news
LOSTTRUST RANSOMWARE OPERATION ANALYSIS
LostTrust is a recently discovered ransomware group with some interesting characteristics.
They started their operations probably in late 2022, but became known only on September 2023 when they started to post victims on their newly created DLS (Data Leak Site).
Here is our analysis of the group main modus operandi.
The cybercrime group
LostTrust describe itself as a “a group of young people who identify themselves as specialists in the field of network security with at least 15 years of experience.”
On their DLS they clarify that they have nothing to do with political groups or intelligence agencies and that the data present is not the only one in their possession.
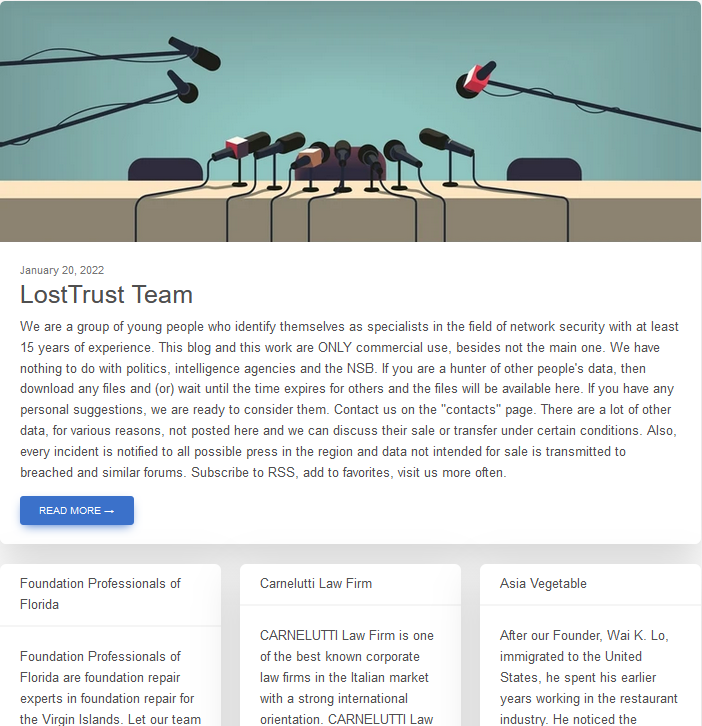
As a rule, they report every incident to as much press as possible in the affected region, while data not intended for sale is passed on to designated forums.
LostTrust cyber attacks
In Hackmanac we analyzed and classified a total of 53 cyber attacks from the group.
Based on what the gang reported in their DLS, 44 of these attacks occurred in the period January-June 2023 and 9 at the end of 2022.
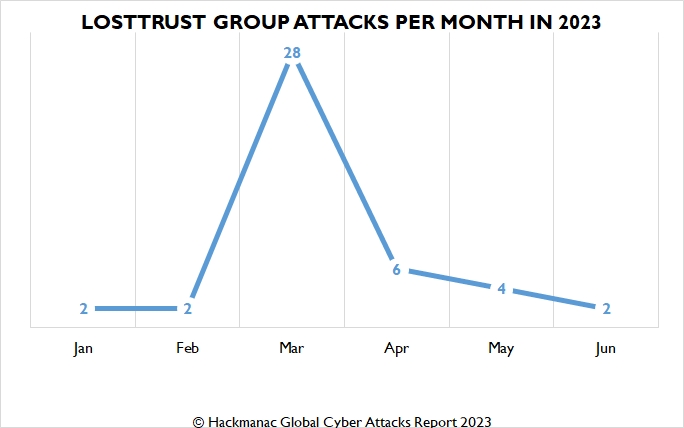
The average in 2013 is 7.3 cyber attacks per month, but in March we recorded a considerable spike of 28 events.
However, it is important to underline that precise attribution of when the attacks occurred is not easy as the group does not use precise dates but only relative dates.
Main victims
Manufacturing and Professional / Scientific / Technical sectors are the group’s main victims (each accounting for 19% of the total number of attacks).
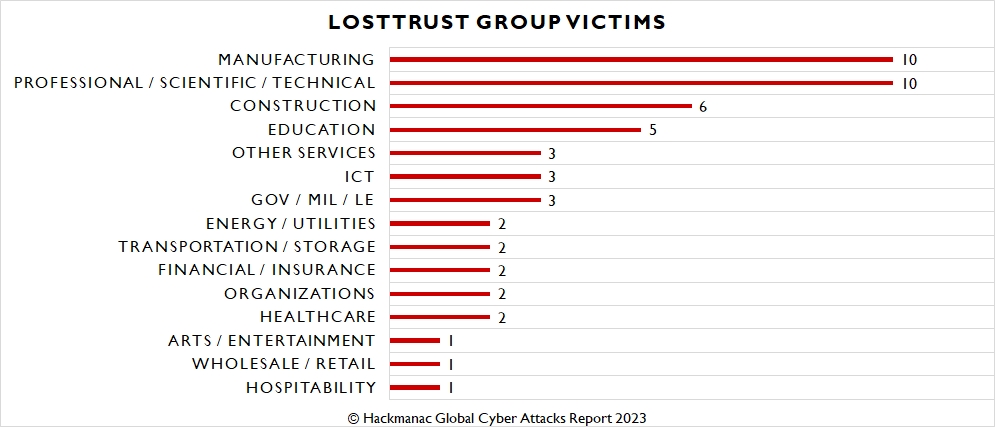
This is followed by Construction (11%), Education (9%), Other Services, ICT, Gov / Mil / LE (each 5%) and other sectors impacted to a lesser extent.
Most targeted countries
USA (71% of total attacks) and Italy (7%) are the most targeted countries by LostTrust group.
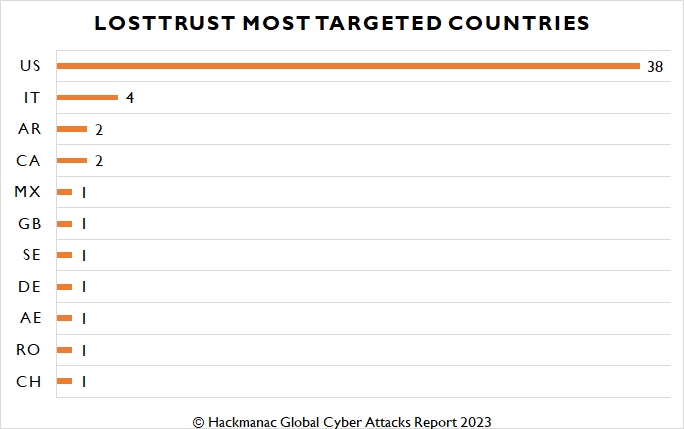
Argentina and Canada (4% each) are other countries affected by the group, followed by other states impacted to a lesser extent.
Probably a rebrand
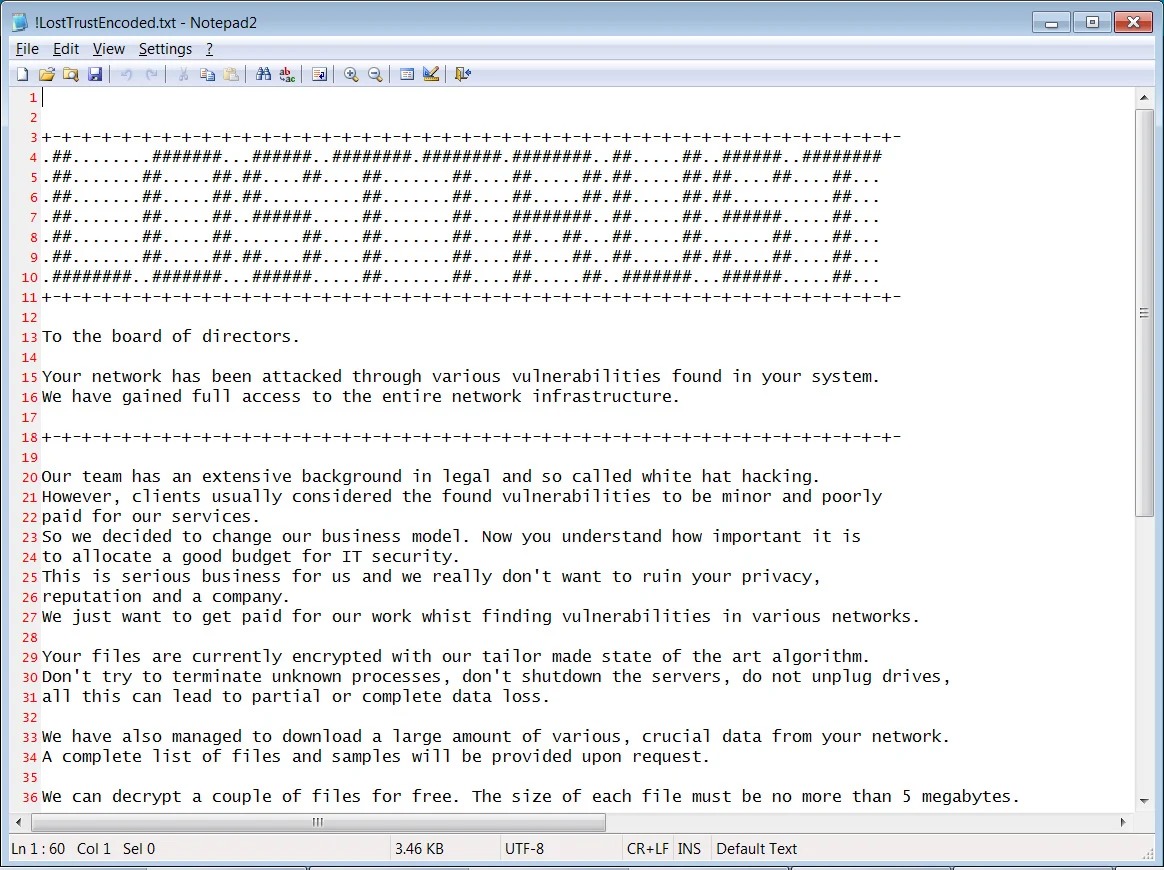
LostTrust group is believed to be a rebrand of Metaencryptor gang.
MetaEncryptor is a ransomware operation that started their activities in August 2022 and didn’t post anything after July 2023, for a total amount of 13 victims.
In September a new DLS was launched for Lost Trust which, as we reported to Bleeping Computer, uses the same template and bio as MetaEncryptor.
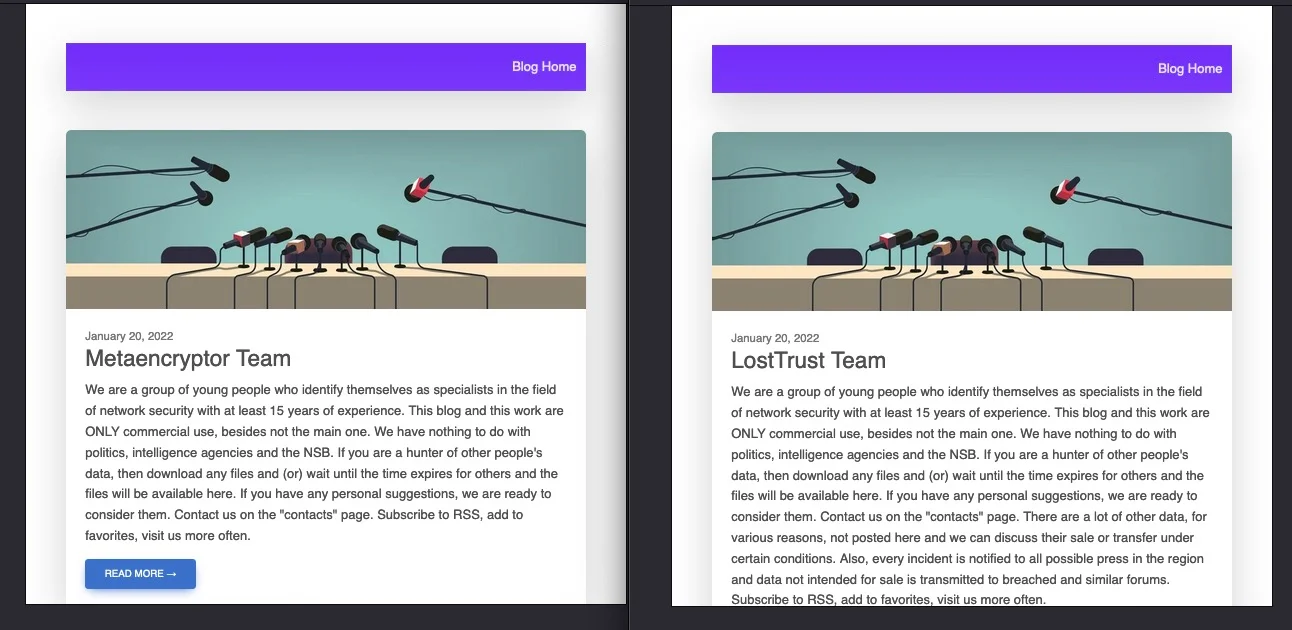
SentinelOne supports this thesis too, also showing similarities in the ransom note construction and in the malware samples of two other gangs, Mindware and SFile, indicating that LostTrust could probably be an evolution of these two groups.
Furthermore, we detected that Lost Trust attacked 7 targets previously affected by 4 other ransomware groups: Medusa, Royal, LockBit 3.0, and NoEscape.
While waiting for further developments, we recommend caution as always.
Stay cyber safe!
Latest news
HACKS OF TODAY 02/05/2024
Today's HOT includes 22 victims by the notorious BianLian, Ra World, RansomHub, INC Ransom, Ransomware Blog, Rhysida, Akira and Underground Team gangs. The average Cyber...
Read MoreHACKS OF TODAY 30/04/2024 – 01/05/2024
Today's HOT includes 29 victims by the notorious LockBit 3.0, BlackBasta, Embargo, Medusa, Akira, Play, Snatch, Everest, Qilin, Cl0p and RansomHub gangs. The average Cyber...
Read MoreHACKS OF TODAY 27-28-29/04/2024
Today's HOT includes 30 ransomware victims by the notorious Apos, Play, LockBit 3.0, RansomHub, INC Ransom, Black Suit, Eraleig, Qiulong, Hunters International, 8Base, BlackBasta and Space Bears...
Read More