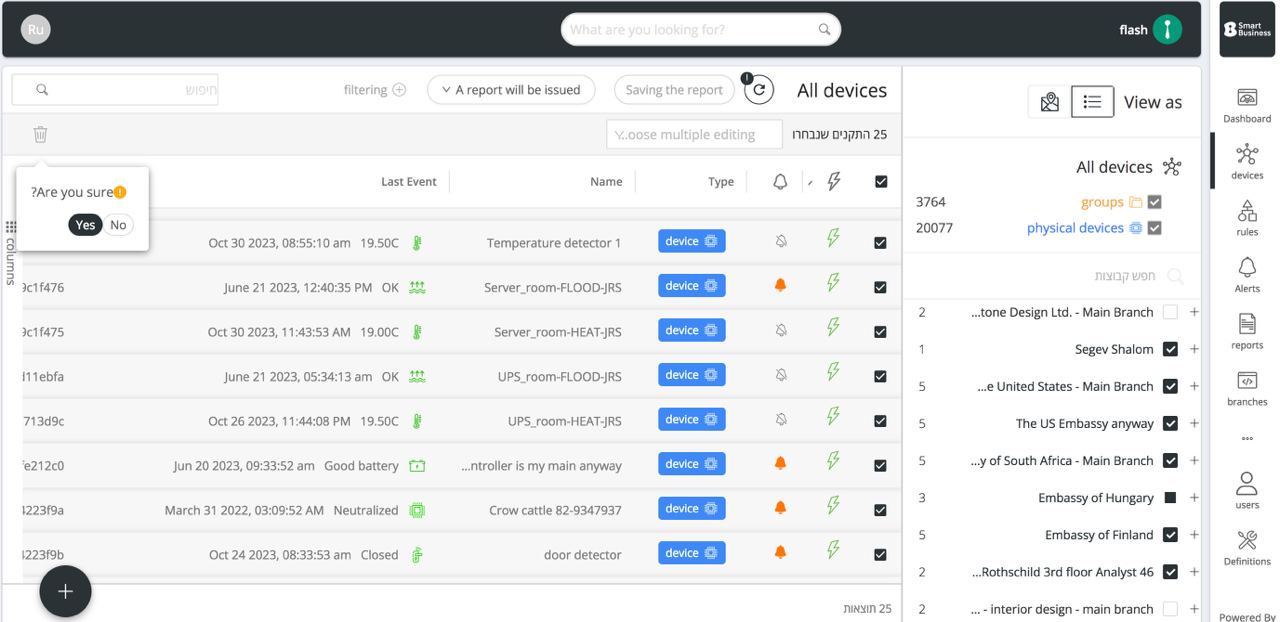
In fact they stated to have accessed and shut down the portal controlling devices throughout the country, impacting operations even in the Hungarian, Finnish, and U.S. Embassies in Israel.
In their third attack, SiegedSec targeted Cellcom, one of Israel’s leading telecommunications companies, breaching the customer support panel.
They stated to have gained access to nearly 180,000 customer records.

This attack was conducted in collaboration with Anonymous Sudan further showcasing SiegedSec’s expanding reach and capabilities.
In this Information Warfare scenario, an increasing number of cybercriminal groups are participating in the #OpIsrael operation, further destabilizing the war landscape between Israel and Hamas.
Latest news
HACKS OF TODAY 02/05/2024
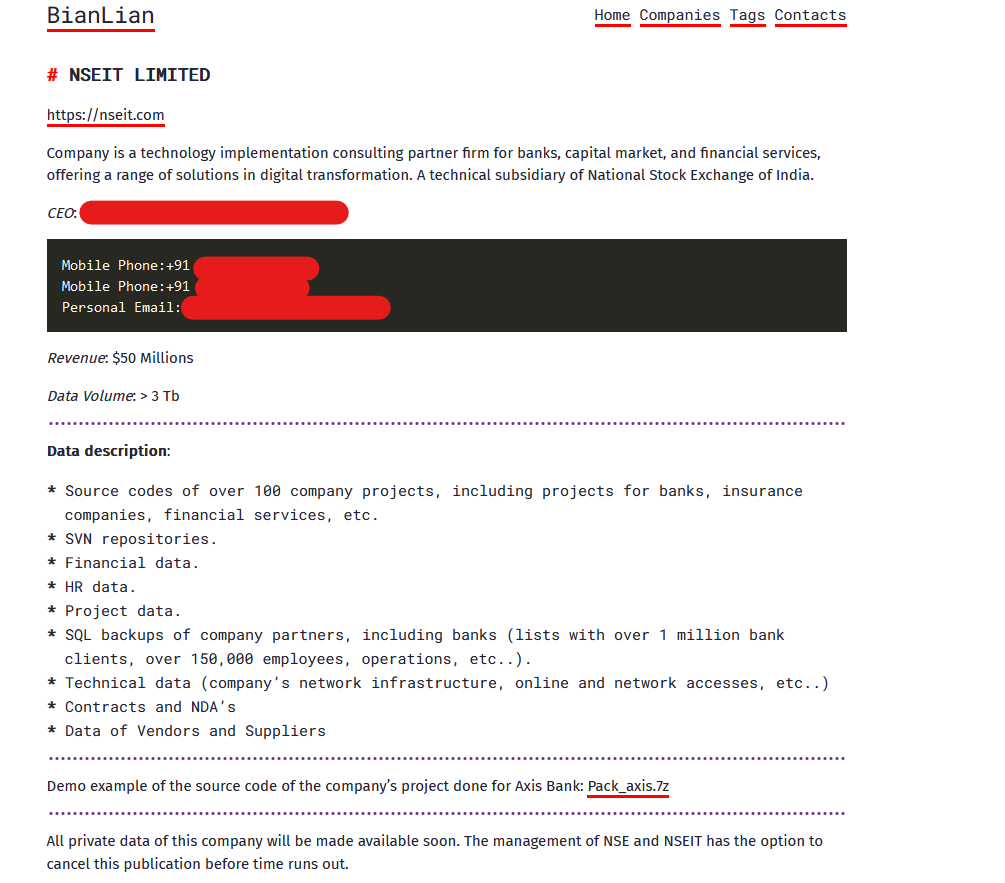
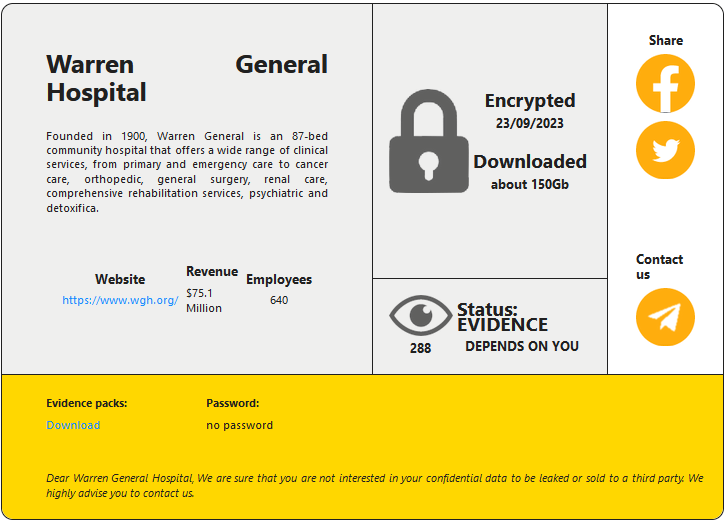
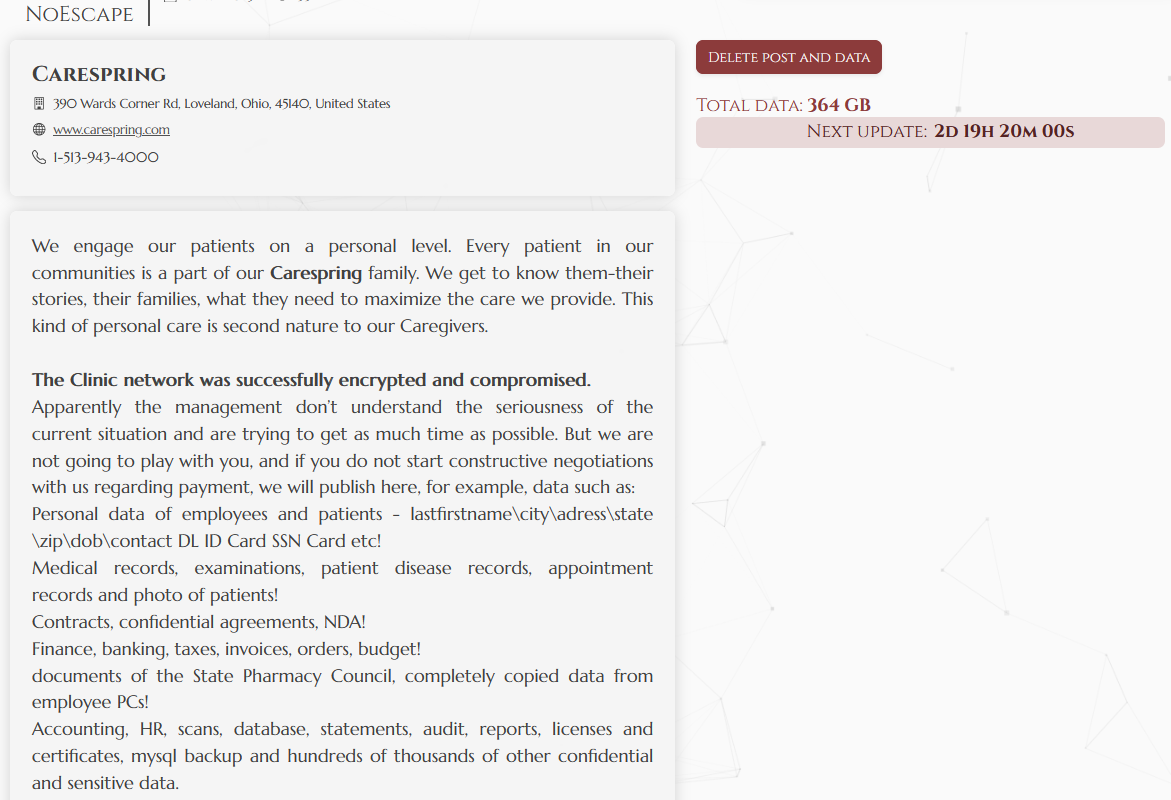
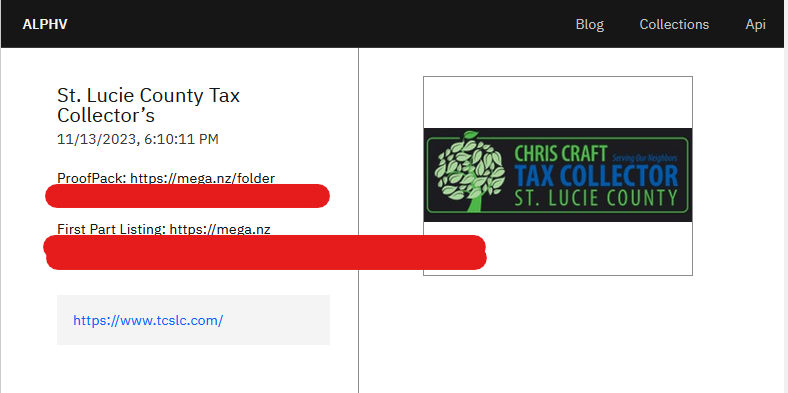
Today's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
Read MoreHACKS OF TODAY 30/04/2024 – 01/05/2024
Today's HOT includes 29 victims by the notorious LockBit 3.0, BlackBasta, Embargo, Medusa, Akira, Play, Snatch, Everest, Qilin, Cl0p and RansomHub gangs. The average Cyber...
Read MoreHACKS OF TODAY 27-28-29/04/2024
Today's HOT includes 30 ransomware victims by the notorious Apos, Play, LockBit 3.0, RansomHub, INC Ransom, Black Suit, Eraleig, Qiulong, Hunters International, 8Base, BlackBasta and Space Bears...
Read More