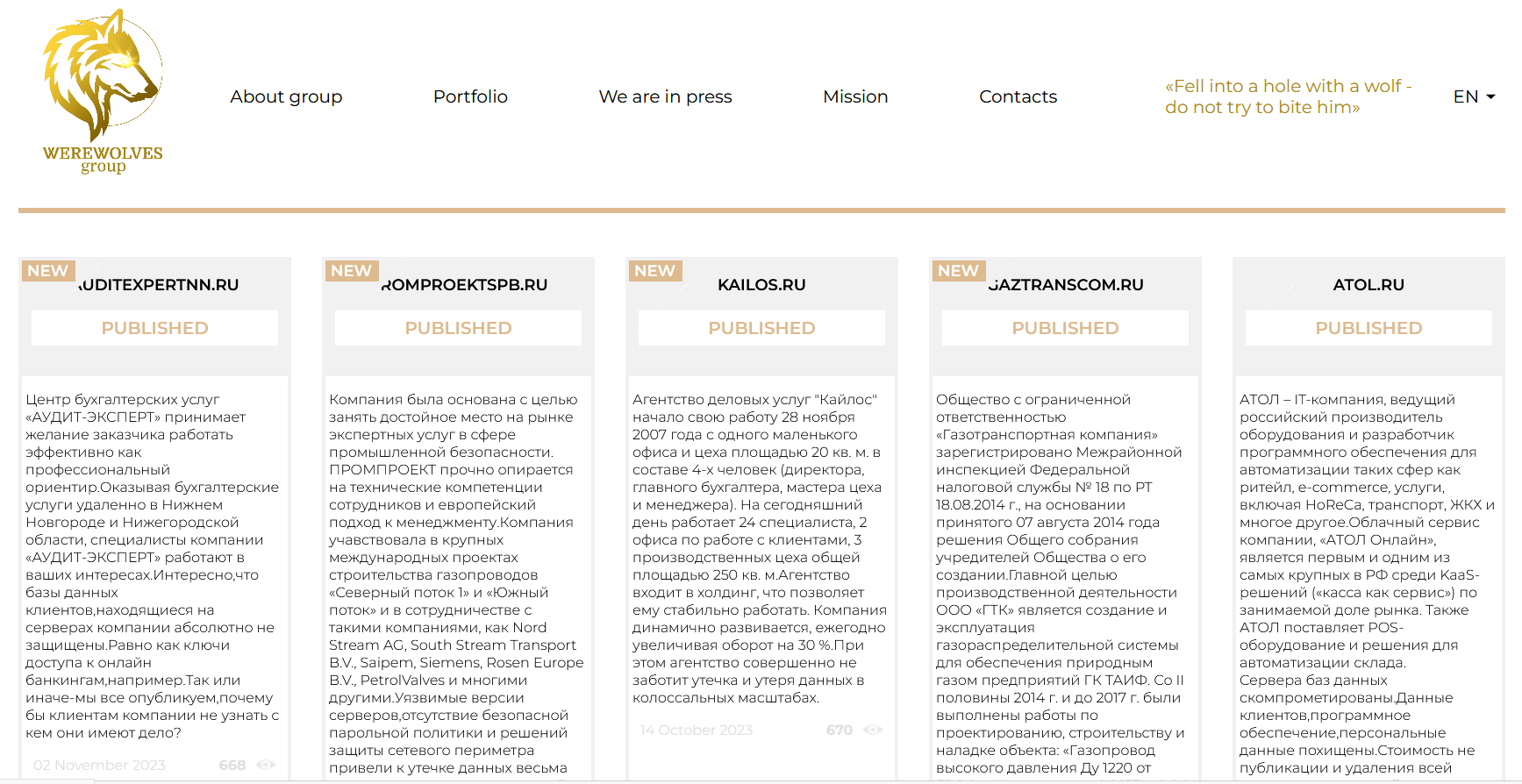
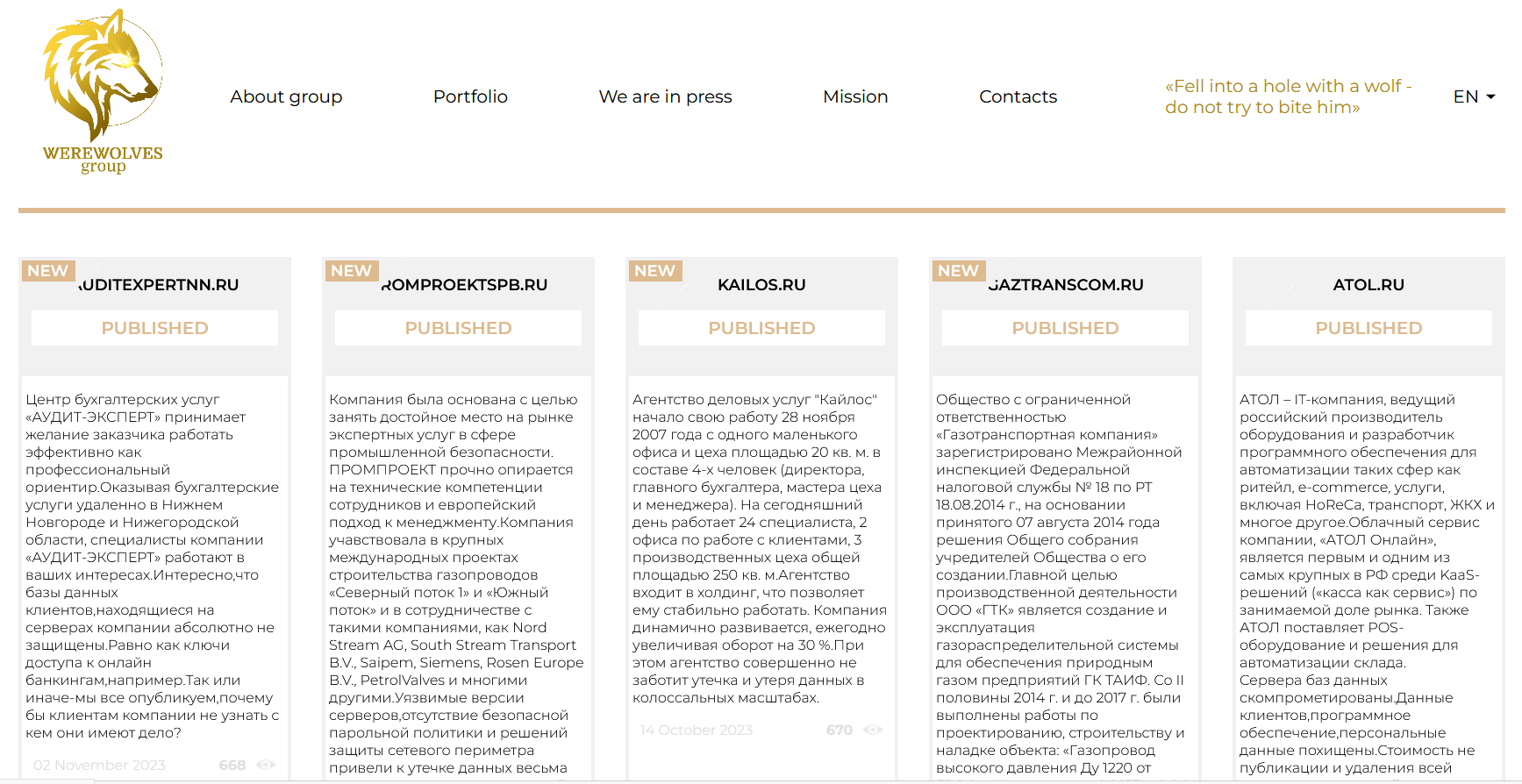
The WereWolves ransomware group has been recently added to our database, and a first look at it’s data leak site reveals that 21 victims have been listed; 14 located in Russia along with another 7 across the USA, France, Netherlands, Germany, Serbia and Macedonia, apparently targeted between May 18th and November 2nd, 2023.
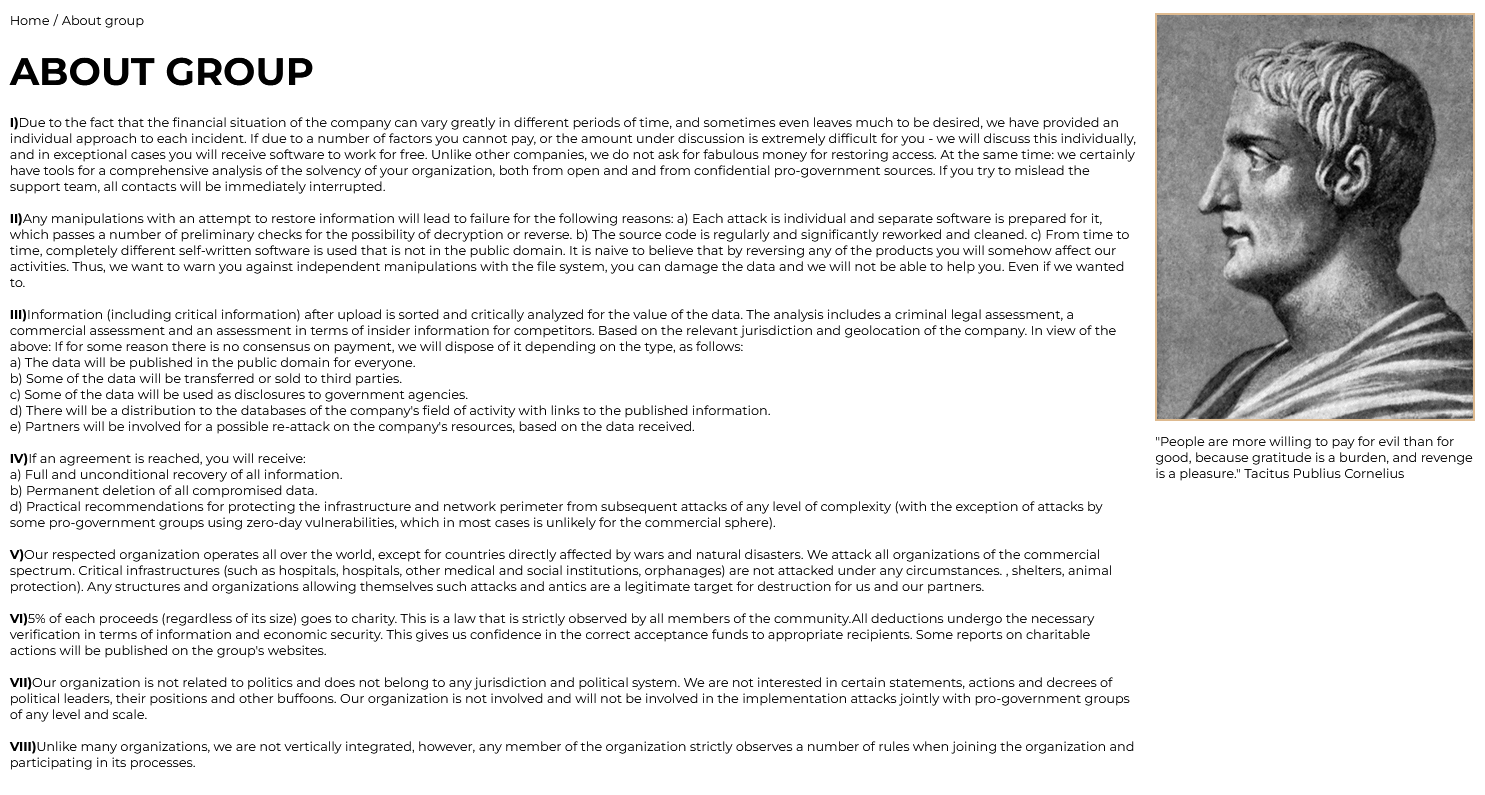
In the “About Us” section, the group portrays itself as an organization committed to cyber attacks and ransomware operations, offering tailored negotiations for data recovery while threatening of punitive measures if agreements are not met. Their “Mission” section states the following: “We see our mission in strengthening the cyber immunity of companies around the world, and this is definitely worth the money.”
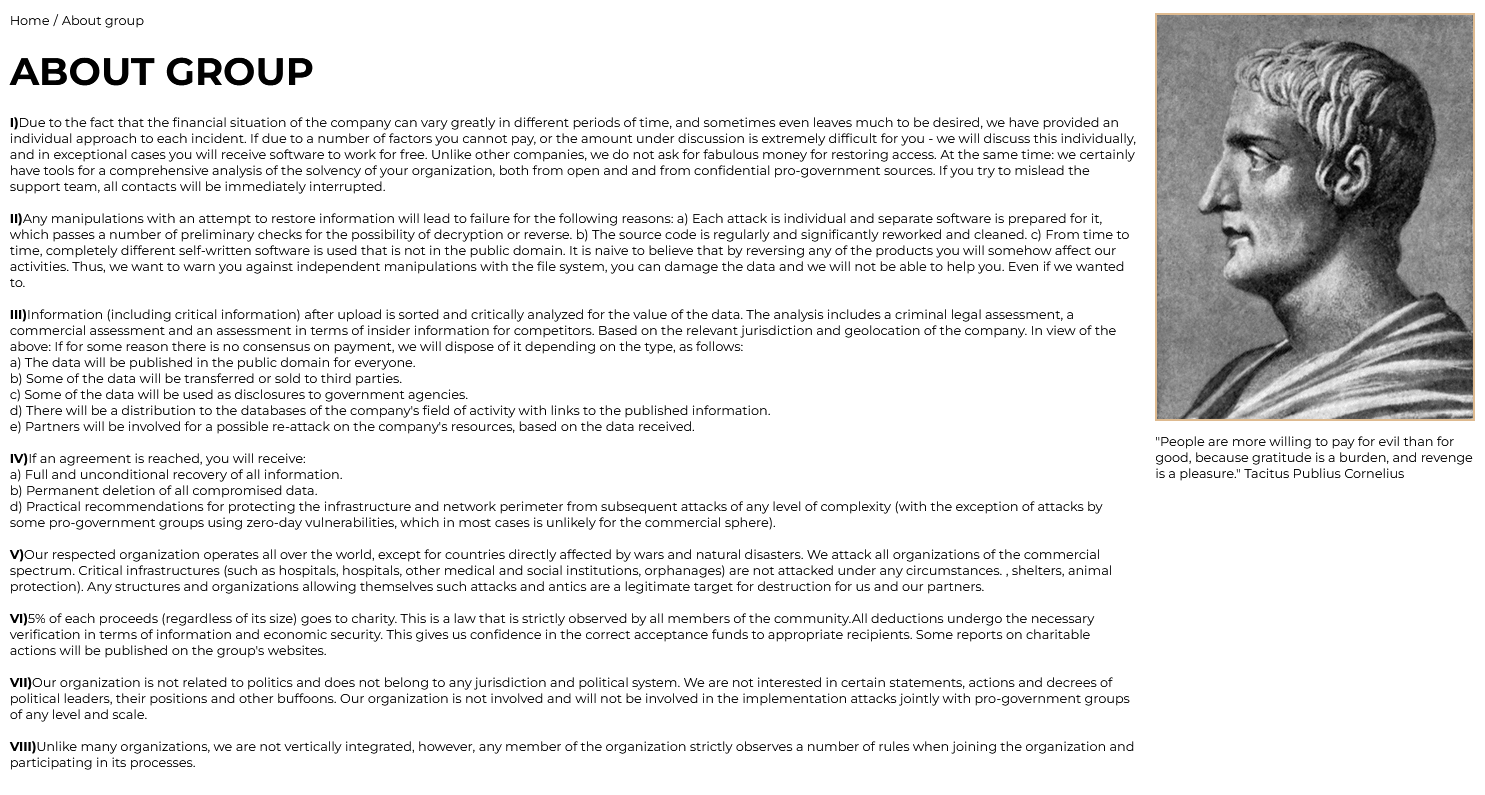
Additionally, they feature a “Portfolio” section inviting security researchers, ethical, and unethical hackers worldwide to join their bug-finding bounty program. This program focuses on website vulnerabilities, doxing, software vulnerabilities, TOX vulnerabilities, unique ideas, and TOR vulnerabilities, with bounties ranging from $1,000 to $1 million.
Seeking public attention, the cybercrime group has published a 2022 article from Ghana Business News, claiming responsibility for an attack on the Electricity Company of Ghana (ECG). Following a ransomware attack, ECG was reportedly unable to buy power, resulting in several days of power outages.
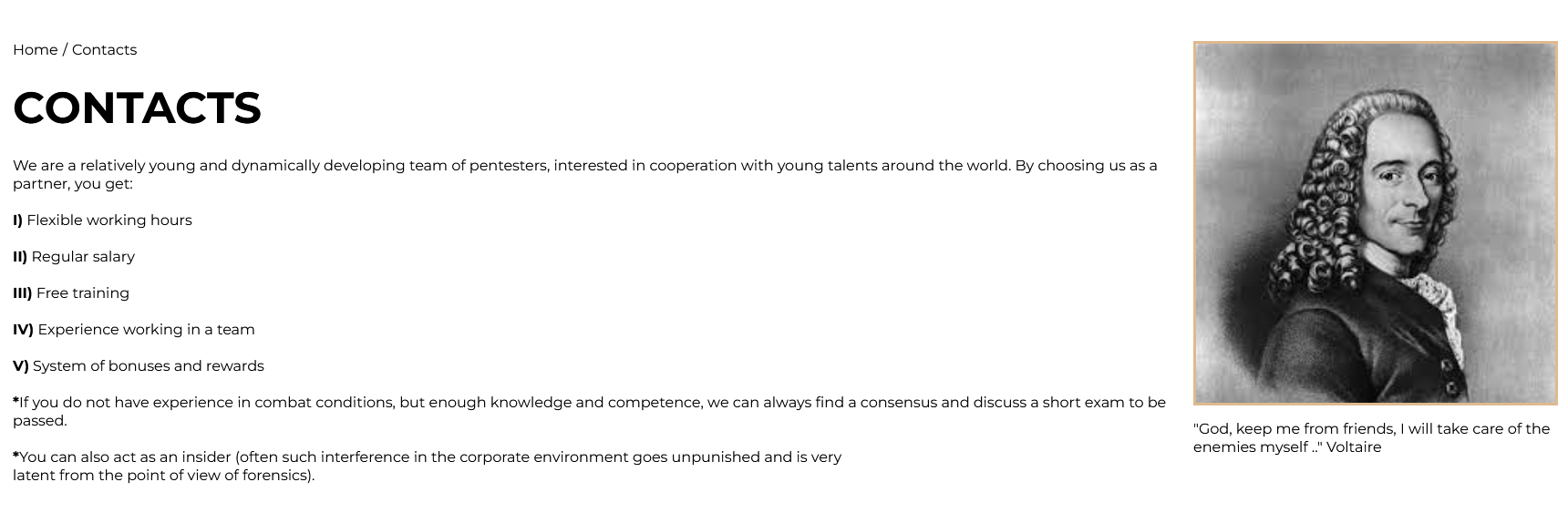
Their blog also includes a recruitment call for new members with hacking skills. They promise flexible working hours, regular salary, and training, targeting both seasoned hackers and those with knowledge but less practical experience. A deposit of 1 Bitcoin is required as a security measure to deter unsuitable candidates like law enforcement or journalists. Applicants must demonstrate their hacking prowess and readiness to commit to cyber attacks immediately upon joining, with the organization emphasizing a structured recruitment process focused on skills, experience, and dedication to their illicit activities.
Although the last recorded activity was on November 2nd, by looking at the timeline of their attacks the group is likely to be still active, requiring a continuous monitoring.
Targets Analysis
An analysis of the attacks published by WereWolves provides us with an overview of the types of targets affected:

With 28.6%, the Professional/Scientific/Technical sector secures the leading position, closely followed by both the Financial/Insurance and Hospitality sectors, each holding a share of 14.3%. Subsequent to these are the WholesaleRetail, Telecommunications, and InformationCommunicationTechnology sectors, each accounting for 9.5%. Finally, the Manufacturing, EnergyUtilities, and OtherServices sectors each comprise 4.7%.
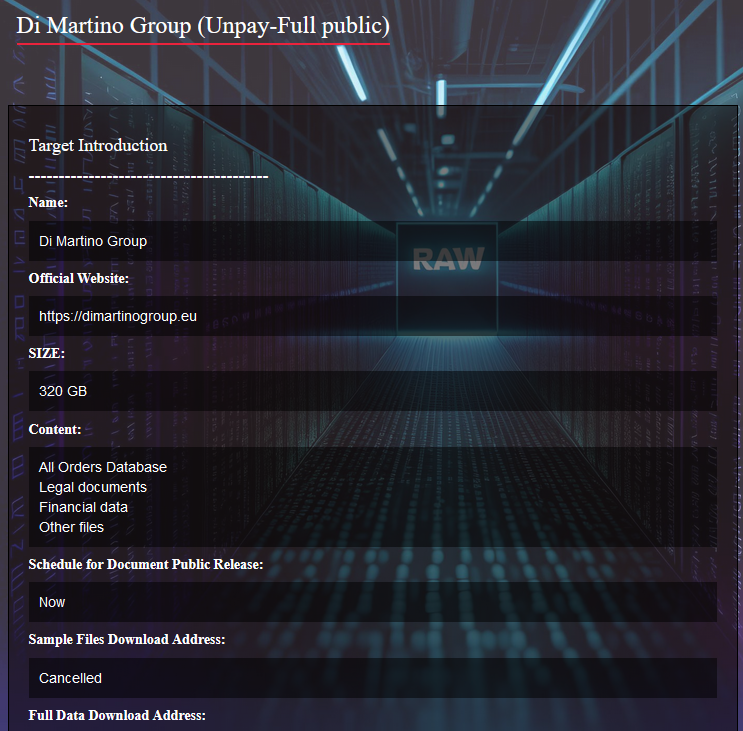
A LockBit affiliate?
Interestingly, among the victims listed on the blog, 6 appear to be copy-pasted from attacks previously conducted by LockBit (Agency for Electronic Communications, Metalnet, Interfides, La Poste Mobile, Emprint, Big Centers). The posts for these 6 victims indeed showcase identical samples and the same amount of data exfiltrated.
Hundreds of terabytes exfiltrated
Other impacted companies have captured our attention, this time for the extreme quantity of data that WereWolves claims to have exfiltrated. In the post detailing the attack on Maritime Bank, the cybercriminals assert that they have exfiltrated 120 Terabytes of data, and for CarMoney, 60 Terabytes. This volume of data is rarely seen even among the largest criminal organizations. As always, these statements are pending confirmation.
(Update 21/12/2023): WereWolves encrypts company data using a version of the LockBit3 ransomware code
BIG Centers, Agency for Electronic Communications, Metalnet, Interfides, Easy Loan, QB2B, Emprint, La Poste Mobile, acac Fitness & Wellness, AMAKS Hotels & Resorts, Aurora Store, AMAKS Congress Hotel Khabarovsk, Maritime Bank, CROC Incorporated, CarMoney, RoomHotel, ATOL, Gas Transportation Company, Kailos, Promproekt, Audit-Expert.
Conclusion
Confirmation or denial of WereWolves’ attacks would be a decisive factor in assessing the actual threat posed by this ransomware group, which until now has remained in the shadows. Moreover, given the 6 attacks coinciding with those of LockBit, an affiliation between the two criminal gangs cannot be ruled out. Continuous monitoring will reveal the true nature of WereWolves.
The detailed list of the targeted victims:
BIG CENTERS
Victim website: | bigcenters.rs |
Victim country: | Serbia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Financial documents |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
AGENCY FOR ELECTRONIC COMMUNICATIONS
Victim website: | aek.mk |
Victim country: | Macedonia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 118 GB |
Exfiltrated data type: | Financial documents, PII, credit cards, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
METALNET
Victim website: | metalnet.nl |
Victim country: | Netherlands |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 49 GB |
Exfiltrated data type: | Technical designs, invoices and financial documents, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
INTERFIDES
Victim website: | interfides.de |
Victim country: | Germany |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Projects, financial data, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
EASY LOAN
Victim website: | lzaim38.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 45,000 |
Exfiltrated data amount: | Miscellaneous documents including passports and photos, etc. |
Exfiltrated data type: | N/A |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
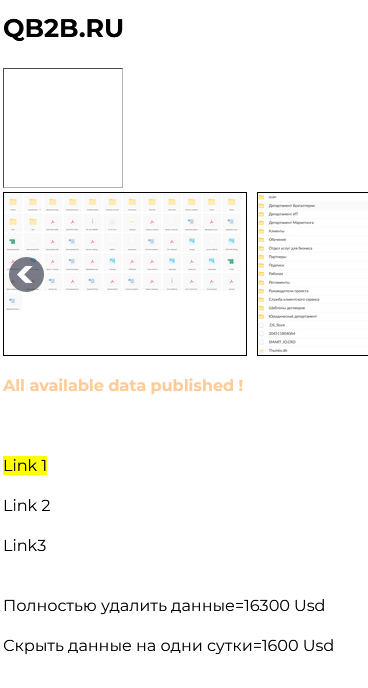
QB2B
Victim website: | qb2b.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 16,300 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including scans and passports, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 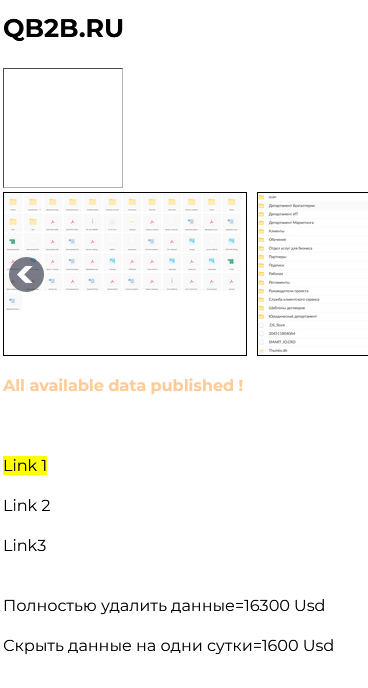
|
EMPRINT
Victim website: | emprint.com |
Victim country: | USA |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: | 
|
LA POSTE MOBILE
Victim website: | lapostemobile.fr |
Victim country: | France |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 3 |
Image: | 
|
ACAC FITNESS & WELLNESS
Victim website: | acac.com |
Victim country: | USA |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: | 
|
AMAKS HOTELS & RESORTS
Victim website: | krasnoyarsk.amaks |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 4,000 |
Exfiltrated data amount: | 1.0 TB |
Exfiltrated data type: | Miscellaneous documents including videos and photos, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
AURORA STORE
Victim website: | avrora24.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 130,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: | 
|
AMAKS CONGRESS HOTEL KHABAROVSK
Victim website: | habarovsk.amaks |
Victim country: | N/A |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 3,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents including videos and photos, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
MARITIME BANK
Victim website: | maritimebank.com |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 1,000,000 |
Exfiltrated data amount: | 120 TB |
Exfiltrated data type: | Clients’ data |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 5 |
Image: | 
|
CROC INCORPORATED
Victim website: | croc.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 170,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
CARMONEY
Victim website: | carmoney.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 60 TB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 5 |
Image: | 
|
ROOMHOTEL
Victim website: | roomhotel-sochi.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 2 |
Image: | 
|
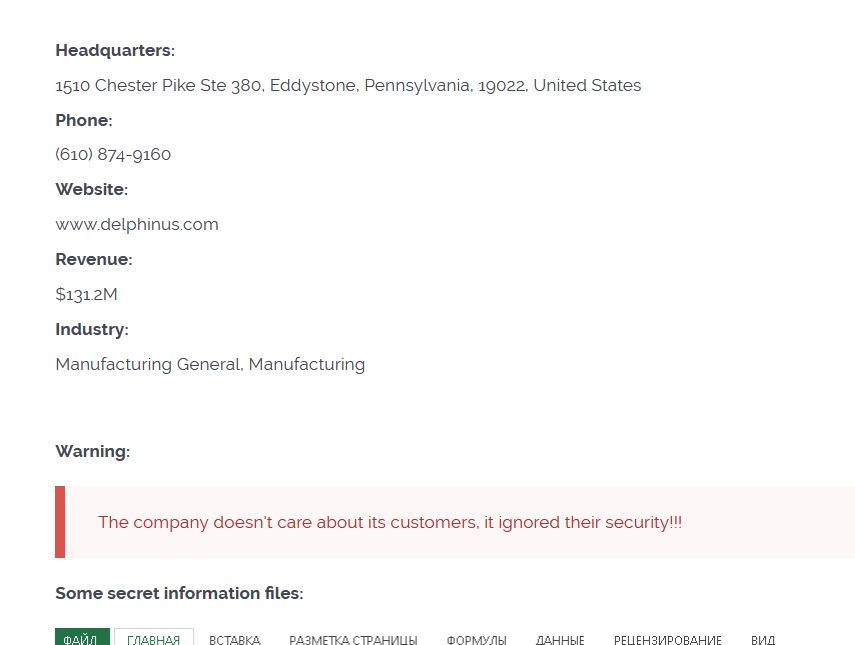
ATOL
Victim website: | atol.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 450,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Database, clients’ data, personal data, software data, etc. |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 5 |
Image: | 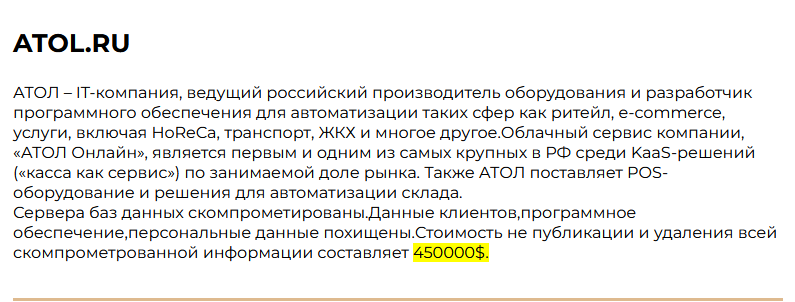
|
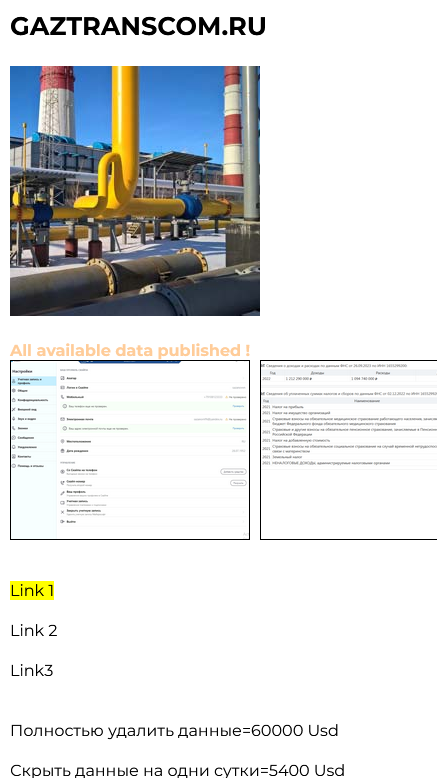
GAS TRANSPORTATION COMPANY
Victim website: | gaztranscom.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 60,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Clients’ data |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 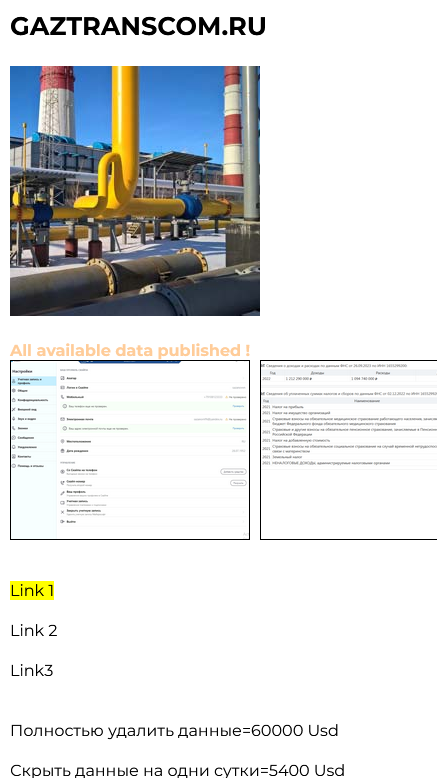
|
KAILOS
Victim website: | kailos.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | $ 6,000 |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous documents |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 
|
PROMPROEKT
Victim website: | promproektspb.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Clients’ data |
Leaked data: | / |
Ransom deadline: | Expired |
Cyber Risk Factor: | 4 |
Image: | 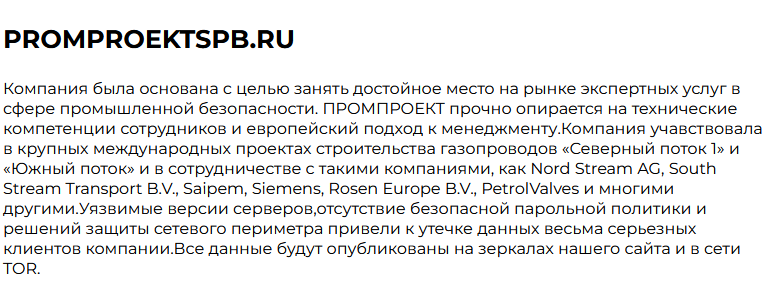
|
AUDIT-EXPERT
Victim website: | auditexpertnn.ru |
Victim country: | Russia |
Attacker name: | WereWolves |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Clients’ data |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 3 |
Image: | 
|
Stay Cyber Safe!