news
HACKS OF TODAY 07/07/2023

Today’s HOT includes 31 victims:
20 ransomware and 2 supply chain attacks by the notorious BianLian, LockBit 3.0,Play, Rhysida and Akira gangs and 9 zero-day exploit by Cl0p.
The average Cyber Risk Factor is 3.8.
Read below the full list.
Disclaimer:
Data are collected from public info published on Dark Web.
The Cyber Risk factor is calculated on cyber attacks’ impact based on available data.
It shows the severity of an event: 1 = low, 5 = critical
CARVIN SOFTWARE
Victim website: | carvinsoftware.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 1,8 TB |
Exfiltrated data type: | Personal data of employees and clients of over 50 staffing companies |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
UNITED BANK
Victim website: | bankwithunited.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
ENERGY TRANSFER
Victim website: | energytransfer.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
CADENCE BANK
Victim website: | cadencebank.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
TD AMERITRADE
Victim website: | tdameritrade.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
DE LA RUE
Victim website: | delarue.com |
Victim country: | United Kingdom |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 5 |
PINNERGY
Victim website: | pinnergy.com |
Victim country: | USA |
Attacker name: | Akira |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 55 GB |
Exfiltrated data type: | Contracts, projects, employee personal information, and confidential documents |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
COLUMBIA HOUSING AUTHORITY
Victim website: | chasc.org |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | Access credentials |
Ransom deadline: | 25th Jul 23 |
Cyber Risk Factor: | 4 |
GAC EGYPT
Victim website: | gacegypt.net |
Victim country: | Egypt |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 452 GB |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 23rd Jul 23 |
Cyber Risk Factor: | 4 |
ENCORE PRO STAFFING
Victim website: | encoreprostaffing.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Supply chain attack |
Ransom demand: | N/A |
Exfiltrated data amount: | 30 GB |
Exfiltrated data type: | Personal records and databases |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
CENTEX PERSONNEL
Victim website: | centexpersonnel.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Supply chain attack |
Ransom demand: | N/A |
Exfiltrated data amount: | 17 GB |
Exfiltrated data type: | Personal records and databases |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
ELLA INSURANCE BROKERAGE
Victim website: | ellabrokerage.com |
Victim country: | USA |
Attacker name: | BianLian |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | 288 GB |
Exfiltrated data type: | Accounting, Personal data, financial data, SQL databases |
Leaked data: | 100% of the exfiltrated data |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
NST ATTORNEYS AT LAW
Victim website: | nstlaw.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, IDs, SSNs, insurance, contracts, lawsuits and etc |
Leaked data: | / |
Ransom deadline: | 12th Jul 23 |
Cyber Risk Factor: | 4 |
UNIQUIFY
Victim website: | uniquify.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, a lot of technical documentation, contracts and etc |
Leaked data: | / |
Ransom deadline: | 12th Jul 23 |
Cyber Risk Factor: | 4 |
LAWER SPA
Victim website: | lawer.com |
Victim country: | Italy |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, contracts, finance and etc |
Leaked data: | / |
Ransom deadline: | 13th Jul 23 |
Cyber Risk Factor: | 4 |
KENYA BUREAU OF STANDARDS
Victim website: | kebs.org |
Victim country: | USA |
Attacker name: | Rhysida |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | Auction |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Miscellaneous including PII documents |
Leaked data: | Sample with proof of the exfiltrated data |
Ransom deadline: | 14th Jul 23 |
Cyber Risk Factor: | 4 |
NEW ERA TECHNOLOGY
Victim website: | neweratech.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
WOLTERS KLUWER
Victim website: | wolterskluwer.com |
Victim country: | Netherlands |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
NETSCOUT
Victim website: | netscout.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
PAYCOR
Victim website: | paycor.com |
Victim country: | USA |
Attacker name: | Cl0p |
Attacker class: | Cybercrime |
Attack technique: | Zero-Day Vulnerability in MOVEit (CVE-2023-34362) |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | N/A |
Cyber Risk Factor: | 4 |
BETA
Victim website: | betalandservices.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 22nd Jul 23 |
Cyber Risk Factor: | 3 |
CLS
Victim website: | cls-group.com |
Victim country: | USA |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | Access credentials |
Ransom deadline: | 20th Jul 23 |
Cyber Risk Factor: | 3 |
SIEGFRIED RHEIN
Victim website: | siegfried.com.mx |
Victim country: | Mexico |
Attacker name: | LockBit 3.0 |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | N/A |
Leaked data: | / |
Ransom deadline: | 20th Jul 23 |
Cyber Risk Factor: | 3 |
CAPACITY
Victim website: | capacityllc.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, IDs, contracts, tax, and etc |
Leaked data: | / |
Ransom deadline: | 12th Jul 23 |
Cyber Risk Factor: | 3 |
SAFETY NETWORK
Victim website: | safetynetworkinc.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, contracts, finance, and etc |
Leaked data: | / |
Ransom deadline: | 12th Jul 23 |
Cyber Risk Factor: | 3 |
GENEVA SOFTWARE
Victim website: | genevasi.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, contracts, taxes, finance and etc |
Leaked data: | / |
Ransom deadline: | 12th Jul 23 |
Cyber Risk Factor: | 3 |
MUJI EUROPE HOLDINGS LIMITED
Victim website: | muji.eu |
Victim country: | United Kingdom |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, contracts, finance and etc |
Leaked data: | / |
Ransom deadline: | 12th Jul 23 |
Cyber Risk Factor: | 3 |
BETTY LOU’S
Victim website: | bettylousinc.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, contracts, and etc |
Leaked data: | / |
Ransom deadline: | 13th Jul 23 |
Cyber Risk Factor: | 3 |
STAR ISLAND RESORT
Victim website: | star-island.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, HR, contracts, finance and etc |
Leaked data: | / |
Ransom deadline: | 13th Jul 23 |
Cyber Risk Factor: | 3 |
INDIANA DIMENSION
Victim website: | indianadimension.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, passports, HR, contracts, finance and etc |
Leaked data: | / |
Ransom deadline: | 13th Jul 23 |
Cyber Risk Factor: | 3 |
LAZER TOW
Victim website: | lazertow.com |
Victim country: | USA |
Attacker name: | Play |
Attacker class: | Cybercrime |
Attack technique: | Ransomware |
Ransom demand: | N/A |
Exfiltrated data amount: | N/A |
Exfiltrated data type: | Private and personal confidential data, clients and employee documents, clients base, passports, contracts, finance and etc |
Leaked data: | / |
Ransom deadline: | 13th Jul 23 |
Cyber Risk Factor: | 3 |
Stay safe!
Hackmanac Team
Latest news
HACKS OF TODAY 11-12-13-14-15/05/2024
Today's HOT includes 94 victims by the notorious Hunters International, Rhysida, BianLIan, dAn0n, Qilin, Embargo, Everest, INC Ransom, Black Suit, Monti, Akira, RansomHub, Zero Tolerance...
Read MoreHACKS OF TODAY 09-10/05/2024
Today's HOT includes 94 victims by the notorious Hunters International, Rhysida, BianLIan, dAn0n, Qilin, Embargo, Everest, INC Ransom, Black Suit, Monti, Akira, RansomHub, Zero Tolerance...
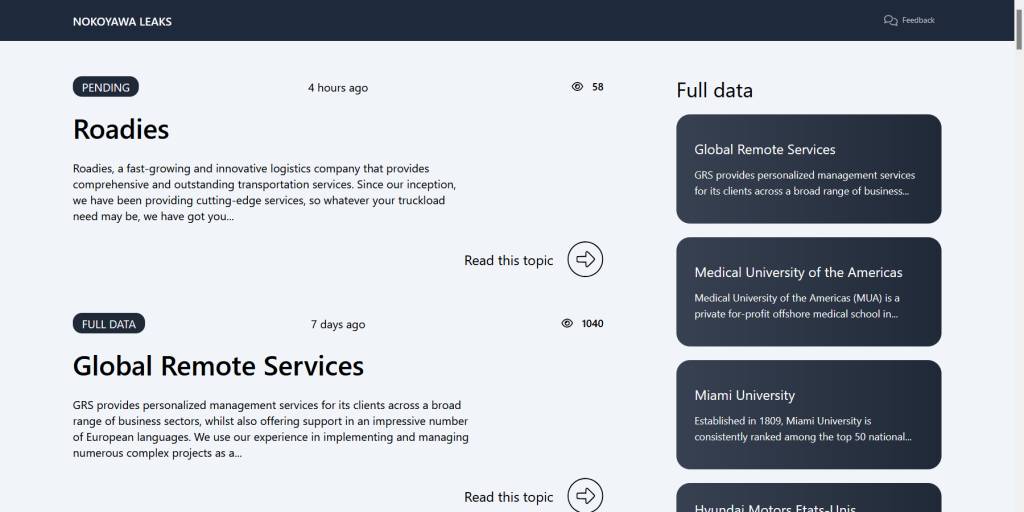
Read MoreOPERATION CRONOS AND THE MAGNITUDE OF THE LOCKBIT REACTION: 119 PREVIOUSLY UNCLAIMED VICTIMS WORLDWIDE
In recent days, following the events involving the LockBit criminal group and law enforcement with Operation Cronos, the hacker group decided to go all in...
Read More